What is Zero Trust Network Access
Introduction
You might have heard the term Zero Trust Network Access, or ZTNA, popping up in conversations about cybersecurity. But what does it really mean? In simple terms, it’s a modern way to protect your network by assuming no one is trustworthy by default—not even people inside your company. This approach helps keep your data safe in a world where cyber threats are constantly evolving.
We all want to keep our information secure, especially with more people working remotely and using cloud services. Zero Trust Network Access changes how we think about security by verifying every user and device before allowing access. In this article, I’ll explain what ZTNA is, why it matters, and how it works to protect your network.
What is Zero Trust Network Access?
Zero Trust Network Access is a security model that requires strict verification for every user and device trying to access a network or application. Unlike traditional security models that trust users inside the network perimeter, ZTNA assumes no one is trustworthy until proven otherwise.
Key Concepts of ZTNA
- Never trust, always verify: Every access request is checked, regardless of where it comes from.
- Least privilege access: Users get only the minimum access they need to do their job.
- Continuous monitoring: Access permissions are constantly reviewed and adjusted based on behavior and risk.
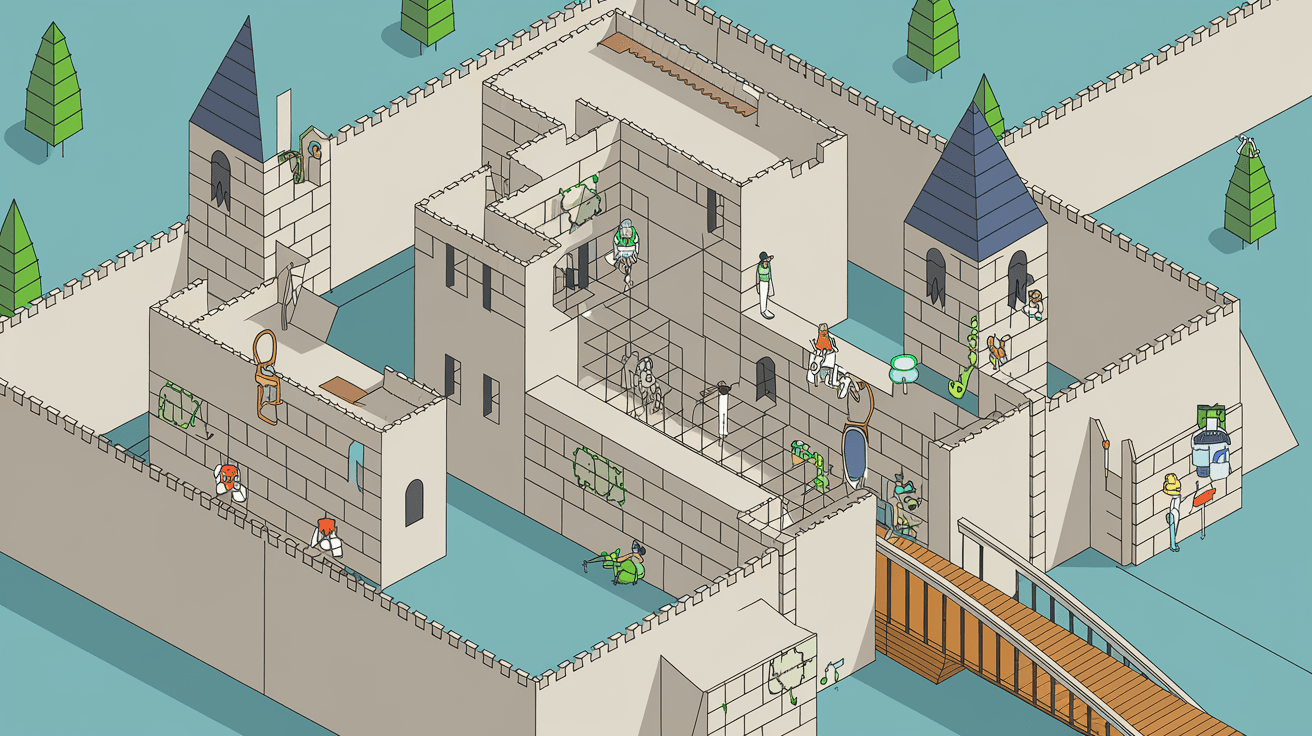
ZTNA replaces the old "castle and moat" approach, where everything inside the network was trusted. Instead, it treats every access attempt as if it’s coming from an untrusted source, even if the user is inside the company.
Why Zero Trust Network Access is Important
With more people working remotely and using cloud applications, traditional network security is no longer enough. Cyber attackers have become more sophisticated, and breaches often happen because attackers gain access through trusted users or devices.
Challenges with Traditional Network Security
- Perimeter-based security: Relies on firewalls and VPNs that trust users once inside the network.
- Increased remote work: Makes it harder to control who accesses the network.
- Cloud adoption: Data and apps are spread across multiple environments, making perimeter security less effective.
ZTNA addresses these challenges by verifying every access request, no matter where it originates. This reduces the risk of unauthorized access and limits the damage if a breach happens.
How Zero Trust Network Access Works
ZTNA uses several technologies and principles to secure access. Here’s a simple breakdown of how it works:
Step 1: User and Device Authentication
Before granting access, ZTNA verifies who you are and checks the security status of your device. This can include:
- Passwords or multi-factor authentication (MFA)
- Device health checks (e.g., antivirus status, software updates)
- User behavior analysis
Step 2: Access Policy Enforcement
Once authenticated, ZTNA applies strict access policies based on the user’s role, device, location, and other factors. These policies ensure users only access what they need.
Step 3: Secure Connection
Instead of giving users full network access, ZTNA creates a secure, encrypted connection directly to the specific application or resource. This limits exposure and reduces the attack surface.
Step 4: Continuous Monitoring and Adaptation
ZTNA continuously monitors user activity and device health. If anything suspicious happens, access can be adjusted or revoked immediately.
Benefits of Zero Trust Network Access
Implementing ZTNA brings many advantages for organizations of all sizes. Here are some key benefits:
- Improved security: Reduces the risk of data breaches by verifying every access request.
- Better user experience: Users get seamless access to applications without complex VPN setups.
- Simplified management: Centralized control over who accesses what, with real-time monitoring.
- Supports remote work: Securely connects users from anywhere without relying on traditional network perimeters.
- Limits lateral movement: If an attacker gains access, ZTNA restricts their ability to move across the network.
ZTNA vs. VPN: What’s the Difference?
Many people wonder how Zero Trust Network Access compares to Virtual Private Networks (VPNs), which have been the standard for remote access.
| Feature | VPN | Zero Trust Network Access (ZTNA) |
| Access Scope | Full network access | Access to specific apps/resources |
| Trust Model | Trusts users inside the network | Never trusts, always verifies |
| Security Level | Lower, vulnerable to lateral movement | Higher, limits attack surface |
| User Experience | Can be slow and complex | More seamless and flexible |
| Management Complexity | Harder to manage at scale | Centralized and policy-driven |
ZTNA offers a more secure and user-friendly alternative to VPNs, especially for modern cloud environments and remote workforces.
Implementing Zero Trust Network Access
If you’re considering ZTNA for your organization, here are some steps to get started:
1. Assess Your Current Network
Understand your existing security setup, applications, and user access patterns. Identify critical assets and potential vulnerabilities.
2. Define Access Policies
Create clear policies based on user roles, device types, and risk levels. Decide who needs access to what and under which conditions.
3. Choose the Right ZTNA Solution
Look for solutions that integrate well with your existing infrastructure and support multi-factor authentication, device checks, and continuous monitoring.
4. Start with a Pilot Program
Test ZTNA with a small group of users or applications to identify challenges and adjust policies.
5. Train Your Team
Educate employees about the new access model and security best practices to ensure smooth adoption.
6. Monitor and Improve
Continuously review access logs and user behavior to refine policies and respond to threats quickly.
Common Challenges with Zero Trust Network Access
While ZTNA offers many benefits, it’s not without challenges:
- Complexity: Designing and managing granular access policies can be complicated.
- Integration: Ensuring compatibility with legacy systems and cloud apps requires planning.
- User Resistance: Changes in access procedures may cause initial pushback.
- Cost: Implementing ZTNA solutions can require investment in new tools and training.
Addressing these challenges requires careful planning, clear communication, and ongoing support.
Real-World Examples of Zero Trust Network Access
Many organizations have adopted ZTNA to improve their security posture:
- Financial institutions: Use ZTNA to protect sensitive customer data and comply with regulations.
- Healthcare providers: Secure patient records while enabling remote access for doctors.
- Technology companies: Protect intellectual property and support flexible work environments.
- Government agencies: Enhance security for critical infrastructure and citizen services.
These examples show how ZTNA adapts to different industries and security needs.
Conclusion
Zero Trust Network Access is changing the way we think about network security. By verifying every user and device before granting access, it helps protect your data from modern cyber threats. Whether you’re managing a small business or a large enterprise, ZTNA offers a smarter, safer way to control access in today’s digital world.
As remote work and cloud services continue to grow, relying on old security models is no longer enough. Implementing Zero Trust Network Access can improve your security, simplify management, and provide a better experience for users. If you want to keep your network safe, understanding and adopting ZTNA is a step in the right direction.
FAQs
What is the main goal of Zero Trust Network Access?
The main goal is to secure network access by verifying every user and device before granting access, reducing the risk of unauthorized entry and limiting potential damage from breaches.
How does ZTNA improve security compared to traditional VPNs?
ZTNA limits access to specific applications rather than the whole network, continuously verifies users, and applies strict policies, making it harder for attackers to move laterally.
Can Zero Trust Network Access work with cloud applications?
Yes, ZTNA is designed to secure access to cloud apps and services, making it ideal for modern hybrid and cloud environments.
Is Zero Trust Network Access difficult to implement?
It can be complex due to policy design and integration needs, but starting with a pilot and clear planning helps ease the process.
Does ZTNA support remote work?
Absolutely. ZTNA provides secure, seamless access for remote users without relying on traditional network perimeters.





