What is Wireless Intrusion Detection System
Introduction
You rely on wireless networks every day, whether at home, work, or public places. But have you ever wondered how these networks stay safe from hackers or unauthorized users? That’s where a Wireless Intrusion Detection System (WIDS) comes in. It helps protect your wireless network by spotting threats before they cause harm.
In this article, I’ll explain what a Wireless Intrusion Detection System is, how it works, and why it’s important for your network security. You’ll also learn about its key features and how it differs from other security tools. Let’s dive in and make your wireless world safer.
What is a Wireless Intrusion Detection System?
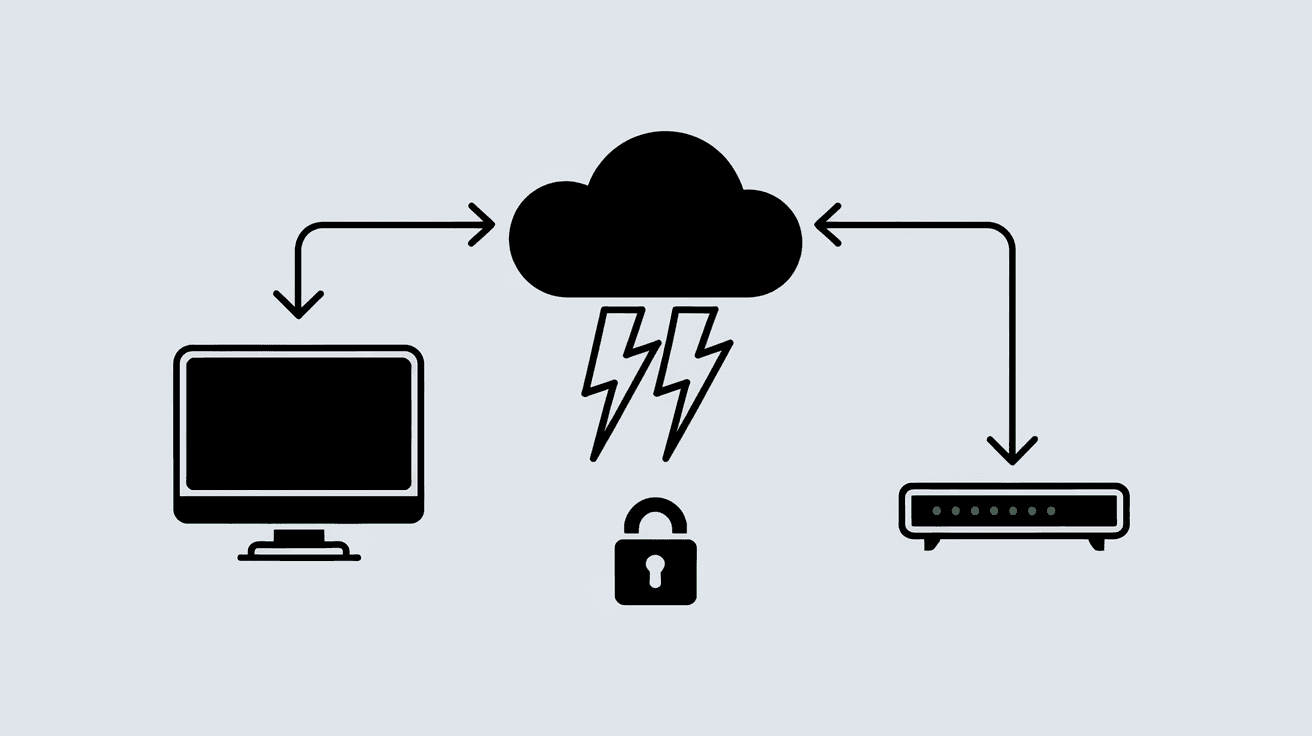
A Wireless Intrusion Detection System (WIDS) is a security tool designed to monitor wireless networks for suspicious activity. It detects unauthorized access, attacks, or unusual behavior that could threaten the network’s safety. Unlike traditional intrusion detection systems that focus on wired networks, WIDS specifically targets wireless signals.
WIDS works by scanning the airwaves for wireless traffic and analyzing it for signs of intrusion. It can identify rogue devices, unauthorized access points, and hacking attempts. When it detects a threat, it alerts network administrators so they can take action quickly.
Key Functions of WIDS
- Monitoring wireless traffic to detect anomalies.
- Identifying unauthorized devices trying to connect.
- Detecting attacks like denial-of-service or spoofing.
- Alerting administrators about potential threats.
- Logging events for further analysis.
By continuously watching your wireless environment, WIDS helps keep your network secure from invisible dangers.
How Does a Wireless Intrusion Detection System Work?
A WIDS uses sensors or access points placed around the wireless network area. These sensors capture wireless signals and send data to a central system for analysis. The system compares the data against known threat patterns and normal network behavior.
Here’s a simple breakdown of the process:
- Data Collection: Sensors scan wireless channels to capture packets.
- Analysis: The system inspects packets for suspicious signs.
- Detection: It identifies threats like rogue access points or attacks.
- Alerting: Notifications are sent to administrators.
- Response: Admins investigate and respond to threats.
Types of Detection Methods
- Signature-Based Detection: Looks for known attack patterns.
- Anomaly-Based Detection: Spots unusual behavior compared to normal traffic.
- Specification-Based Detection: Uses predefined rules about normal operations.
Each method helps WIDS catch different types of threats, making the system more effective.
Why is Wireless Intrusion Detection Important?
Wireless networks are everywhere, but they come with risks. Unlike wired networks, wireless signals travel through the air, making them easier to intercept or attack. Without proper protection, hackers can steal data, disrupt services, or gain unauthorized access.
WIDS is crucial because it:
- Protects sensitive data from being intercepted.
- Prevents unauthorized access to your network.
- Detects attacks early to minimize damage.
- Supports compliance with security regulations.
- Improves overall network security posture.
For businesses and individuals, WIDS adds an essential layer of defense against wireless threats.
Key Features of Wireless Intrusion Detection Systems
When choosing a WIDS, it’s helpful to know the features that make these systems effective. Here are some common features you’ll find:
- Real-Time Monitoring: Continuous scanning of wireless traffic.
- Rogue Device Detection: Identifies unauthorized access points or clients.
- Attack Detection: Recognizes common wireless attacks like deauthentication or man-in-the-middle.
- Location Tracking: Pinpoints where rogue devices are physically located.
- Reporting and Alerts: Sends detailed notifications to admins.
- Integration: Works with other security tools like firewalls or SIEM systems.
- Scalability: Supports networks of different sizes, from small offices to large enterprises.
These features help you stay ahead of threats and maintain a secure wireless environment.
Differences Between WIDS and Wireless Intrusion Prevention System (WIPS)
You might hear about Wireless Intrusion Prevention Systems (WIPS) alongside WIDS. While they sound similar, they serve different purposes.
- WIDS focuses on detecting threats and alerting administrators.
- WIPS goes a step further by automatically blocking or stopping threats.
Think of WIDS as a security camera that watches for trouble, while WIPS is like a security guard who intervenes when something suspicious happens.
Many organizations use both systems together for stronger protection.
Common Wireless Threats Detected by WIDS
Wireless networks face various threats that WIDS can detect, including:
- Rogue Access Points: Unauthorized devices pretending to be legitimate network points.
- Evil Twin Attacks: Fake access points set up to steal user data.
- Denial of Service (DoS): Attacks that flood the network to disrupt service.
- Man-in-the-Middle Attacks: Intercepting communication between devices.
- MAC Spoofing: Faking device addresses to gain access.
- Packet Sniffing: Capturing wireless data packets to steal information.
By identifying these threats early, WIDS helps prevent serious security breaches.
How to Implement a Wireless Intrusion Detection System
Setting up a WIDS involves several steps to ensure it works effectively:
- Assess Your Network: Understand your wireless environment and risks.
- Choose the Right WIDS: Select a system that fits your network size and needs.
- Deploy Sensors: Place sensors strategically to cover all wireless areas.
- Configure Detection Rules: Set up rules based on your network’s normal behavior.
- Monitor Alerts: Regularly check notifications and logs.
- Respond to Threats: Investigate and act on any detected intrusions.
- Update Regularly: Keep the system updated with the latest threat signatures.
Proper implementation ensures your WIDS provides reliable protection.
Challenges and Limitations of Wireless Intrusion Detection Systems
While WIDS is powerful, it has some challenges:
- False Positives: Sometimes normal activity is flagged as a threat.
- Coverage Gaps: Sensors might miss signals in some areas.
- Complex Setup: Requires technical knowledge to configure properly.
- Resource Intensive: Continuous monitoring can demand network and system resources.
- Encrypted Traffic: Encrypted wireless traffic can be harder to analyze.
Understanding these limitations helps you manage expectations and improve your security strategy.
Future Trends in Wireless Intrusion Detection
Wireless security is evolving with new technologies and threats. Here are some trends shaping the future of WIDS:
- AI and Machine Learning: Using smart algorithms to improve threat detection accuracy.
- Integration with IoT Security: Protecting the growing number of wireless IoT devices.
- Cloud-Based WIDS: Offering scalable and flexible monitoring solutions.
- Enhanced Automation: Faster response and remediation without human intervention.
- Support for New Wireless Standards: Adapting to Wi-Fi 6E and beyond.
These advancements will make wireless networks safer and easier to protect.
Conclusion
Now you know that a Wireless Intrusion Detection System is a vital tool for keeping your wireless network secure. It watches for unauthorized devices and attacks, helping you stop threats before they cause damage. Whether you manage a home network or a large business, WIDS adds an important layer of defense.
By understanding how WIDS works, its features, and how to implement it, you can better protect your wireless environment. As wireless technology grows, staying ahead of threats with tools like WIDS becomes even more important. Take steps today to secure your wireless world and enjoy safer connections.
FAQs
What is the main purpose of a Wireless Intrusion Detection System?
The main purpose of a WIDS is to monitor wireless networks for unauthorized access and attacks. It detects suspicious activity and alerts administrators to protect the network from threats.
How does WIDS differ from a Wireless Intrusion Prevention System?
WIDS detects and alerts about wireless threats, while WIPS actively blocks or prevents those threats. WIPS adds a layer of automatic response to the detection capabilities of WIDS.
Can WIDS detect rogue access points?
Yes, WIDS can identify rogue access points that try to connect to your network without permission. This helps prevent unauthorized devices from compromising your wireless security.
Is WIDS effective against all wireless attacks?
WIDS is effective against many common wireless attacks like spoofing and denial-of-service, but it may have limitations with encrypted traffic or very sophisticated attacks.
Do I need technical skills to set up a WIDS?
Setting up a WIDS can be complex and often requires some technical knowledge to configure sensors, detection rules, and respond to alerts effectively.





