What is Whaling Phishing
Introduction
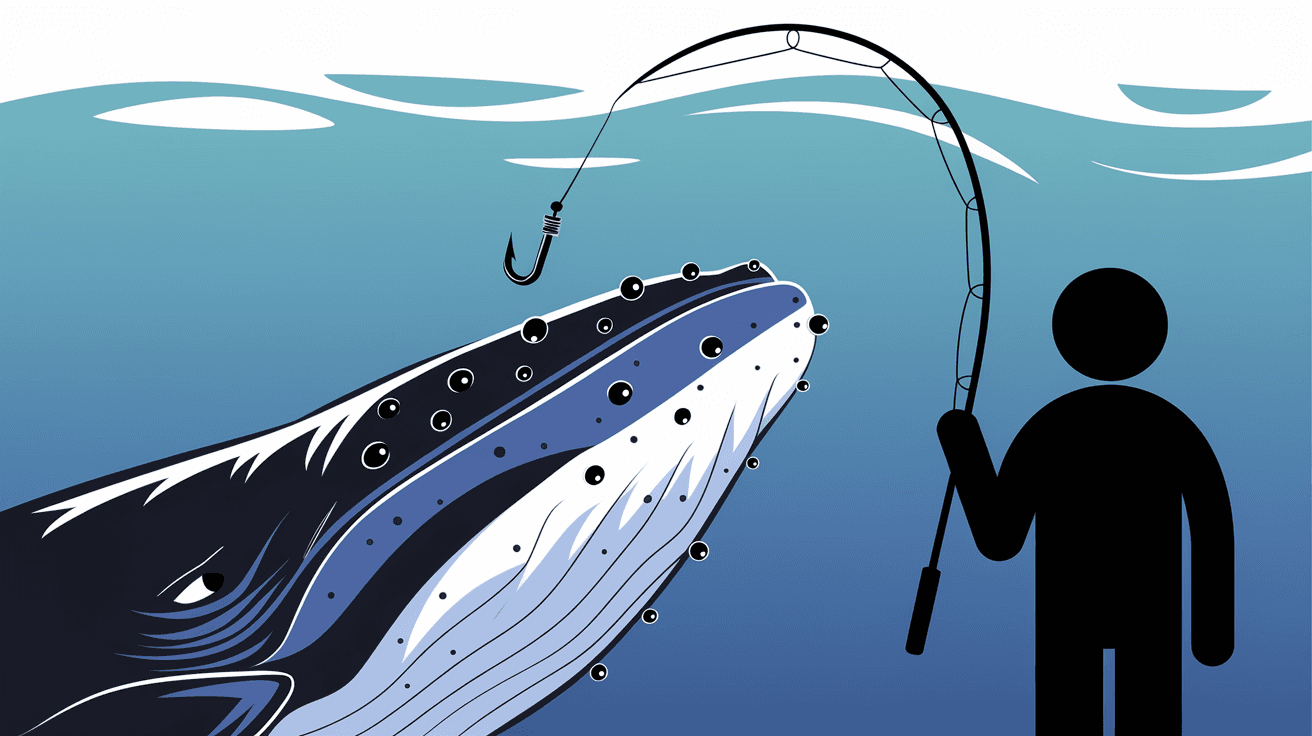
You might have heard about phishing scams, but have you come across the term "whaling phishing"? It’s a special kind of cyberattack that targets important people like CEOs or executives. These attacks are more focused and dangerous because they aim to steal sensitive information or money from high-level targets.
In this article, I’ll explain what whaling phishing is, how it works, and why it’s different from regular phishing. You’ll also learn how to spot these attacks and protect yourself or your organization from falling victim to them.
What is Whaling Phishing?
Whaling phishing is a type of phishing attack that specifically targets high-profile individuals within an organization. These targets are usually senior executives, such as CEOs, CFOs, or other decision-makers. The goal is to trick them into revealing confidential information or authorizing financial transactions.
Unlike regular phishing, which often casts a wide net, whaling is highly targeted and personalized. Attackers spend time researching their victims to make their messages look genuine and convincing.
Key Characteristics of Whaling Phishing
- Targets high-ranking individuals or executives.
- Uses personalized and well-researched messages.
- Often involves urgent or sensitive requests.
- Aims to steal sensitive data or money.
- Uses email or other communication channels.
How Does Whaling Phishing Work?
Whaling phishing attacks usually start with thorough research. Attackers gather information about their target from social media, company websites, and news articles. This helps them craft believable emails or messages.
Once the attacker has enough information, they send a message that looks like it comes from a trusted source, such as a business partner or another executive. The message often contains urgent requests, like approving a wire transfer or sharing confidential files.
If the target falls for the scam, the attacker can gain access to sensitive data or cause financial loss.
Steps in a Typical Whaling Attack
- Research: Gather detailed information about the target.
- Crafting the Message: Create a personalized email or message.
- Delivery: Send the message via email or other platforms.
- Exploitation: Victim responds by sharing information or authorizing transactions.
- Attack Execution: Attacker uses the stolen data or money.
Examples of Whaling Phishing Attacks
Whaling phishing has been behind some major cyberattacks in recent years. Here are a few examples to help you understand how serious these attacks can be:
- CEO Fraud: An attacker impersonates a CEO and sends an email to the finance department asking for a large wire transfer. The finance team, believing the request is genuine, transfers the money to the attacker’s account.
- Fake Legal Requests: An attacker pretends to be a lawyer or legal advisor and asks an executive to review confidential documents or share sensitive information.
- Vendor Impersonation: The attacker poses as a trusted vendor and requests updated payment details or invoices.
These examples show how attackers exploit trust and authority to trick their victims.
Why is Whaling Phishing Dangerous?
Whaling phishing is dangerous because it targets people who have access to critical company resources. When an executive’s account is compromised, the attacker can cause significant damage, including:
- Financial loss through fraudulent transactions.
- Exposure of sensitive company data.
- Damage to the company’s reputation.
- Legal and regulatory consequences.
Since these attacks are highly targeted and personalized, they are harder to detect and prevent than regular phishing scams.
How to Recognize Whaling Phishing Attempts
Recognizing whaling phishing attempts can save you and your organization from serious harm. Here are some signs to watch for:
- Unexpected Requests: Be cautious if you receive urgent or unusual requests, especially involving money or confidential information.
- Unusual Sender Address: Check the sender’s email address carefully. Attackers often use addresses that look similar but are slightly different.
- Poor Grammar or Spelling: Although whaling emails are usually well-crafted, some may still contain errors.
- Requests for Secrecy: Be wary if the message asks you to keep the request confidential.
- Pressure to Act Quickly: Attackers often create a sense of urgency to prevent you from thinking carefully.
How to Protect Yourself and Your Organization
Protecting against whaling phishing requires a combination of technology, awareness, and policies. Here are some effective strategies:
Employee Training
- Teach employees, especially executives, how to recognize phishing and whaling attempts.
- Conduct regular simulated phishing exercises.
- Encourage reporting of suspicious emails.
Email Security Tools
- Use advanced email filters that detect phishing attempts.
- Implement multi-factor authentication (MFA) to secure accounts.
- Use encryption for sensitive communications.
Verification Procedures
- Establish clear protocols for approving financial transactions.
- Require verbal or secondary confirmation for unusual requests.
- Verify requests through a separate communication channel.
Regular Security Audits
- Conduct audits to identify vulnerabilities.
- Update security policies regularly.
- Monitor for unusual account activity.
The Role of Technology in Combating Whaling Phishing
Technology plays a crucial role in defending against whaling phishing attacks. Here are some tools and techniques commonly used:
- AI-Powered Email Filters: These tools analyze email content and sender behavior to detect phishing attempts.
- Behavioral Analytics: Systems monitor user behavior to spot anomalies that may indicate a compromised account.
- Threat Intelligence: Sharing information about new phishing tactics helps organizations stay ahead.
- Secure Email Gateways: These gateways block malicious emails before they reach users.
Using these technologies alongside employee training creates a strong defense.
What to Do If You Suspect a Whaling Phishing Attack
If you think you’ve received a whaling phishing email or your organization is under attack, act quickly:
- Do not respond to the suspicious message.
- Report the email to your IT or security team immediately.
- Change passwords and enable multi-factor authentication.
- Review recent transactions and account activity for unauthorized actions.
- Inform relevant stakeholders and, if necessary, law enforcement.
Quick action can minimize damage and help recover from the attack.
Conclusion
Whaling phishing is a serious cyber threat that targets high-level executives with personalized and convincing scams. Because these attacks focus on people with access to sensitive information and financial resources, they can cause significant harm.
By understanding how whaling phishing works and learning to recognize its signs, you can better protect yourself and your organization. Combining employee training, strong security policies, and advanced technology is the best way to defend against these sophisticated attacks. Stay alert and always verify unusual requests to keep your data and finances safe.
FAQs
What is the difference between phishing and whaling phishing?
Phishing targets a broad audience with generic messages, while whaling phishing focuses on high-profile individuals like executives with personalized, well-researched attacks.
Who are common targets of whaling phishing?
Common targets include CEOs, CFOs, senior executives, and other decision-makers with access to sensitive company information or financial resources.
How can I verify if an email is a whaling phishing attempt?
Check for unusual sender addresses, unexpected urgent requests, poor grammar, and pressure to act quickly. Always verify requests through a separate communication channel.
What should I do if I accidentally respond to a whaling phishing email?
Immediately inform your IT or security team, change your passwords, enable multi-factor authentication, and review your accounts for suspicious activity.
Are there tools to prevent whaling phishing attacks?
Yes, tools like AI-powered email filters, secure email gateways, behavioral analytics, and threat intelligence platforms help detect and block whaling phishing attempts.





