What is Whaling Attack
Introduction
You might have heard about phishing attacks, but have you come across the term "whaling attack"? If not, you're not alone. Whaling attacks are a specific type of cyberattack that targets high-profile individuals, like CEOs or executives, to steal sensitive information or money. Understanding what a whaling attack is can help you recognize the signs and protect yourself or your organization.
In this article, I’ll explain what a whaling attack is, how it works, and what makes it different from other cyber threats. You’ll also learn practical tips to defend against these attacks. Let’s dive in and explore this important topic together.
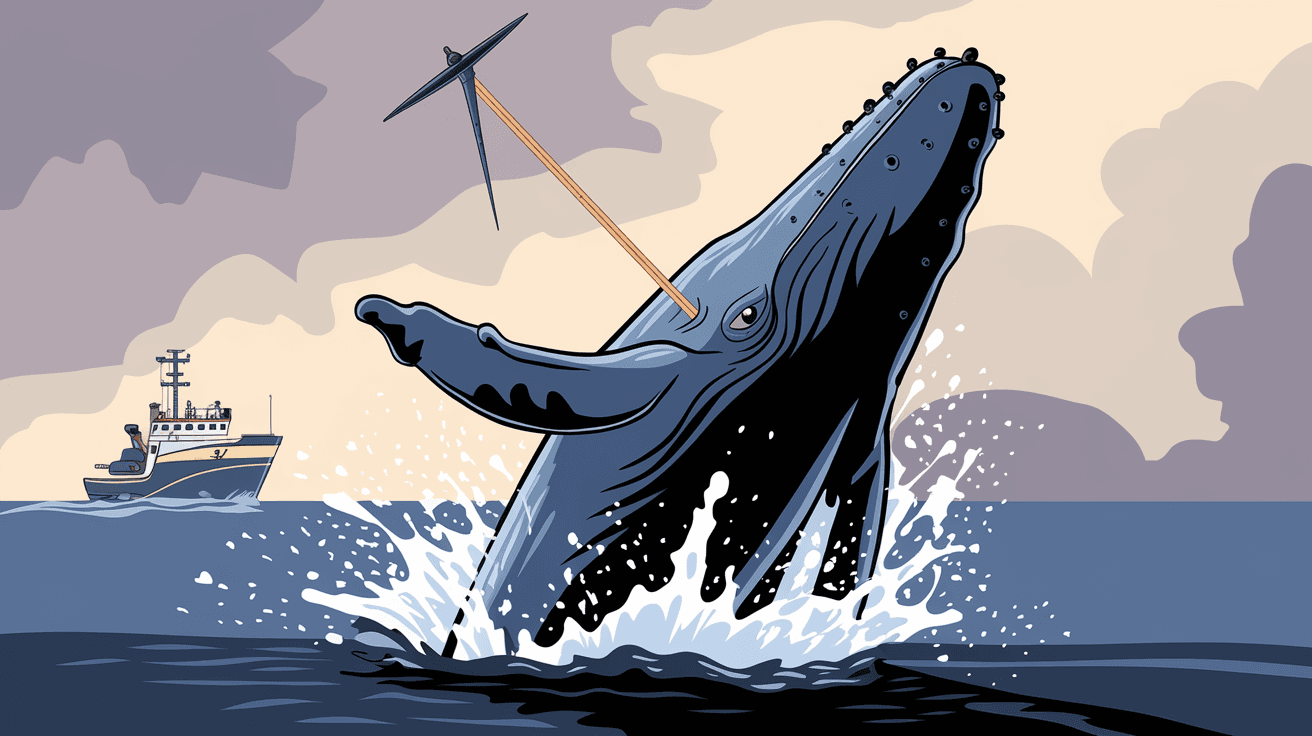
What is a Whaling Attack?
A whaling attack is a type of phishing scam that targets senior executives or important people in a company. Unlike regular phishing, which casts a wide net, whaling is very focused. The attackers “go after the big fish,” which is why it’s called whaling.
Here’s what makes whaling attacks unique:
- Targeted: Attackers research their victims carefully.
- High stakes: They aim for executives who have access to sensitive data or financial resources.
- Sophisticated: The emails or messages look very professional and believable.
Whaling attacks often involve emails that appear to come from trusted sources, like a company’s legal department or a business partner. The goal is to trick the executive into revealing confidential information or authorizing large money transfers.
How Does a Whaling Attack Work?
Whaling attacks follow a careful process. Attackers spend time gathering information about their target before launching the attack. Here’s a step-by-step look:
- Research: Attackers collect details about the executive, such as their role, contacts, and recent activities.
- Crafting the message: They create a convincing email or message tailored to the victim’s position.
- Sending the email: The message is sent, often appearing urgent or important.
- Exploitation: The victim is asked to provide sensitive data, click on a malicious link, or approve a financial transaction.
- Execution: Once the attacker gets what they want, they use it to steal money, data, or cause damage.
Because these emails are so personalized, they are harder to spot than regular phishing attempts. The attacker’s goal is to exploit trust and authority.
Examples of Whaling Attacks
Real-world examples help us understand how dangerous whaling attacks can be. Here are some notable cases:
- CEO Fraud: An attacker impersonated a company’s CEO and emailed the finance department, asking for a large wire transfer. The finance team complied, losing millions.
- Legal Threat Scam: Executives received emails that appeared to be from the legal team, warning about a lawsuit. The email asked for confidential documents, which were then stolen.
- Vendor Invoice Scam: Attackers sent fake invoices to CFOs, pretending to be trusted vendors. The invoices were paid without verification.
These examples show how attackers exploit authority and urgency to trick victims.
Why Are Whaling Attacks So Dangerous?
Whaling attacks are particularly dangerous because they target people with power and access. Here’s why they pose a big risk:
- High financial loss: Executives can authorize large payments quickly.
- Data breach risk: Sensitive company information can be stolen.
- Reputation damage: If confidential information leaks, it can harm the company’s image.
- Difficult to detect: The emails look legitimate and often bypass spam filters.
Because of these factors, whaling attacks can cause severe damage to businesses and individuals.
How to Recognize a Whaling Attack
Recognizing a whaling attack is the first step to stopping it. Here are some signs to watch for:
- Unexpected requests: Emails asking for urgent money transfers or confidential info.
- Unusual sender address: The email may look like it’s from a trusted source but has subtle differences.
- Poor grammar or spelling: While whaling emails are often professional, some may have mistakes.
- Pressure tactics: The message creates a sense of urgency or secrecy.
- Requests for unusual actions: Such as bypassing normal procedures or policies.
If you notice any of these signs, it’s best to verify the request through a different communication channel.
How to Protect Yourself and Your Organization
Protecting against whaling attacks requires a mix of technology and awareness. Here are practical steps you can take:
- Educate executives: Train leaders to recognize phishing and whaling attempts.
- Verify requests: Always confirm unusual requests by phone or in person.
- Use email filters: Advanced spam filters can catch suspicious emails.
- Implement multi-factor authentication: This adds a layer of security for sensitive accounts.
- Set up approval processes: Require multiple approvals for large transactions.
- Monitor accounts: Regularly check for unauthorized activity.
By combining these measures, you can reduce the risk of falling victim to a whaling attack.
The Role of Technology in Preventing Whaling Attacks
Technology plays a crucial role in defending against whaling attacks. Here are some tools and techniques commonly used:
- Email authentication protocols: Such as SPF, DKIM, and DMARC help verify sender identity.
- AI-based threat detection: Artificial intelligence can spot unusual email patterns.
- Security awareness platforms: These simulate phishing attacks to train employees.
- Data loss prevention (DLP): Systems that monitor and block sensitive data leaks.
- Incident response tools: Help quickly react to suspected attacks.
Using these technologies alongside human vigilance creates a strong defense.
What to Do If You Suspect a Whaling Attack
If you think you’ve received a whaling email or your organization is targeted, act quickly:
- Do not respond or click links: Avoid engaging with the suspicious email.
- Report it immediately: Notify your IT or security team.
- Change passwords: Especially if you clicked a link or shared information.
- Check financial accounts: Look for unauthorized transactions.
- Conduct a security review: Assess if any data was compromised.
Prompt action can limit damage and help prevent future attacks.
Conclusion
Whaling attacks are a serious threat that targets high-level individuals in organizations. Because these attacks are highly targeted and sophisticated, they can cause significant financial and reputational damage. Understanding what a whaling attack is and how it works helps you stay alert and protect yourself.
By recognizing the signs and following best practices, you can defend against these attacks. Remember, technology and awareness go hand in hand. Stay informed, verify suspicious requests, and keep your security measures up to date to keep the “big fish” safe.
FAQs
What is the difference between phishing and whaling attacks?
Phishing targets many people with generic emails, while whaling focuses on high-profile individuals like executives with personalized, convincing messages.
How can I verify if an email is a whaling attack?
Check for unusual requests, verify the sender’s email address, and confirm urgent or sensitive requests through a separate communication method.
Are whaling attacks only done via email?
Mostly yes, but attackers can also use phone calls or social media to impersonate executives and trick victims.
Can small businesses be targeted by whaling attacks?
Yes, any organization with valuable data or financial resources can be targeted, regardless of size.
What should I do if I accidentally respond to a whaling email?
Immediately inform your IT team, change your passwords, and monitor your accounts for suspicious activity.





