What is Watering Hole Attack
Introduction
You might have heard about cyberattacks like phishing or ransomware, but have you come across the term "watering hole attack"? It’s a sneaky way hackers target specific groups by infecting websites they often visit. Understanding this attack can help you stay safer online.
In this article, I’ll explain what a watering hole attack is, how it works, and what signs to watch for. You’ll also learn practical steps to protect yourself and your organization from falling victim to this cyber threat.
What Is a Watering Hole Attack?
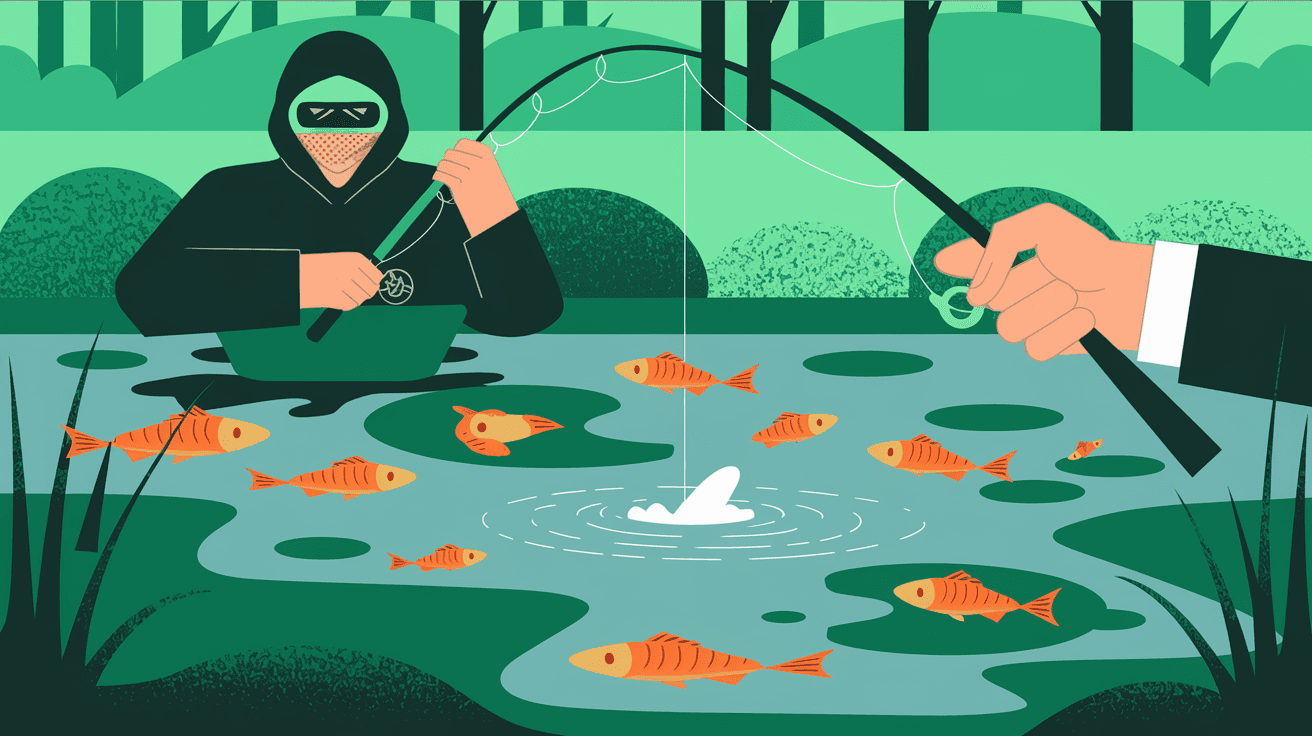
A watering hole attack is a type of cyberattack where hackers compromise websites that a particular group of people frequently visit. The goal is to infect these sites with malware, so when the target visits, their device gets infected.
The name comes from the idea of predators waiting near a watering hole to catch prey. Similarly, attackers wait for their victims to visit a trusted website to launch their attack.
How It Works
- Target Selection: Attackers research and identify websites popular with their intended victims.
- Website Compromise: They find vulnerabilities in these sites and inject malicious code.
- Infection: When victims visit the infected site, malware is silently downloaded or exploits a browser vulnerability.
- Data Theft or Control: The malware can steal sensitive information or give attackers control over the victim’s device.
This method is effective because users trust the websites they visit regularly, making them less cautious.
Examples of Watering Hole Attacks
Several high-profile watering hole attacks have made headlines in recent years. Here are some notable examples:
- The 2013 Council on Foreign Relations Attack: Hackers targeted this think tank’s website to infect visitors with malware, aiming at government officials and researchers.
- The 2017 CCleaner Attack: Attackers compromised the CCleaner software update server, infecting millions of users through a trusted software source.
- The 2021 Microsoft Exchange Watering Hole: Hackers targeted websites frequented by Microsoft Exchange administrators to spread malware and gain access to corporate networks.
These examples show how attackers use watering hole attacks to reach specific groups, such as government employees, IT professionals, or industry experts.
Why Are Watering Hole Attacks Dangerous?
Watering hole attacks are dangerous because they exploit trust and are hard to detect. Here’s why:
- Trusted Websites: Users don’t expect trusted sites to be harmful, so they don’t hesitate to visit them.
- Silent Infection: Malware often installs without any visible signs, making it hard to notice.
- Targeted Approach: Attackers focus on specific groups, increasing the chances of success.
- Difficult to Prevent: Since the attack happens on legitimate websites, traditional security tools may not catch it immediately.
Because of these factors, watering hole attacks can lead to serious data breaches, financial loss, and damage to reputation.
How to Recognize a Watering Hole Attack
Detecting a watering hole attack can be tricky, but there are some signs you can watch for:
- Unexpected Pop-Ups or Downloads: If a trusted site suddenly shows strange pop-ups or tries to download files, be cautious.
- Browser Warnings: Modern browsers often warn about suspicious websites or downloads.
- Slow or Unusual Website Behavior: If a site you visit regularly behaves oddly, it might be compromised.
- Antivirus Alerts: Your security software may detect malware after visiting a compromised site.
If you notice any of these signs, avoid interacting with the site and report it to your IT team or the website owner.
How to Protect Yourself from Watering Hole Attacks
Protecting yourself requires a mix of good habits and technical defenses. Here’s what you can do:
For Individuals
- Keep Software Updated: Regularly update your browser, operating system, and antivirus software to patch vulnerabilities.
- Use Security Extensions: Browser extensions can block malicious scripts and ads.
- Be Cautious with Downloads: Avoid downloading files from websites unless you trust them completely.
- Enable Multi-Factor Authentication: This adds an extra layer of security to your accounts.
- Regular Scans: Run antivirus scans frequently to catch infections early.
For Organizations
- Monitor Website Traffic: Use tools to detect unusual activity on websites your employees visit.
- Educate Employees: Train staff to recognize signs of watering hole attacks and report suspicious behavior.
- Implement Network Segmentation: Limit access between different parts of your network to contain infections.
- Use Web Filtering: Block access to risky websites or content.
- Regular Security Audits: Check your own websites for vulnerabilities to prevent being used as watering holes.
The Role of Cybersecurity Tools in Defense
Cybersecurity tools play a crucial role in defending against watering hole attacks. Here are some key tools:
- Web Application Firewalls (WAFs): Protect websites from being compromised by filtering malicious traffic.
- Endpoint Detection and Response (EDR): Monitors devices for suspicious activity and responds quickly.
- Threat Intelligence Platforms: Provide information about emerging threats and compromised sites.
- Sandboxing: Isolates suspicious files or websites to analyze behavior safely.
- Intrusion Detection Systems (IDS): Alert administrators about unusual network activity.
Using these tools together creates a stronger defense against watering hole attacks.
What to Do If You Suspect a Watering Hole Attack
If you think you’ve encountered a watering hole attack, act quickly:
- Disconnect from the Internet: This can stop malware from communicating with attackers.
- Run a Full Antivirus Scan: Identify and remove any infections.
- Change Passwords: Especially for sensitive accounts accessed recently.
- Report the Incident: Inform your IT department or cybersecurity team.
- Avoid Visiting the Suspicious Site: Until it is confirmed safe.
Taking these steps can limit damage and help your organization respond effectively.
Future Trends in Watering Hole Attacks
As cyber threats evolve, watering hole attacks are becoming more sophisticated. Here’s what to expect:
- Use of AI and Automation: Attackers may use AI to identify and compromise websites faster.
- Targeting Mobile Devices: With more people using smartphones, attackers might focus on mobile-friendly sites.
- Supply Chain Attacks: Combining watering hole tactics with software supply chain attacks to reach more victims.
- Increased Use of Encrypted Traffic: Making detection harder for security tools.
Staying informed and updating your defenses regularly is key to keeping up with these trends.
Conclusion
Watering hole attacks are a clever and dangerous form of cyberattack that target trusted websites to infect specific groups. By understanding how these attacks work, you can better protect yourself and your organization. Remember, staying cautious online and keeping your software updated are simple but effective ways to reduce your risk.
Whether you’re an individual or part of a company, awareness and proactive security measures are your best defense. Keep learning about new threats and use the right tools to stay safe in today’s digital world.
FAQs
What is the main goal of a watering hole attack?
The main goal is to infect a specific group of users by compromising websites they trust and visit often, allowing attackers to steal data or control devices.
How do attackers choose which websites to compromise?
They research the target group’s habits and pick websites frequently visited by them, such as industry forums or professional organizations.
Can antivirus software detect watering hole attacks?
Yes, modern antivirus and endpoint detection tools can often detect malware from watering hole attacks, but early detection depends on timely updates and scans.
Are watering hole attacks common on mobile devices?
While less common, attackers are increasingly targeting mobile-friendly sites to infect smartphones and tablets as mobile usage grows.
How can organizations prevent their websites from being used in watering hole attacks?
Organizations should regularly update and patch their websites, use web application firewalls, and monitor for suspicious activity to prevent compromise.





