What is Trojan Infection
Introduction
You might have heard the term "Trojan infection" and wondered what it really means. In simple terms, a Trojan infection is a type of malware that tricks you into letting it into your device. Unlike viruses that spread on their own, Trojans disguise themselves as harmless files or programs.
Understanding how Trojan infections work is important because they can cause serious damage to your data and privacy. In this article, I’ll explain what a Trojan infection is, how it spreads, signs to watch for, and how you can protect yourself from it.
What Is a Trojan Infection?
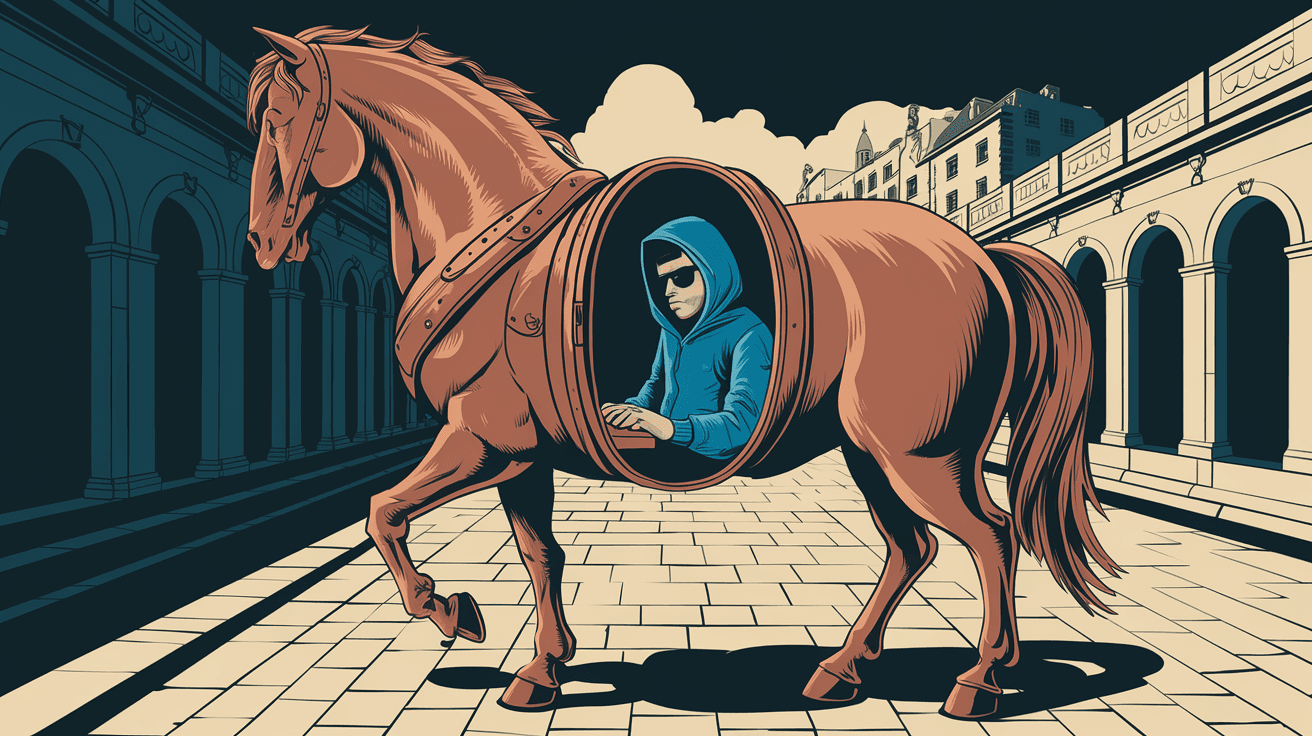
A Trojan infection is a kind of malicious software that pretends to be something useful or harmless. The name comes from the famous story of the Trojan Horse, where soldiers hid inside a wooden horse to sneak into a city. Similarly, a Trojan hides inside a file or program to sneak into your device.
Unlike viruses or worms, Trojans don’t replicate themselves. Instead, they rely on you to download or open them. Once inside, they can do many harmful things, such as stealing your personal information, damaging files, or giving hackers control over your device.
How Trojans Work
- Disguise: Trojans often look like legitimate software, games, or email attachments.
- Delivery: They get into your device when you download or open the fake file.
- Activation: Once activated, they can install other malware or spy on your activities.
- Damage: They may delete files, steal passwords, or use your device for attacks on others.
Common Types of Trojan Infections
There are several types of Trojans, each designed for a specific purpose. Knowing these can help you recognize threats better.
- Backdoor Trojans: Allow hackers to control your device remotely.
- Downloader Trojans: Download and install other malicious software.
- Spyware Trojans: Monitor your activities and steal sensitive data.
- Ransomware Trojans: Lock your files and demand payment to unlock them.
- Banking Trojans: Target your financial information to steal money.
- Fake Antivirus Trojans: Pretend to be security software but actually harm your device.
Each type can cause different problems, but all are dangerous and should be avoided.
How Do Trojan Infections Spread?
Trojans spread mainly through trickery. They rely on you to open the door, so to speak. Here are the most common ways Trojans get into devices:
- Email Attachments: Opening attachments from unknown or suspicious emails.
- Fake Software Downloads: Downloading software from untrustworthy websites.
- Malicious Links: Clicking on links in emails, messages, or websites that lead to infected files.
- Social Engineering: Hackers tricking you into installing the Trojan by pretending to be someone you trust.
- Pirated Software: Using cracked or pirated software often comes with hidden Trojans.
Being cautious about what you download and open is the best way to avoid infection.
Signs Your Device Might Have a Trojan Infection
It’s not always easy to know if your device has a Trojan. However, some common signs can alert you:
- Slow Performance: Your device runs slower than usual.
- Unexpected Pop-ups: Strange ads or warnings appear frequently.
- Programs Crashing: Apps or the system crash without reason.
- Unusual Network Activity: Your internet is busy even when you’re not using it.
- Disabled Security Software: Antivirus or firewall stops working.
- New Icons or Files: Unknown programs or files appear on your device.
- Password Problems: You notice unauthorized access to your accounts.
If you see these signs, it’s important to scan your device immediately.
How to Protect Yourself from Trojan Infections
Protecting yourself from Trojans involves a mix of good habits and tools. Here’s what you can do:
- Use Reliable Antivirus Software: Keep it updated and run regular scans.
- Be Careful with Emails: Don’t open attachments or links from unknown senders.
- Download from Trusted Sources: Only get software from official websites.
- Keep Your System Updated: Install updates for your operating system and apps.
- Avoid Pirated Software: It often contains hidden malware.
- Use a Firewall: It helps block unauthorized access.
- Backup Your Data: Regular backups protect your files if something goes wrong.
- Educate Yourself: Learn about phishing and social engineering tactics.
Following these steps greatly reduces your risk of infection.
What to Do If You Suspect a Trojan Infection
If you think your device has a Trojan, act quickly to minimize damage:
- Disconnect from the Internet: This stops the Trojan from communicating with hackers.
- Run a Full Antivirus Scan: Use your security software to detect and remove threats.
- Update Your Security Software: Make sure it has the latest virus definitions.
- Delete Suspicious Files: Remove any unknown or suspicious programs.
- Change Your Passwords: Especially for important accounts like email and banking.
- Restore from Backup: If possible, restore your system to a clean state.
- Seek Professional Help: If you’re unsure, a technician can help clean your device.
Acting fast can save your data and prevent further harm.
The Impact of Trojan Infections on Privacy and Security
Trojan infections don’t just slow down your device; they can seriously harm your privacy and security. Here’s how:
- Data Theft: Trojans can steal passwords, credit card numbers, and personal files.
- Identity Theft: Hackers use stolen data to impersonate you.
- Financial Loss: Banking Trojans can empty your accounts.
- Device Control: Backdoor Trojans let hackers control your device remotely.
- Spread of Malware: Trojans can download other dangerous malware.
- Damage to Reputation: If your device is used for attacks, it can hurt your online reputation.
Understanding these risks shows why prevention is so important.
How Trojan Infections Have Evolved
Trojan infections have become more sophisticated over time. Hackers use advanced techniques to avoid detection and increase damage.
- Polymorphic Trojans: Change their code to avoid antivirus detection.
- Fileless Trojans: Operate in memory without leaving files on disk.
- Mobile Trojans: Target smartphones and tablets.
- Multi-Stage Trojans: Use several steps to infect and control devices.
- Social Media Trojans: Spread through fake profiles and messages.
Because of these advances, staying informed and using strong security measures is essential.
Conclusion
Now you know what a Trojan infection is and how it can affect your device and privacy. Trojans are tricky because they hide in plain sight, pretending to be safe files or programs. But with the right knowledge and tools, you can protect yourself.
Always be cautious about what you download and open. Use trusted antivirus software and keep everything updated. If you suspect an infection, act quickly to remove it. Staying alert and prepared is the best way to keep your devices safe from Trojan infections.
FAQs
What is the main difference between a Trojan and a virus?
A Trojan disguises itself as a harmless file and requires you to open it, while a virus can replicate and spread on its own without your action.
Can Trojans infect smartphones?
Yes, Trojans can infect smartphones, especially through malicious apps or links, targeting both Android and iOS devices.
How can I tell if an email attachment contains a Trojan?
Be cautious if the email is from an unknown sender, contains unexpected attachments, or has suspicious language and formatting.
Is antivirus software enough to stop Trojans?
Antivirus software is essential but not enough alone. Safe browsing habits and keeping software updated are also crucial.
Can a Trojan infection be completely removed?
Yes, with proper antivirus tools and sometimes professional help, Trojans can be fully removed from your device.





