What is Trojan Horse
Introduction
You might have heard the term "Trojan Horse" in different contexts, but what does it really mean? Whether you're curious about history or cybersecurity, understanding the Trojan Horse can help you recognize hidden dangers and clever tricks.
In this article, I’ll explain what a Trojan Horse is, where the idea comes from, and how it applies today. You’ll learn about its origins in ancient stories and how the term is used in computer security to describe a type of malware.
What is a Trojan Horse?
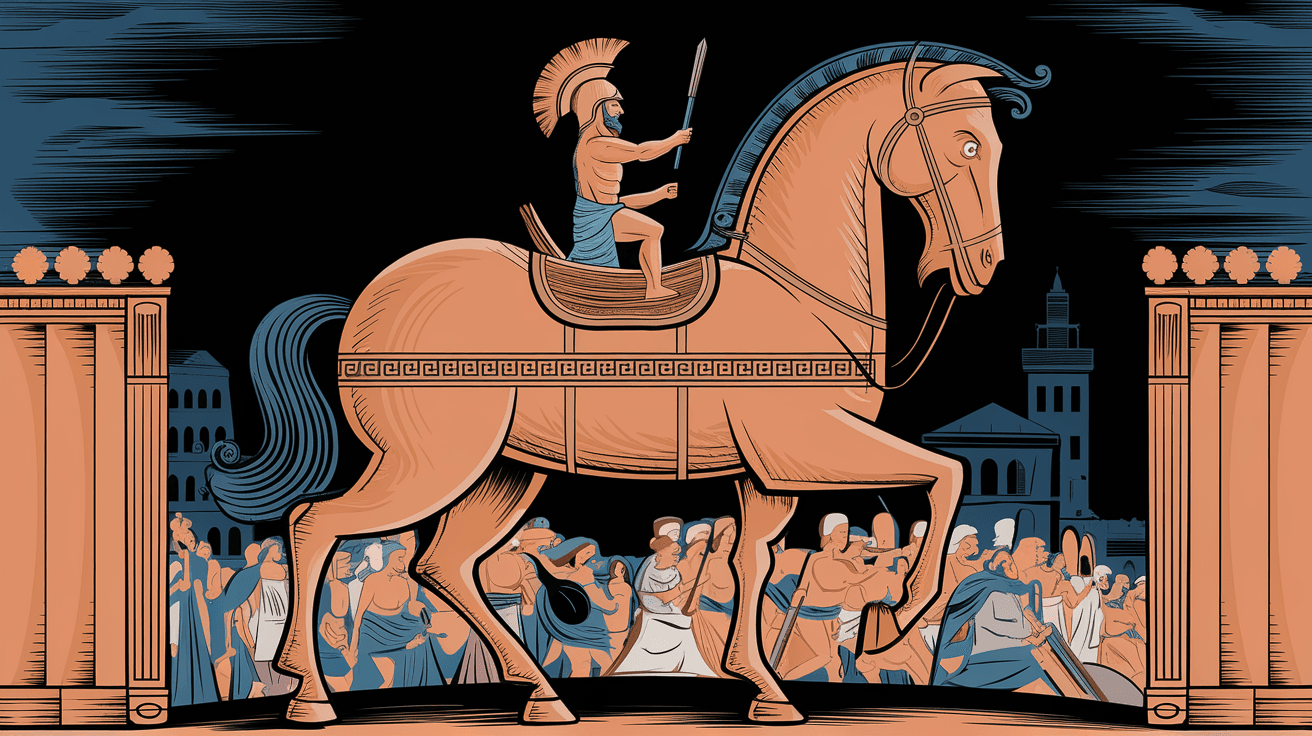
A Trojan Horse is a concept that comes from an ancient Greek story. It refers to a trick where something harmful is hidden inside something that looks safe or useful. The name comes from the wooden horse used by the Greeks to enter the city of Troy during the Trojan War.
In modern times, the term "Trojan Horse" is mostly used in cybersecurity. It describes a type of malicious software (malware) that tricks users into installing it by pretending to be something harmless. Once inside a computer, it can cause damage or steal information.
The Origin of the Trojan Horse Story
The story of the Trojan Horse is part of Greek mythology. According to legend, the Greeks wanted to capture the city of Troy but could not break through its walls. So, they built a giant wooden horse and hid soldiers inside it.
The Trojans thought the horse was a gift and brought it inside their city walls. At night, the hidden soldiers came out and opened the gates for the Greek army, leading to Troy’s defeat.
This story shows how something that looks safe can hide danger, which is why the term "Trojan Horse" is used for deceptive attacks.
Trojan Horse in Cybersecurity
In cybersecurity, a Trojan Horse is a type of malware that tricks you into running it. Unlike viruses or worms, Trojans don’t replicate themselves. Instead, they rely on users to install them by disguising as legitimate software.
Once installed, Trojans can:
- Steal personal information like passwords and credit card numbers.
- Create backdoors for hackers to access your computer.
- Download and install other malware.
- Damage or delete files.
Because Trojans rely on deception, they are often spread through email attachments, fake software downloads, or malicious websites.
How Does a Trojan Horse Work?
Understanding how a Trojan Horse works can help you avoid falling victim to one. Here’s a simple breakdown of the process:
- Disguise: The Trojan pretends to be something useful or interesting, like a game, a tool, or an email attachment.
- Installation: You download or open the Trojan, thinking it’s safe.
- Activation: Once inside your system, the Trojan activates its harmful functions.
- Damage or Theft: The Trojan carries out its mission, such as stealing data or damaging files.
- Hidden Presence: Trojans often try to stay hidden to avoid detection by antivirus software.
Common Ways Trojans Spread
Trojans can reach your device through various methods:
- Email Attachments: Opening attachments from unknown senders.
- Fake Software: Downloading cracked or pirated software.
- Malicious Websites: Visiting unsafe websites that prompt downloads.
- Social Engineering: Clicking on links or pop-ups that look legitimate.
Signs Your Computer Might Have a Trojan
It’s important to recognize if your device is infected. Some common signs include:
- Slow performance or frequent crashes.
- Unexpected pop-up ads.
- Programs opening or closing on their own.
- Unusual network activity.
- Disabled antivirus software.
If you notice these signs, running a full antivirus scan is a good first step.
Protecting Yourself from Trojan Horses
You can take several steps to protect your computer and personal data from Trojan Horses. Here are some practical tips:
- Use Reliable Antivirus Software: Keep it updated to detect the latest threats.
- Avoid Unknown Links and Attachments: Don’t open emails or messages from strangers.
- Download Software from Trusted Sources: Avoid pirated or cracked programs.
- Keep Your System Updated: Install security patches regularly.
- Enable Firewalls: They help block unauthorized access.
- Be Careful with Pop-ups: Don’t click on suspicious ads or alerts.
- Backup Your Data: Regular backups can save your files if something goes wrong.
Trojan Horse in History vs. Modern Usage
The original Trojan Horse story is a powerful metaphor for deception. In history, it was a physical trick used in war. Today, it’s a digital threat that hides inside software.
Historical Trojan Horse
- A wooden horse built by Greeks.
- Hidden soldiers inside.
- Used to enter and conquer Troy.
- Symbolizes clever deception.
Modern Trojan Horse
- Malware disguised as safe software.
- Relies on user trust to install.
- Can steal data or damage systems.
- Represents hidden digital threats.
Both versions teach us to be cautious about what we trust, whether it’s a gift or a file.
Examples of Famous Trojan Horse Attacks
Several well-known Trojan Horse attacks have caused major problems worldwide. Here are a few examples:
- Zeus Trojan: A banking Trojan that stole millions by capturing login details.
- Emotet: Initially a banking Trojan, it evolved into a malware distributor.
- Remote Access Trojans (RATs): Allow hackers to control infected computers remotely.
- Fake Antivirus Trojans: Trick users into paying for fake security software.
These examples show how Trojans can be used for financial theft, spying, or spreading other malware.
How to Remove a Trojan Horse
If you suspect a Trojan Horse infection, acting quickly is important. Here’s how you can remove it:
- Disconnect from the Internet: Prevent the Trojan from communicating with hackers.
- Enter Safe Mode: This limits what runs on your computer.
- Run a Full Antivirus Scan: Use trusted antivirus or anti-malware tools.
- Delete or Quarantine Threats: Follow the software’s instructions.
- Update Your Software: Patch vulnerabilities.
- Change Passwords: Especially for important accounts.
- Restore from Backup: If files are damaged or lost.
If the infection is severe, you might need professional help or a complete system reinstall.
Trojan Horse vs. Other Malware Types
It’s useful to know how Trojans differ from other malware:
| Malware Type | How It Spreads | Behavior | Replication | Example |
| Trojan Horse | Disguised as safe software | Hidden harmful actions | Does not self-replicate | Zeus Trojan |
| Virus | Attaches to files | Damages files or system | Self-replicates | ILOVEYOU virus |
| Worm | Exploits network vulnerabilities | Spreads rapidly | Self-replicates | Conficker worm |
| Ransomware | Phishing, downloads | Encrypts files for ransom | Does not self-replicate | WannaCry |
Trojans rely on tricking users, while viruses and worms spread automatically.
Conclusion
Now you know that a Trojan Horse is more than just an ancient story. It’s a powerful symbol of hidden danger that has found a new life in the digital world. Whether in history or cybersecurity, the Trojan Horse teaches us to be careful about what we trust.
By understanding how Trojans work and how to protect yourself, you can keep your devices and data safe. Always stay cautious when downloading files or clicking links, and use strong security tools to defend against these sneaky threats.
FAQs
What is the main purpose of a Trojan Horse in cybersecurity?
A Trojan Horse is designed to trick users into installing it. Once inside, it can steal data, damage files, or allow hackers to control your device without your knowledge.
How can I tell if my computer has a Trojan Horse?
Signs include slow performance, unexpected pop-ups, programs opening by themselves, unusual network activity, and disabled antivirus software.
Is a Trojan Horse the same as a virus?
No. Unlike viruses, Trojans don’t self-replicate. They rely on users to install them by pretending to be safe software.
How do Trojans spread?
Trojans spread through email attachments, fake software downloads, malicious websites, and social engineering tactics like phishing.
Can antivirus software detect all Trojan Horses?
While good antivirus software can detect many Trojans, some are designed to avoid detection. Keeping your software updated and practicing safe browsing is essential.





