What is Time-Based One-Time Password
Introduction
You’ve probably heard about two-factor authentication (2FA) and wondered how it actually works. One of the most popular methods behind 2FA is the Time-Based One-Time Password, or TOTP. It’s a simple yet powerful way to protect your online accounts from hackers.
In this article, I’ll explain what a Time-Based One-Time Password is, how it works, and why it’s important for your digital security. By the end, you’ll understand how TOTP can keep your accounts safer and how you can start using it today.
What is a Time-Based One-Time Password?
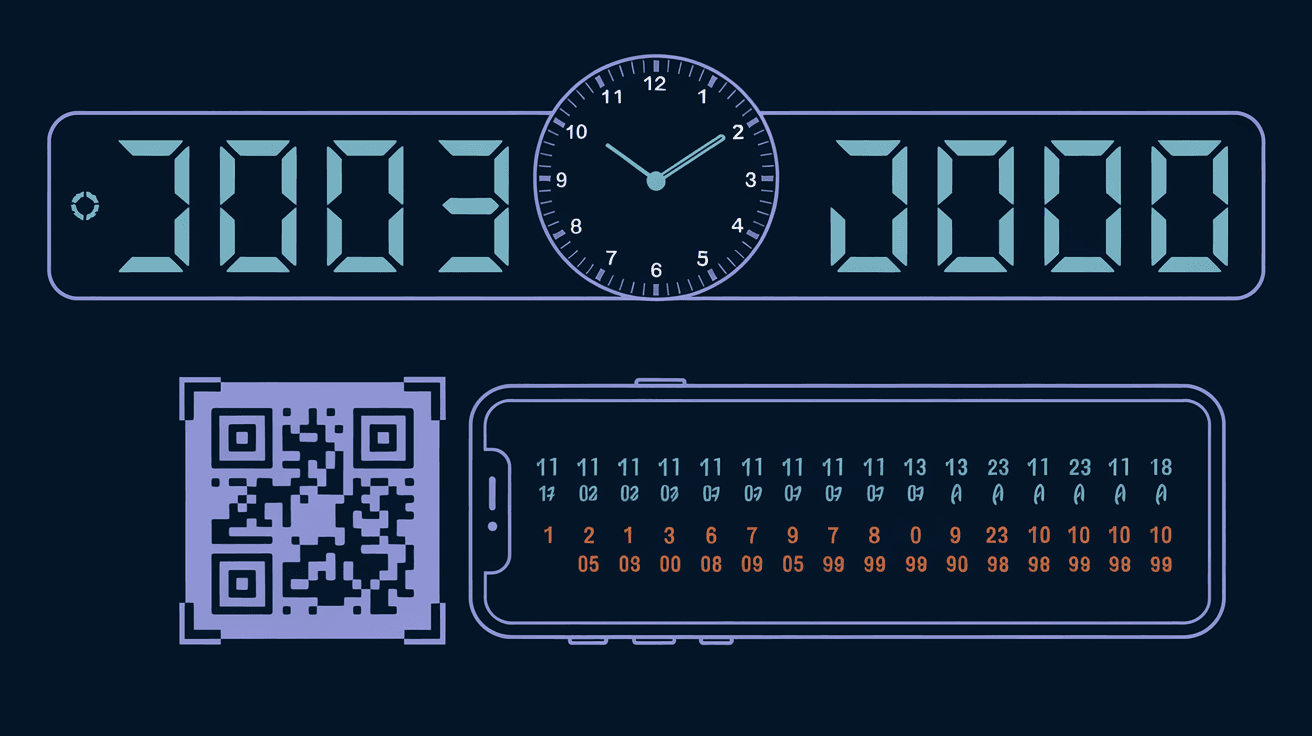
A Time-Based One-Time Password (TOTP) is a temporary code that changes every 30 seconds or so. It’s used as a second step to verify your identity when logging into an account. Unlike a regular password, which stays the same until you change it, a TOTP is only valid for a short time.
Here’s how it works:
- The TOTP is generated using a secret key shared between your device and the service you’re logging into.
- This secret key combines with the current time to create a unique code.
- Because the code changes frequently, it’s very hard for hackers to guess or reuse.
TOTP is part of a broader security method called two-factor authentication (2FA). It adds an extra layer of protection beyond just your password.
How Does TOTP Work?
TOTP relies on a few key components to generate secure, temporary codes. Let’s break down the process:
Shared Secret Key: When you set up TOTP on an app like Google Authenticator or Authy, the service gives you a secret key. This key is stored on your device and the server.
Current Time: The TOTP algorithm uses the current time, usually in 30-second intervals, to generate a new code.
Hash Function: The secret key and the current time are combined using a cryptographic hash function (usually HMAC-SHA1). This creates a unique code.
Code Display: The app shows you a 6-digit code that changes every 30 seconds.
When you log in, you enter your password and the current TOTP code. The server checks if the code matches what it expects based on the shared secret and time. If it does, you’re granted access.
Why Time Matters
The time-based aspect means the code is only valid for a short window. Even if someone steals your code, it quickly becomes useless. This makes TOTP much safer than static passwords or codes sent by email or SMS.
Benefits of Using TOTP
Using TOTP for two-factor authentication offers several advantages:
Enhanced Security: It adds a second layer of protection, making it harder for attackers to access your accounts even if they have your password.
No Internet Needed: TOTP apps generate codes offline, so you don’t need a network connection to get your code.
Phishing Resistance: Since codes expire quickly, phishing attacks that try to steal your code are less effective.
Widely Supported: Many popular services like Google, Microsoft, Dropbox, and GitHub support TOTP.
Easy to Use: Setting up TOTP is straightforward with apps that scan a QR code and start generating codes immediately.
Common TOTP Apps and How to Use Them
To use TOTP, you need an authenticator app on your smartphone or device. Here are some popular options:
Google Authenticator: One of the most widely used apps. It’s simple and supports multiple accounts.
Authy: Offers cloud backup and multi-device sync, which can be helpful if you lose your phone.
Microsoft Authenticator: Works well with Microsoft accounts and supports other services too.
LastPass Authenticator: Integrates with the LastPass password manager for added convenience.
Setting Up TOTP
Here’s a quick guide to setting up TOTP on your account:
Log into your account and find the two-factor authentication settings.
Choose the option to use an authenticator app.
The service will show a QR code.
Open your authenticator app and scan the QR code.
The app will start generating 6-digit codes.
Enter the current code into the website to verify setup.
Once done, you’ll use these codes every time you log in.
Security Considerations and Best Practices
While TOTP greatly improves security, there are some things to keep in mind:
Keep Your Secret Key Safe: If someone gets your secret key, they can generate your codes. Don’t share it or store it insecurely.
Backup Codes: Many services provide backup codes in case you lose access to your authenticator app. Store these safely.
Device Loss: If you lose your phone, you might be locked out. Use apps like Authy that offer backups or set up multiple devices.
Time Sync: Your device’s clock must be accurate. If it’s off, codes might not work. Most smartphones sync time automatically.
Beware of Phishing: TOTP codes add security but don’t protect against all phishing attacks. Always verify the website you’re logging into.
How TOTP Compares to Other 2FA Methods
There are several ways to add two-factor authentication. Here’s how TOTP stacks up:
| 2FA Method | Security Level | Convenience | Offline Use | Common Use Cases |
| SMS Codes | Moderate | High | No | Basic accounts, less secure |
| Email Codes | Low to Moderate | High | No | Less secure, prone to hacking |
| Hardware Tokens | Very High | Moderate | Yes | High-security environments |
| TOTP Apps | High | High | Yes | Most online services |
| Push Notifications | High | Very High | Requires Internet | Modern apps, easy approval |
TOTP strikes a good balance between security and convenience. It’s more secure than SMS or email codes and easier to use than hardware tokens.
Real-World Examples of TOTP Use
Many companies and services rely on TOTP to protect users:
Google: Uses TOTP for Google accounts via Google Authenticator.
GitHub: Offers TOTP for developers to secure repositories.
Dropbox: Supports TOTP to protect file storage.
Microsoft: Uses TOTP in Microsoft Authenticator for Office 365 and other services.
These examples show how TOTP is trusted by major platforms to keep your data safe.
Troubleshooting Common TOTP Issues
Sometimes, you might face problems with TOTP codes. Here’s how to fix them:
Codes Not Working: Check your device’s time settings. Sync the clock or enable automatic time updates.
Lost Phone: Use backup codes or contact the service’s support to regain access.
Multiple Devices: If you use more than one device, make sure all are synced with the same secret key.
App Crashes or Bugs: Try reinstalling the authenticator app or switching to a different one.
Conclusion
Time-Based One-Time Passwords are a simple yet powerful way to protect your online accounts. By generating temporary codes that change every 30 seconds, TOTP adds a strong layer of security beyond your password. You don’t need an internet connection to use it, and many free apps make setup easy.
If you want to keep your accounts safe from hackers, enabling TOTP-based two-factor authentication is one of the best steps you can take. It’s widely supported, user-friendly, and significantly reduces the risk of unauthorized access. Start using TOTP today and enjoy peace of mind knowing your digital life is more secure.
FAQs
What devices can I use for TOTP?
You can use smartphones, tablets, or even some desktop apps that support authenticator functions. Most people use smartphone apps like Google Authenticator or Authy.
Is TOTP safer than SMS codes?
Yes, TOTP is generally safer because it doesn’t rely on your mobile network and the codes expire quickly. SMS codes can be intercepted or redirected by attackers.
Can I use TOTP without an internet connection?
Yes, TOTP apps generate codes offline using the secret key and your device’s clock. You don’t need internet or cellular service to get your code.
What happens if I lose my phone with TOTP app?
If you lose your phone, you can use backup codes provided during setup or restore your TOTP keys from a backup if your app supports it. Otherwise, you may need to contact the service for account recovery.
How often do TOTP codes change?
TOTP codes typically change every 30 seconds. This short lifespan helps keep your accounts secure by limiting the time a code is valid.





