What is Threat Detection Engine
Introduction
You might have heard the term "Threat Detection Engine" when reading about cybersecurity. But what exactly is it, and why should you care? In simple terms, a Threat Detection Engine is a tool that helps identify harmful activities or attacks on computer systems before they cause damage.
We live in a world where cyber threats are constantly evolving. Your personal data, business information, or even government secrets can be at risk. Understanding how a Threat Detection Engine works can help you protect your digital life better. Let’s dive into what this technology is all about and how it keeps you safe.
What is a Threat Detection Engine?
A Threat Detection Engine is a software system designed to spot suspicious or malicious activities in a network or computer system. It acts like a security guard, constantly watching for signs of cyberattacks such as viruses, malware, or hacking attempts.
How It Works
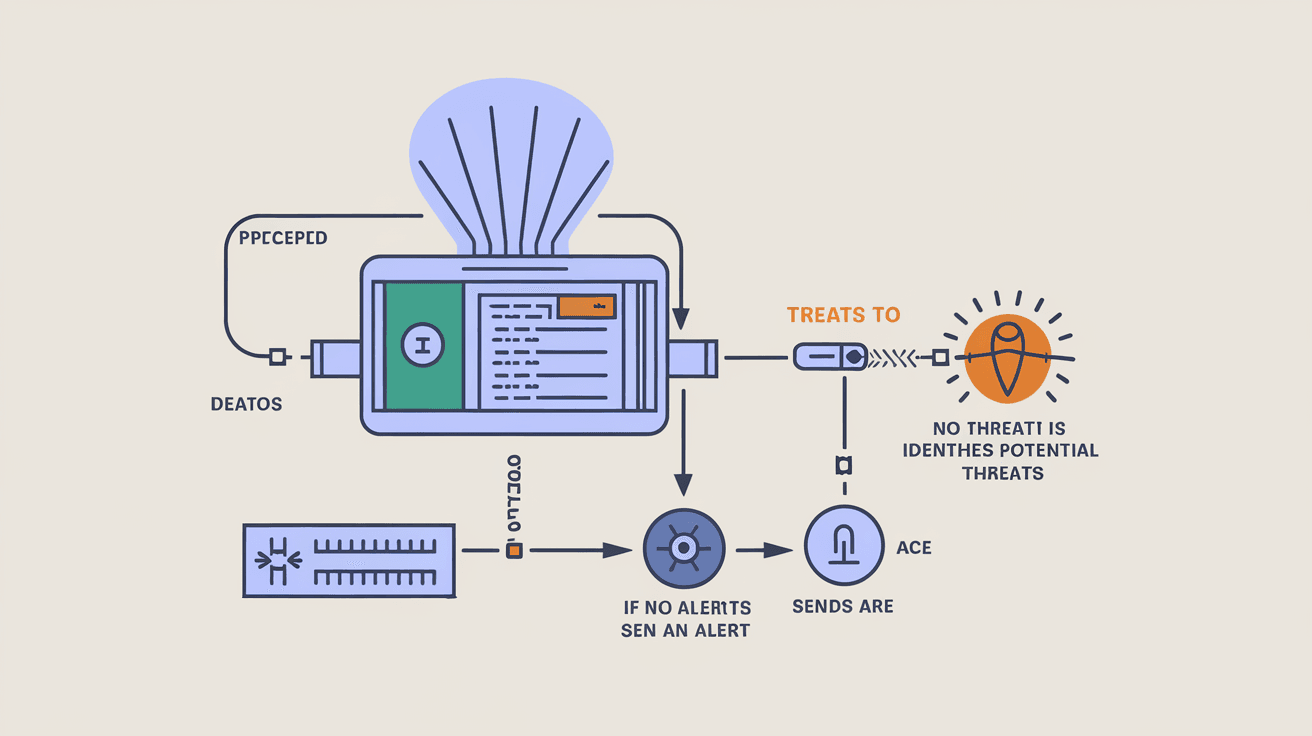
- Data Monitoring: It collects data from various sources like network traffic, system logs, and user behavior.
- Analysis: The engine analyzes this data to find unusual patterns or known attack signatures.
- Alerting: When it detects a threat, it alerts security teams or automatically takes action to block the attack.
This process helps organizations respond quickly to threats, reducing the chances of damage or data loss.
Key Components of a Threat Detection Engine
Understanding the parts that make up a Threat Detection Engine can help you see why it’s so effective.
1. Data Collection
The engine gathers information from multiple points such as:
- Network devices (routers, firewalls)
- Servers and endpoints (computers, mobile devices)
- Cloud services and applications
This wide data collection ensures the engine has a full picture of what’s happening in the system.
2. Threat Intelligence
Threat intelligence is knowledge about known cyber threats. The engine uses this to recognize attack patterns. It often updates itself with the latest threat data from global security communities.
3. Detection Algorithms
These are the rules or models the engine uses to spot threats. They include:
- Signature-based detection: Looks for known malware or attack signatures.
- Anomaly-based detection: Identifies unusual behavior that might indicate a new or unknown threat.
- Behavioral analysis: Examines how users or programs act to find suspicious activities.
4. Response Mechanism
Once a threat is detected, the engine can:
- Send alerts to security teams
- Automatically block or quarantine malicious files
- Initiate further investigation steps
This quick response is crucial to stopping attacks before they spread.
Why is a Threat Detection Engine Important?
Cyber threats are becoming more sophisticated every day. Traditional security methods like firewalls and antivirus software are no longer enough. Here’s why a Threat Detection Engine is essential:
- Early Detection: It catches threats before they cause harm.
- Reduced Damage: Quick responses limit the impact of attacks.
- Improved Visibility: It gives security teams a clear view of network activity.
- Adaptability: It can detect new, unknown threats using advanced algorithms.
- Compliance: Helps organizations meet security regulations by monitoring and reporting threats.
Types of Threat Detection Engines
There are different types of engines depending on their focus and technology.
Network-Based Threat Detection
This type monitors network traffic to find suspicious data flows or connections. It’s useful for spotting attacks like Distributed Denial of Service (DDoS) or unauthorized access.
Endpoint-Based Threat Detection
Installed on individual devices, this engine watches for malicious activities on computers or mobile devices. It can detect malware infections or unauthorized software installations.
Cloud-Based Threat Detection
With more businesses moving to the cloud, this engine focuses on cloud environments. It monitors cloud applications, storage, and services for threats.
Hybrid Threat Detection
Combines multiple detection methods to provide comprehensive protection across networks, endpoints, and cloud systems.
How Threat Detection Engines Use AI and Machine Learning
Modern Threat Detection Engines often use Artificial Intelligence (AI) and Machine Learning (ML) to improve their accuracy and speed.
- Pattern Recognition: AI can quickly identify complex attack patterns.
- Behavioral Analysis: ML models learn normal behavior and spot deviations.
- Reduced False Positives: AI helps reduce unnecessary alerts, saving time for security teams.
- Continuous Learning: The engine improves over time by learning from new threats.
These technologies make threat detection smarter and more effective.
Challenges in Threat Detection
While Threat Detection Engines are powerful, they face some challenges:
- False Positives: Sometimes, normal activities are flagged as threats, causing alert fatigue.
- Evasion Techniques: Attackers use methods to hide their activities from detection.
- Data Overload: Large volumes of data can overwhelm the system.
- Integration: Combining with existing security tools can be complex.
Addressing these challenges requires skilled security teams and continuous improvement of detection technologies.
How to Choose the Right Threat Detection Engine
If you’re looking to protect your organization, picking the right engine is important. Consider these factors:
- Coverage: Does it monitor networks, endpoints, and cloud environments?
- Detection Methods: Does it use signature, anomaly, and behavioral detection?
- AI Capabilities: Does it include machine learning for smarter detection?
- Ease of Use: Is the interface user-friendly for your security team?
- Integration: Can it work with your current security tools?
- Scalability: Can it grow with your organization’s needs?
- Support and Updates: Does the vendor provide regular updates and support?
Evaluating these will help you find a solution that fits your security needs.
Real-World Examples of Threat Detection Engines
Many companies and organizations use Threat Detection Engines to protect themselves.
- Financial Institutions: Banks use engines to detect fraud and cyberattacks on customer accounts.
- Healthcare Providers: Protect sensitive patient data from ransomware attacks.
- Government Agencies: Monitor for cyber espionage and data breaches.
- E-commerce Platforms: Detect payment fraud and account takeovers.
These examples show how vital threat detection is across industries.
Best Practices for Using a Threat Detection Engine
To get the most out of your Threat Detection Engine, follow these tips:
- Regularly Update Threat Intelligence: Keep the engine informed about new threats.
- Tune Detection Rules: Adjust settings to reduce false positives.
- Train Security Teams: Ensure your team knows how to respond to alerts.
- Integrate with Incident Response: Connect detection with your response plans.
- Monitor Continuously: Threats can happen anytime, so constant monitoring is key.
These practices help maintain strong security defenses.
Conclusion
Now you know that a Threat Detection Engine is a vital tool in cybersecurity. It watches over your systems, spots threats early, and helps stop attacks before they cause damage. With cyber threats growing more complex, relying on this technology is no longer optional but necessary.
Whether you’re protecting a small business or a large organization, understanding how these engines work can help you make smarter security decisions. By choosing the right engine and following best practices, you can keep your digital world safer and more secure.
FAQs
What is the main function of a Threat Detection Engine?
Its main function is to monitor systems and networks for suspicious activities and alert security teams to potential cyber threats.
How does a Threat Detection Engine differ from antivirus software?
Unlike antivirus, which mainly scans for known malware, a Threat Detection Engine uses multiple methods, including behavior analysis and AI, to detect a wider range of threats.
Can Threat Detection Engines prevent cyberattacks?
They help detect and respond to attacks early but usually work alongside other security tools to prevent attacks fully.
Are Threat Detection Engines suitable for small businesses?
Yes, many engines are scalable and can be tailored to protect small businesses effectively.
How often should a Threat Detection Engine be updated?
It should be updated regularly, often daily or weekly, to stay current with the latest threat intelligence and detection techniques.





