What is SIEM Correlation Rules
Introduction
If you’re diving into cybersecurity, you’ve probably heard about SIEM correlation rules. These rules are a key part of how organizations detect and respond to threats quickly. But what exactly are they, and why do they matter so much?
In this article, I’ll explain SIEM correlation rules in simple terms. You’ll learn how they work, why they’re important, and how they help security teams spot complex attacks by connecting the dots between different security events.
What Are SIEM Correlation Rules?
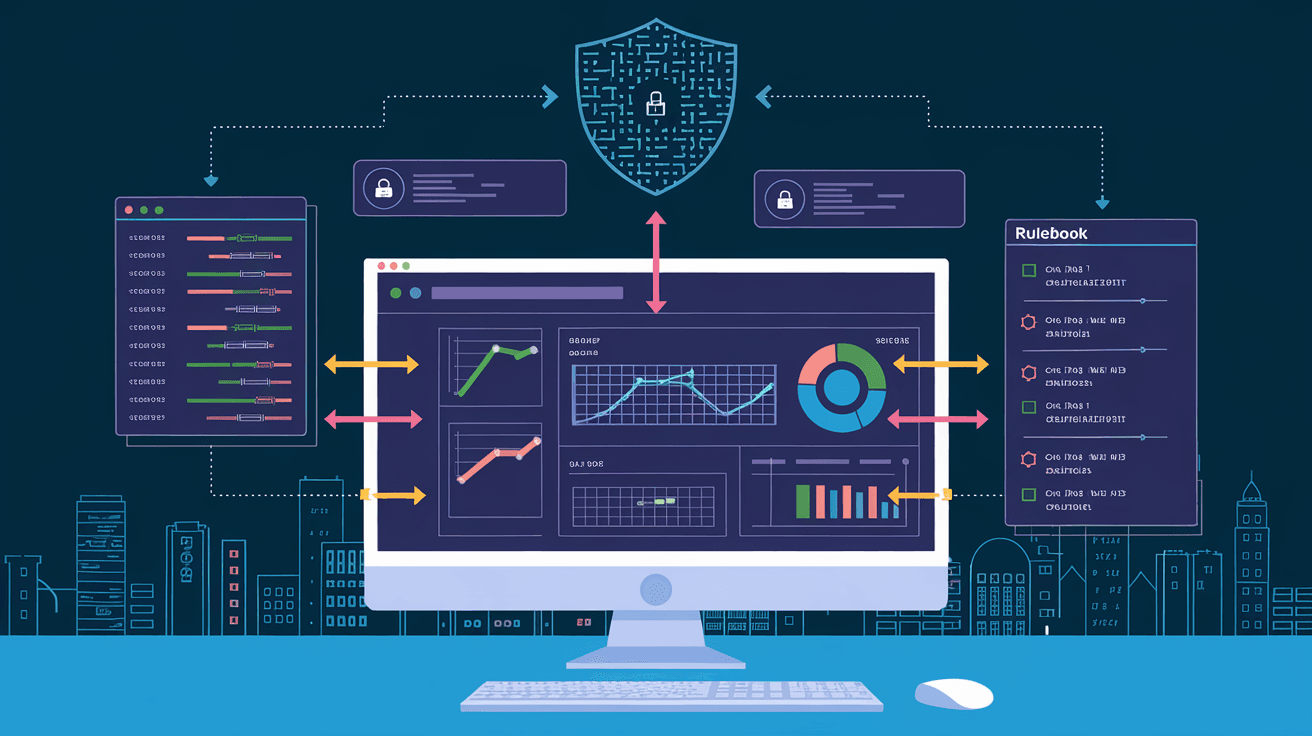
SIEM stands for Security Information and Event Management. It’s a system that collects and analyzes security data from across an organization’s network. Correlation rules are the logic inside SIEM that links related events together.
Instead of looking at each event alone, correlation rules help the SIEM system see patterns. These patterns might indicate suspicious activity or a security breach. By connecting multiple events, the SIEM can raise alerts that are more accurate and meaningful.
How Correlation Rules Work
- Collect Events: The SIEM gathers logs and alerts from firewalls, servers, applications, and more.
- Analyze Patterns: Correlation rules scan these events for specific combinations or sequences.
- Generate Alerts: When a rule matches, the SIEM creates an alert for security teams to investigate.
For example, a rule might look for multiple failed login attempts followed by a successful login from the same user. This pattern could suggest a brute force attack.
Why Are Correlation Rules Important in SIEM?
Without correlation rules, SIEM systems would just be a flood of raw data. Security teams would struggle to find real threats among thousands of harmless events.
Correlation rules help by:
- Reducing Noise: They filter out irrelevant events and focus on suspicious patterns.
- Improving Detection: They catch complex attacks that single events can’t reveal.
- Speeding Response: Alerts based on correlated events help teams act faster.
Benefits of Using Correlation Rules
- Detect multi-step attacks like phishing followed by malware installation.
- Identify insider threats by spotting unusual user behavior.
- Monitor compliance by tracking policy violations over time.
Types of SIEM Correlation Rules
There are several types of correlation rules, each designed to detect different kinds of threats. Understanding these types helps you know how SIEM systems spot attacks.
1. Temporal Correlation Rules
These rules look for events that happen within a specific time frame. For example, multiple failed logins within five minutes.
- Useful for detecting rapid attack attempts.
- Helps spot bursts of suspicious activity.
2. Sequential Correlation Rules
These rules check if events occur in a particular order. For example, a user logs in, then accesses sensitive files, then downloads data.
- Detects attack chains or insider threats.
- Tracks the flow of suspicious actions.
3. Statistical Correlation Rules
These rules use thresholds or baselines. For example, if a user accesses more files than usual in a day.
- Identifies anomalies compared to normal behavior.
- Useful for spotting unusual spikes in activity.
4. Rule-Based Correlation
These are predefined rules based on known attack patterns. For example, detecting a port scan followed by a connection attempt.
- Relies on expert knowledge.
- Easy to implement for common threats.
How to Create Effective SIEM Correlation Rules
Creating good correlation rules is both an art and a science. You want rules that catch real threats but don’t overwhelm your team with false alarms.
Steps to Build Correlation Rules
- Understand Your Environment: Know your network, users, and typical activity.
- Identify Threat Scenarios: Think about how attackers might try to breach your systems.
- Define Event Patterns: Choose which events to link and how.
- Set Time Windows: Decide how close in time events must be to correlate.
- Test and Tune: Run the rules and adjust thresholds to reduce false positives.
Tips for Better Rules
- Use multiple data sources for richer context.
- Combine different rule types for complex detection.
- Regularly review and update rules as threats evolve.
Examples of SIEM Correlation Rules in Action
Here are some practical examples of correlation rules that security teams use:
- Brute Force Detection: Multiple failed logins followed by a successful login from the same IP.
- Data Exfiltration: Large file transfers after accessing sensitive databases.
- Privilege Escalation: A user suddenly gaining admin rights and making system changes.
- Malware Infection: Antivirus alerts combined with unusual outbound network traffic.
These examples show how correlation rules help spot attacks that single events might miss.
Challenges with SIEM Correlation Rules
While powerful, correlation rules come with challenges:
- False Positives: Poorly designed rules can create too many alerts.
- Complexity: Writing effective rules requires deep security knowledge.
- Performance: Correlating large volumes of data can slow down systems.
- Maintenance: Rules need constant updates to stay relevant.
To overcome these, organizations invest in skilled analysts and use automation tools.
The Future of SIEM Correlation Rules
As cyber threats grow more sophisticated, SIEM correlation rules are evolving too. Here’s what to expect:
- AI and Machine Learning: These technologies help create smarter, adaptive correlation rules.
- Behavioral Analytics: More focus on user and entity behavior to detect insider threats.
- Cloud Integration: Correlation rules expanding to cover cloud environments and hybrid networks.
- Automation: Faster response through automated playbooks triggered by correlated alerts.
These trends make SIEM correlation rules even more essential for modern security.
Conclusion
SIEM correlation rules are the backbone of effective threat detection. They help security teams connect the dots between isolated events to spot attacks early. By understanding how these rules work and how to create them, you can improve your organization’s security posture.
Remember, correlation rules reduce noise, improve detection, and speed up response. As threats evolve, so must your rules. Staying updated and using advanced technologies will keep your SIEM system sharp and ready to protect your network.
FAQs
What is the main purpose of SIEM correlation rules?
SIEM correlation rules link related security events to detect complex threats. They help reduce false alarms and highlight suspicious patterns that single events might miss.
How do temporal correlation rules work?
Temporal correlation rules look for events occurring within a specific time frame, such as multiple failed logins in five minutes, to identify rapid or repeated suspicious activity.
Can SIEM correlation rules detect insider threats?
Yes, by analyzing unusual user behavior or sequences of actions, correlation rules can help identify insider threats like unauthorized access or data theft.
What challenges do organizations face with correlation rules?
Common challenges include false positives, complexity in rule creation, system performance issues, and the need for ongoing maintenance and updates.
How is AI improving SIEM correlation rules?
AI helps by creating adaptive rules that learn from data patterns, reducing false positives, and enabling faster, more accurate threat detection and response.





