What is Segmentation Firewall
Introduction
When you think about protecting your network, you might picture a big wall keeping threats out. But what if you need more than just one barrier? That’s where a segmentation firewall comes in. It helps you divide your network into smaller parts, making it easier to control and protect each section.
In this article, I’ll explain what a segmentation firewall is, how it works, and why it’s becoming a must-have for businesses and organizations today. You’ll see how it can improve your security and reduce risks by limiting access within your network.
What is a Segmentation Firewall?
A segmentation firewall is a security tool that divides a large network into smaller, isolated segments. Each segment can have its own rules and controls. This way, even if one part of the network is compromised, the attacker cannot easily move to other areas.
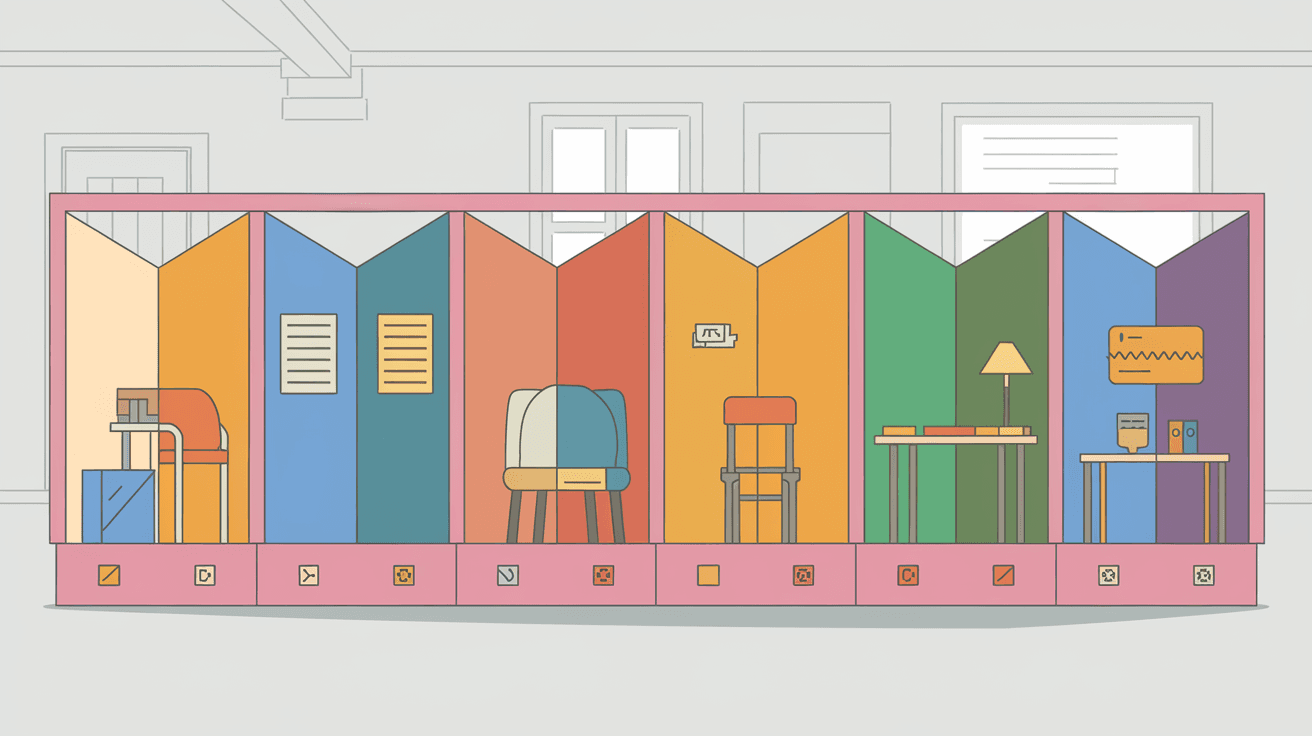
Think of it like rooms in a house. Instead of leaving all doors open, you lock some rooms to protect valuable items. The segmentation firewall acts like those locked doors inside your network.
How Segmentation Firewalls Differ from Traditional Firewalls
- Traditional firewalls protect the network perimeter, blocking threats from outside.
- Segmentation firewalls work inside the network, controlling traffic between different segments.
- They provide micro-segmentation, which means very detailed control over who can access what.
This internal control is crucial because many attacks happen from inside the network or after an attacker bypasses the outer firewall.
How Does a Segmentation Firewall Work?
Segmentation firewalls use rules and policies to control traffic between network segments. These rules define which devices or users can communicate with each other.
Here’s how it works step-by-step:
- Network Division: The network is divided into segments based on function, sensitivity, or user groups.
- Policy Creation: Security policies are set for each segment, specifying allowed and blocked traffic.
- Traffic Inspection: The firewall inspects all traffic moving between segments.
- Access Control: Only authorized traffic is allowed; unauthorized attempts are blocked or logged.
Types of Segmentation
- Physical Segmentation: Using separate hardware or switches to isolate segments.
- Virtual Segmentation: Using VLANs (Virtual Local Area Networks) or software-defined networking.
- Micro-Segmentation: Applying very fine-grained rules, often with software firewalls or agents on devices.
Benefits of Using a Segmentation Firewall
Using a segmentation firewall brings many advantages to your network security and management.
Improved Security
- Limits the spread of malware or attackers inside the network.
- Reduces the risk of insider threats by restricting access.
- Helps meet compliance requirements by isolating sensitive data.
Better Network Performance
- Reduces unnecessary traffic between segments.
- Allows for more efficient monitoring and troubleshooting.
Simplified Management
- Easier to apply specific policies to different departments or functions.
- Helps quickly identify and isolate security issues.
Real-World Example
A hospital uses segmentation firewalls to separate patient records, medical devices, and guest Wi-Fi. If a hacker gains access to the guest network, they cannot reach sensitive patient data because the firewall blocks that traffic.
Common Use Cases for Segmentation Firewalls
Segmentation firewalls are useful in many industries and scenarios.
Healthcare
Protects patient data and medical devices from cyber threats.
Finance
Isolates sensitive financial systems to prevent fraud and data breaches.
Manufacturing
Secures operational technology (OT) networks from IT networks to avoid disruptions.
Cloud Environments
Controls traffic between virtual machines and services in cloud infrastructures.
Remote Workforces
Limits access for remote users to only necessary resources, reducing risk.
How to Implement a Segmentation Firewall
Implementing a segmentation firewall requires careful planning and execution.
Steps to Follow
- Assess Your Network: Identify critical assets and how your network is currently structured.
- Define Segments: Group devices and users based on roles, sensitivity, or function.
- Create Policies: Develop clear rules for what traffic is allowed between segments.
- Deploy the Firewall: Use hardware or software solutions to enforce segmentation.
- Monitor and Adjust: Continuously watch traffic and update policies as needed.
Tools and Technologies
- Next-Generation Firewalls (NGFW): Often include segmentation features.
- Software-Defined Networking (SDN): Allows dynamic segmentation.
- Micro-Segmentation Platforms: Like VMware NSX or Cisco ACI.
Challenges and Considerations
While segmentation firewalls offer many benefits, there are challenges to keep in mind.
Complexity
- Designing and managing multiple segments can be complicated.
- Requires skilled staff to maintain policies and monitor traffic.
Performance Impact
- Inspecting traffic between segments may add latency.
- Needs proper hardware or cloud resources to handle load.
Policy Management
- Overly strict policies can disrupt business operations.
- Too loose policies reduce security benefits.
Integration
- Must work well with existing security tools and network infrastructure.
Future Trends in Segmentation Firewalls
As cyber threats evolve, segmentation firewalls are also advancing.
AI and Machine Learning
- Automated policy creation and threat detection.
- Adaptive segmentation based on real-time risk.
Zero Trust Architecture
- Segmentation firewalls are key to implementing zero trust.
- Continuous verification of users and devices before granting access.
Cloud-Native Segmentation
- More segmentation happening inside cloud platforms.
- Integration with container security and serverless computing.
Conclusion
A segmentation firewall is a powerful tool that helps you protect your network by dividing it into smaller, controlled parts. It stops attackers from moving freely inside your system and keeps sensitive data safe. By using segmentation firewalls, you gain better security, improved network performance, and easier management.
If you want to strengthen your network defenses in 2025, understanding and implementing segmentation firewalls is essential. Whether you run a business, healthcare facility, or cloud environment, this approach helps you stay one step ahead of cyber threats.
FAQs
What is the main purpose of a segmentation firewall?
Its main purpose is to divide a network into smaller segments and control traffic between them, limiting the spread of threats and improving security inside the network.
How does micro-segmentation differ from regular segmentation?
Micro-segmentation applies very detailed, fine-grained rules to control access at the device or application level, while regular segmentation usually divides the network into larger parts.
Can segmentation firewalls work in cloud environments?
Yes, many cloud providers support segmentation firewalls to control traffic between virtual machines, containers, and services within the cloud.
What industries benefit most from segmentation firewalls?
Healthcare, finance, manufacturing, and any industry handling sensitive data or critical systems benefit greatly from segmentation firewalls.
Is implementing a segmentation firewall difficult?
It can be complex and requires planning, skilled staff, and ongoing management, but the security benefits usually outweigh the challenges.





