What is Security Monitoring
Introduction
You might wonder what security monitoring really means and why it’s so important today. Whether you’re a business owner, IT professional, or just someone curious about safety, understanding security monitoring helps you protect your data and property better. It’s not just about cameras or alarms anymore; it’s a whole system working to keep threats away.
In this article, I’ll explain what security monitoring is, how it works, and why you need it. You’ll also learn about the tools and strategies involved, so you can make smarter decisions about your security needs.
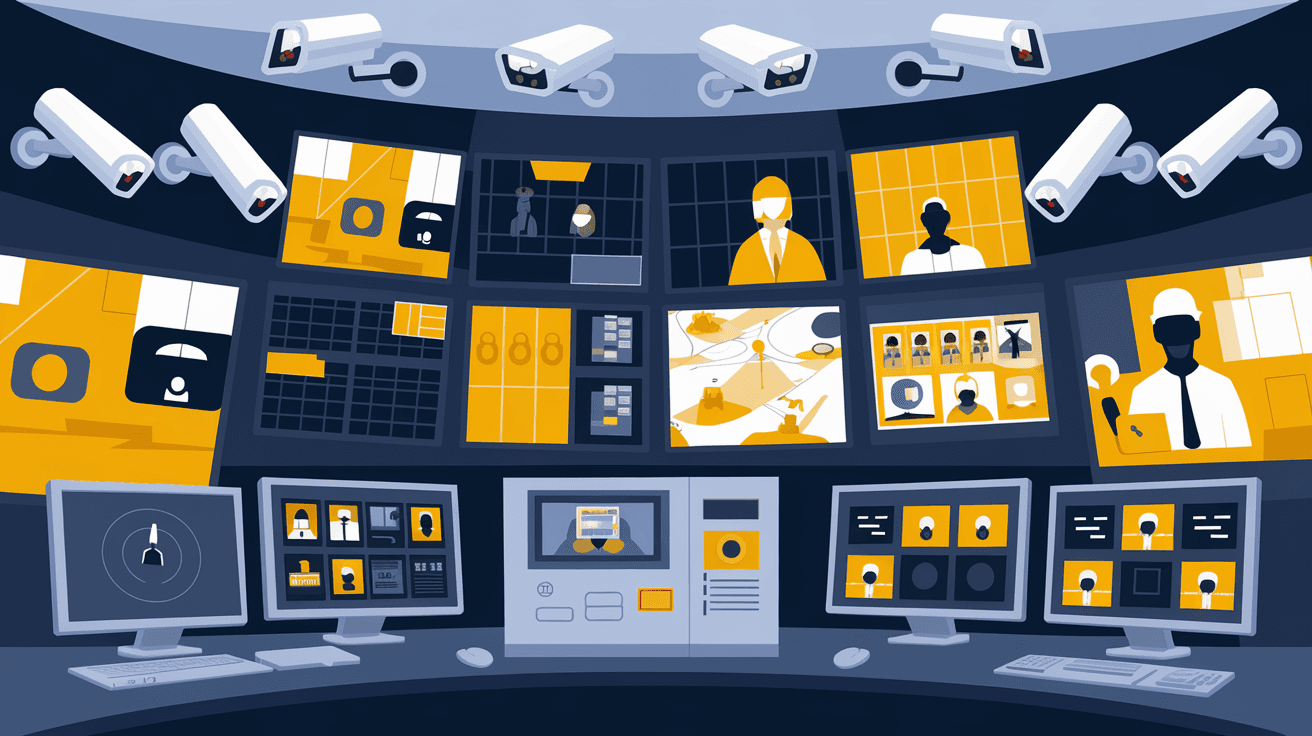
What Is Security Monitoring?
Security monitoring is the continuous process of observing and analyzing systems, networks, or physical spaces to detect and respond to threats. It helps identify suspicious activities early, so you can prevent damage or loss.
This monitoring can be digital, like watching over computer networks, or physical, like keeping an eye on buildings with cameras. The goal is to spot problems quickly and act before they escalate.
Types of Security Monitoring
- Network Security Monitoring: Watches data traffic for unusual patterns or attacks.
- Physical Security Monitoring: Uses cameras, sensors, and guards to protect physical locations.
- Application Security Monitoring: Checks software for vulnerabilities or breaches.
- User Activity Monitoring: Tracks user behavior to detect insider threats or misuse.
How Does Security Monitoring Work?
Security monitoring works by collecting data from various sources and analyzing it for signs of trouble. This process involves several key steps:
- Data Collection: Sensors, cameras, logs, and software gather information continuously.
- Data Analysis: Automated tools or security experts review the data to find anomalies.
- Alerting: When a threat is detected, alerts notify the responsible team or system.
- Response: The team investigates and takes action to stop or reduce the threat.
Tools Used in Security Monitoring
- Security Information and Event Management (SIEM): Combines data from multiple sources for real-time analysis.
- Intrusion Detection Systems (IDS): Detects unauthorized access attempts.
- Video Surveillance Systems: Monitors physical spaces with cameras.
- Endpoint Detection and Response (EDR): Watches individual devices for suspicious activity.
Why Is Security Monitoring Important?
Security monitoring is essential because threats are constantly evolving. Hackers, malware, and physical intruders are always looking for weaknesses. Without monitoring, you might not notice a breach until it’s too late.
Here’s why it matters:
- Early Threat Detection: Catch problems before they cause harm.
- Compliance: Many industries require monitoring to meet legal standards.
- Risk Reduction: Minimizes financial and reputational damage.
- Improved Incident Response: Faster action limits the impact of attacks.
Security Monitoring in Cybersecurity
In cybersecurity, security monitoring focuses on protecting digital assets like networks, servers, and data. It involves watching for signs of hacking, malware, or unauthorized access.
Key Cybersecurity Monitoring Practices
- Log Monitoring: Reviewing system logs for unusual activity.
- Network Traffic Analysis: Spotting suspicious data flows.
- Vulnerability Scanning: Finding weak points before attackers do.
- Threat Intelligence Integration: Using external data to anticipate attacks.
Cybersecurity monitoring tools often use artificial intelligence and machine learning to improve detection accuracy and reduce false alarms.
Physical Security Monitoring Explained
Physical security monitoring protects buildings, equipment, and people. It uses devices like cameras, motion sensors, and access controls to watch for unauthorized entry or suspicious behavior.
Common Physical Security Monitoring Methods
- CCTV Cameras: Provide real-time video surveillance.
- Alarm Systems: Trigger alerts when doors or windows are breached.
- Access Control Systems: Restrict entry to authorized personnel only.
- Security Guards: Provide human oversight and quick response.
Combining these methods creates a layered defense that’s harder for intruders to bypass.
Benefits of Automated Security Monitoring
Automation plays a big role in modern security monitoring. Automated systems can process huge amounts of data faster than humans and respond immediately to threats.
Advantages of Automation
- 24/7 Monitoring: No breaks or downtime.
- Faster Detection: Immediate alerts reduce response time.
- Consistency: Eliminates human error or oversight.
- Scalability: Easily handles growing networks or facilities.
Automation tools often include dashboards that give you a clear view of your security status at any time.
Challenges in Security Monitoring
While security monitoring is powerful, it comes with challenges you should know about:
- False Positives: Alerts that turn out to be harmless can waste time.
- Data Overload: Too much information can be hard to manage.
- Cost: Advanced monitoring systems can be expensive to install and maintain.
- Privacy Concerns: Monitoring must balance security with respecting privacy laws.
Addressing these challenges requires careful planning and the right technology choices.
How to Implement Security Monitoring Effectively
If you want to set up security monitoring, follow these steps to get it right:
- Assess Your Risks: Identify what you need to protect and from whom.
- Choose the Right Tools: Select monitoring systems that fit your needs and budget.
- Train Your Team: Make sure staff know how to use the tools and respond to alerts.
- Establish Procedures: Define clear steps for investigating and handling incidents.
- Regularly Review: Update your monitoring strategy as threats and technology evolve.
Future Trends in Security Monitoring
Security monitoring is evolving quickly with new technologies and threats. Here are some trends shaping the future:
- AI and Machine Learning: Smarter detection and predictive capabilities.
- Cloud-Based Monitoring: Easier access and scalability.
- Integration of Physical and Cybersecurity: Unified systems for better protection.
- IoT Security Monitoring: Protecting connected devices in homes and businesses.
Staying informed about these trends helps you keep your security measures up to date.
Conclusion
Security monitoring is a vital part of protecting your digital and physical assets. It involves watching for threats, analyzing data, and responding quickly to keep you safe. Whether you’re managing a business or securing your home, understanding how security monitoring works helps you make better choices.
By using the right tools and strategies, you can detect problems early and reduce risks. Remember, security monitoring is not a one-time setup but an ongoing process that adapts to new challenges. Staying proactive is the best way to keep your environment secure.
FAQs
What is the main purpose of security monitoring?
The main purpose is to continuously watch systems or spaces to detect and respond to threats early, preventing damage or loss.
How does security monitoring differ from security management?
Security monitoring focuses on real-time detection of threats, while security management involves planning and implementing overall security policies.
Can small businesses benefit from security monitoring?
Yes, small businesses can protect their assets and data by using affordable monitoring tools tailored to their needs.
What role does AI play in security monitoring?
AI helps analyze large data sets quickly, improving threat detection accuracy and reducing false alarms.
Is physical security monitoring still important in a digital world?
Absolutely. Physical security protects people and property, complementing cybersecurity for comprehensive protection.





