What is Security Information and Event Management (SIEM)
Introduction
You might have heard the term Security Information and Event Management, or SIEM, but wondered what it really means. If you’re responsible for protecting your organization’s data or just curious about cybersecurity, understanding SIEM is a great place to start. It’s a powerful tool that helps you detect, analyze, and respond to security threats in real time.
In this article, I’ll explain what SIEM is, how it works, and why it’s become a key part of modern cybersecurity. Whether you’re new to the topic or looking to deepen your knowledge, you’ll find clear explanations and practical insights to help you grasp this essential technology.
What is Security Information and Event Management (SIEM)?
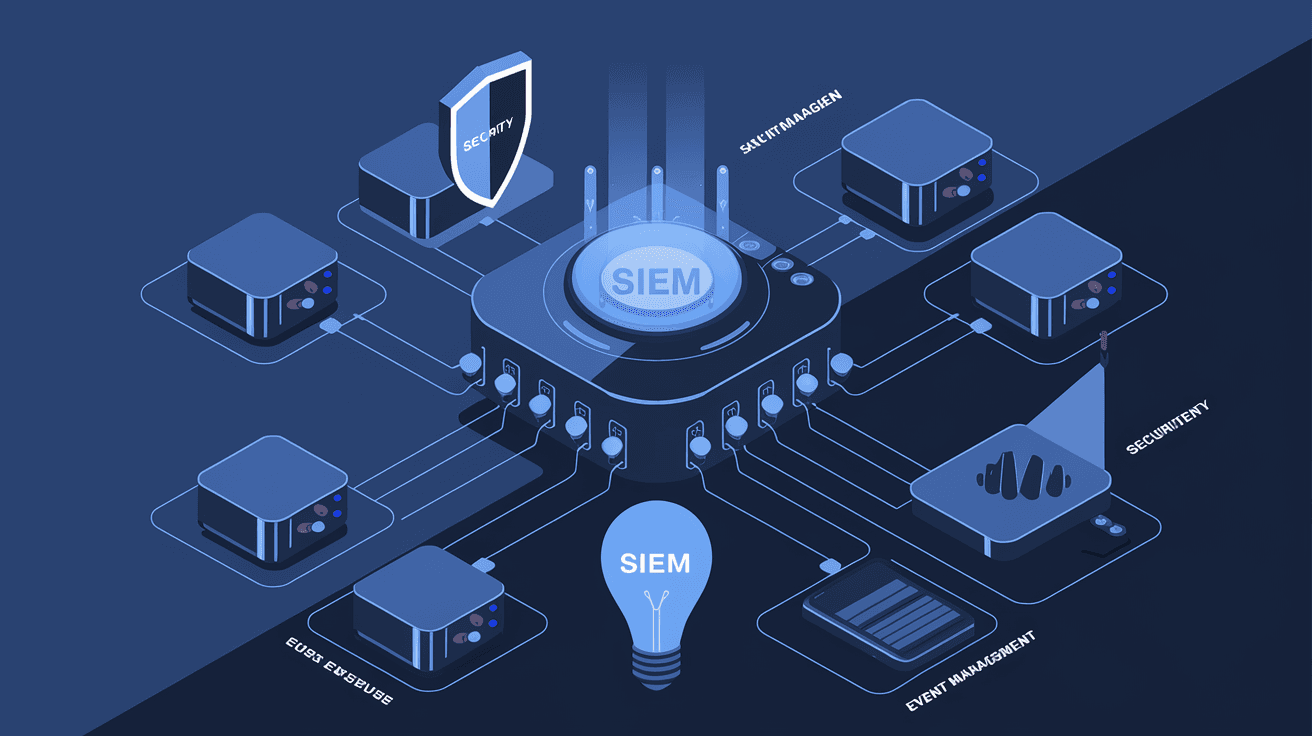
Security Information and Event Management, or SIEM, is a technology that collects and analyzes security data from across an organization’s IT environment. It combines two important functions:
- Security Information Management (SIM): Collecting and storing log data.
- Security Event Management (SEM): Real-time monitoring and analysis of security events.
Together, SIEM systems provide a centralized view of security alerts and events. This helps security teams detect unusual activities, investigate incidents, and respond quickly to threats.
Why SIEM Matters
In today’s digital world, organizations face constant cyber threats. Hackers use sophisticated methods to breach systems, and without the right tools, it’s hard to spot these attacks early. SIEM helps by:
- Gathering data from multiple sources like firewalls, servers, and applications.
- Correlating events to identify patterns that indicate a security breach.
- Alerting security teams to suspicious activities immediately.
This makes SIEM a vital part of any cybersecurity strategy.
How Does SIEM Work?
SIEM works by collecting, normalizing, and analyzing data from various sources within an IT environment. Here’s a step-by-step look at the process:
1. Data Collection
SIEM tools gather logs and event data from:
- Network devices (routers, switches)
- Security devices (firewalls, intrusion detection systems)
- Servers and endpoints
- Applications and databases
- Cloud services
This data is collected continuously to provide a complete picture of what’s happening.
2. Data Normalization
Raw data comes in many formats. SIEM systems convert this data into a consistent format so it can be analyzed effectively. This step is crucial for comparing events from different sources.
3. Event Correlation
SIEM analyzes the normalized data to find relationships between events. For example, multiple failed login attempts followed by a successful login might indicate a brute force attack. Correlation rules help identify such patterns.
4. Alerting and Reporting
When the SIEM detects suspicious activity, it generates alerts for security teams. It also provides detailed reports to help with compliance and auditing.
5. Incident Response
Some SIEM solutions integrate with automated response tools. This allows them to take immediate action, like blocking an IP address or isolating a compromised device.
Key Features of SIEM Systems
Understanding the main features of SIEM can help you see why it’s so valuable:
- Real-time Monitoring: Continuous tracking of security events to detect threats quickly.
- Log Management: Centralized collection and storage of logs for easy access and analysis.
- Event Correlation: Linking related events to identify complex attack patterns.
- Alerting: Notifying security teams about potential threats immediately.
- Forensics and Analysis: Providing tools to investigate incidents and understand their impact.
- Compliance Reporting: Generating reports to meet regulatory requirements like GDPR, HIPAA, or PCI DSS.
Benefits of Using SIEM
Implementing a SIEM system offers many advantages for organizations:
- Improved Threat Detection: SIEM helps spot threats that might go unnoticed by individual security tools.
- Faster Incident Response: Alerts and automation speed up how quickly teams can react.
- Centralized Security Management: All security data is in one place, making it easier to manage.
- Regulatory Compliance: SIEM simplifies meeting legal and industry standards.
- Reduced Risk: Early detection and response reduce the chance of data breaches and damage.
Challenges and Considerations
While SIEM is powerful, it’s not without challenges. Here are some common issues to keep in mind:
- Complexity: SIEM systems can be complex to set up and manage, requiring skilled staff.
- False Positives: Too many alerts can overwhelm teams, making it hard to focus on real threats.
- Cost: SIEM solutions can be expensive, especially for smaller organizations.
- Data Overload: Managing and analyzing large volumes of data can be challenging.
To get the most from SIEM, organizations need to tune their systems carefully and invest in training.
Types of SIEM Solutions
There are different types of SIEM solutions available, depending on your needs:
- On-Premises SIEM: Installed and managed within your own data center. Offers full control but requires more resources.
- Cloud-Based SIEM: Hosted by a service provider. Easier to deploy and scale, with lower upfront costs.
- Hybrid SIEM: Combines on-premises and cloud components for flexibility.
Choosing the right type depends on your organization’s size, budget, and security requirements.
How to Choose the Right SIEM for Your Organization
Selecting a SIEM system can be overwhelming. Here are some tips to help you decide:
- Assess Your Needs: Understand your security goals, compliance requirements, and IT environment.
- Evaluate Features: Look for real-time monitoring, event correlation, reporting, and integration capabilities.
- Consider Scalability: Choose a solution that can grow with your organization.
- Check Vendor Support: Reliable customer support and regular updates are essential.
- Test Usability: A user-friendly interface helps your team work efficiently.
- Budget Wisely: Balance cost with features and long-term value.
The Future of SIEM
SIEM technology continues to evolve. Here are some trends shaping its future:
- Integration with AI and Machine Learning: These technologies improve threat detection by identifying patterns humans might miss.
- Extended Detection and Response (XDR): Combining SIEM with other security tools for broader visibility.
- Cloud-Native SIEM: Designed specifically for cloud environments to handle dynamic workloads.
- Automation: More automated responses to reduce manual work and speed up incident handling.
These advancements make SIEM even more effective in protecting organizations.
Conclusion
Now that you know what Security Information and Event Management (SIEM) is, you can see why it’s such a critical tool for cybersecurity. SIEM collects and analyzes security data from across your IT environment, helping you detect threats early and respond quickly. It brings together real-time monitoring, event correlation, and reporting to give you a clear picture of your security posture.
While SIEM systems can be complex and costly, their benefits in improving threat detection and compliance are undeniable. As cyber threats grow more sophisticated, investing in the right SIEM solution can make a big difference in keeping your organization safe.
FAQs
What types of data does SIEM collect?
SIEM collects logs and event data from devices like firewalls, servers, applications, and cloud services. This data helps monitor and analyze security events across your entire IT environment.
How does SIEM help with compliance?
SIEM generates detailed reports that meet regulatory standards such as GDPR, HIPAA, and PCI DSS. These reports simplify audits and prove your organization’s security efforts.
Can SIEM systems automate responses to threats?
Yes, many SIEM solutions integrate with automated tools to respond immediately, like blocking suspicious IPs or isolating devices, reducing the time to contain threats.
What is event correlation in SIEM?
Event correlation links related security events from different sources to identify patterns that may indicate an attack, helping detect complex threats that single events might miss.
Is SIEM suitable for small businesses?
While SIEM can be costly and complex, cloud-based and managed SIEM services offer scalable options that small businesses can use to improve their security without heavy upfront investments.





