What is Secure Network Topology
Introduction
When you think about your network, security should be at the top of your mind. A secure network topology is the blueprint that helps protect your data and devices from cyber threats. It’s not just about connecting computers; it’s about connecting them safely.
In this article, I’ll guide you through what secure network topology means, why it’s important, and how you can design one that keeps your information safe. Whether you manage a small office or a large enterprise, understanding this concept is key to building a strong defense.
What is Network Topology?
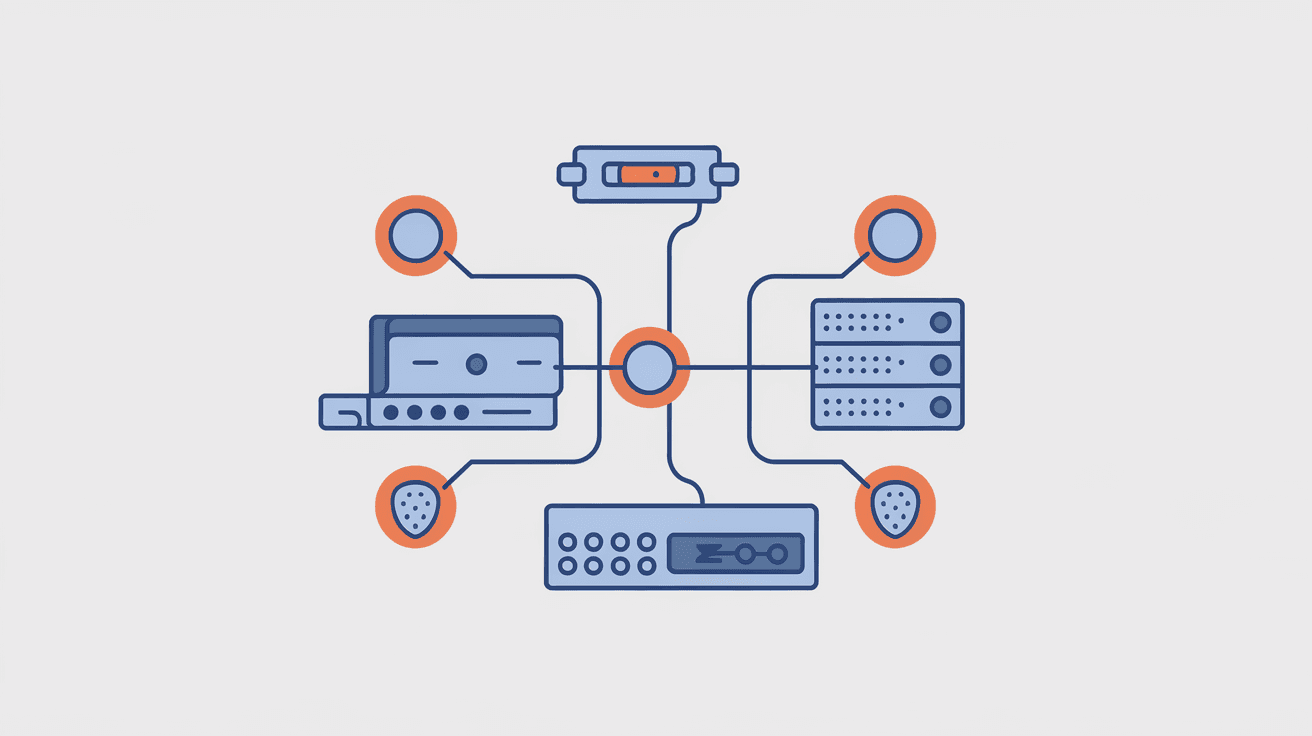
Network topology is the arrangement of different elements in a computer network. It shows how devices like computers, routers, and switches connect and communicate with each other.
There are several common types of network topologies:
- Bus Topology: All devices connect to a single cable.
- Star Topology: Devices connect to a central hub.
- Ring Topology: Devices connect in a circular fashion.
- Mesh Topology: Devices connect directly to many others.
- Hybrid Topology: A mix of two or more types.
Each topology has its strengths and weaknesses, but when it comes to security, the design must focus on protecting data and controlling access.
What Does Secure Network Topology Mean?
Secure network topology refers to designing and organizing a network in a way that minimizes vulnerabilities and protects against unauthorized access or attacks. It combines the physical and logical layout of the network with security measures to create a safe environment.
Key aspects include:
- Segmentation: Dividing the network into smaller parts to limit access.
- Access Control: Defining who can access what.
- Monitoring: Keeping an eye on traffic and devices.
- Redundancy: Having backup paths to avoid single points of failure.
By carefully planning these elements, you reduce the risk of breaches and make it easier to detect and respond to threats.
Why is Secure Network Topology Important?
You might wonder why network topology matters for security. Here’s why:
- Limits Damage: If one part is compromised, segmentation stops the attacker from moving freely.
- Improves Performance: Secure designs often improve traffic flow and reduce congestion.
- Simplifies Management: Clear structure helps in monitoring and updating security policies.
- Supports Compliance: Many regulations require secure network designs.
In today’s world, cyberattacks are more frequent and sophisticated. A secure network topology is your first line of defense.
Key Principles of Secure Network Topology
When designing a secure network topology, consider these principles:
1. Network Segmentation
Breaking your network into smaller zones helps control access and contain threats.
- Use VLANs (Virtual Local Area Networks) to separate departments.
- Create DMZs (Demilitarized Zones) for public-facing servers.
- Isolate sensitive data and systems.
2. Least Privilege Access
Only allow users and devices the minimum access they need.
- Implement role-based access control (RBAC).
- Use firewalls to restrict traffic between segments.
- Regularly review permissions.
3. Defense in Depth
Layer multiple security measures to protect the network.
- Combine firewalls, intrusion detection systems (IDS), and antivirus.
- Use encryption for data in transit.
- Employ strong authentication methods.
4. Redundancy and Failover
Ensure the network stays secure even if parts fail.
- Use multiple paths for critical connections.
- Have backup devices ready.
- Monitor network health continuously.
Common Secure Network Topology Designs
Here are some popular secure network topologies used in organizations:
Star Topology with Segmentation
- Central switch or router connects all devices.
- VLANs separate traffic by department or function.
- Firewalls control access between VLANs.
Mesh Topology for Critical Systems
- Devices connect directly to multiple others.
- Provides redundancy and resilience.
- Often used in data centers or core networks.
Hybrid Topology with DMZ
- Combines star, mesh, and bus topologies.
- Public servers placed in DMZ, isolated from internal network.
- Internal network segmented for security.
How to Design a Secure Network Topology
Designing a secure network topology involves several steps:
Step 1: Assess Your Needs
- Identify critical assets and data.
- Understand user roles and access requirements.
- Analyze potential threats.
Step 2: Choose the Right Topology
- Pick a topology that fits your size and complexity.
- Consider scalability and future growth.
Step 3: Implement Segmentation
- Use VLANs and subnets to separate traffic.
- Create DMZs for external-facing services.
Step 4: Apply Access Controls
- Set firewall rules between segments.
- Use authentication and authorization.
Step 5: Monitor and Maintain
- Deploy IDS/IPS systems.
- Regularly update software and hardware.
- Conduct security audits.
Tools and Technologies Supporting Secure Network Topology
Several tools help build and maintain secure network topologies:
- Firewalls: Control traffic between network segments.
- VLANs: Logical segmentation of networks.
- Intrusion Detection/Prevention Systems (IDS/IPS): Detect and block attacks.
- Network Access Control (NAC): Enforce policies on devices connecting to the network.
- VPNs: Secure remote access.
- Security Information and Event Management (SIEM): Centralized monitoring and alerting.
Using these tools together strengthens your network’s security posture.
Challenges in Implementing Secure Network Topology
Designing and maintaining a secure network topology isn’t without challenges:
- Complexity: More segmentation means more management.
- Cost: Advanced hardware and software can be expensive.
- User Resistance: Strict access controls may frustrate users.
- Evolving Threats: Attackers constantly find new ways in.
To overcome these, balance security with usability and keep updating your defenses.
Real-World Example: Secure Network Topology in a Healthcare Organization
Healthcare organizations handle sensitive patient data, making secure network topology critical.
- They use segmentation to separate patient records from general office systems.
- DMZs host public websites without exposing internal networks.
- Strict access controls limit who can see medical data.
- Continuous monitoring detects unusual activity quickly.
This approach helps protect patient privacy and comply with regulations like HIPAA.
Conclusion
Understanding what secure network topology is helps you build networks that protect your data and systems. It’s about more than just connecting devices; it’s about connecting them safely.
By applying principles like segmentation, least privilege, and defense in depth, you can reduce risks and improve your network’s resilience. Whether you’re managing a small business or a large enterprise, investing time in secure network design pays off in stronger security and peace of mind.
FAQs
What is the main goal of secure network topology?
The main goal is to protect network resources by organizing devices and connections to minimize vulnerabilities and control access, reducing the risk of cyberattacks.
How does network segmentation improve security?
Segmentation divides the network into smaller parts, limiting access and containing threats, so attackers can’t easily move across the entire network.
What role do firewalls play in secure network topology?
Firewalls control traffic between network segments, enforcing security policies and blocking unauthorized access.
Can secure network topology prevent all cyberattacks?
No, but it significantly reduces risks by limiting attack surfaces and improving detection and response capabilities.
Is secure network topology only for large organizations?
No, businesses of all sizes benefit from secure network design to protect their data and systems effectively.





