What is Sandboxing
Introduction
You might have heard the term "sandboxing" when talking about computer security or software development. But what exactly is sandboxing, and why is it so important today? In simple terms, sandboxing is a way to create a safe space where programs or files can run without affecting the rest of your system.
If you want to protect your computer from harmful software or test new apps without risk, sandboxing is a powerful tool. In this article, I’ll explain what sandboxing means, how it works, and why it matters for both everyday users and professionals.
What Is Sandboxing?
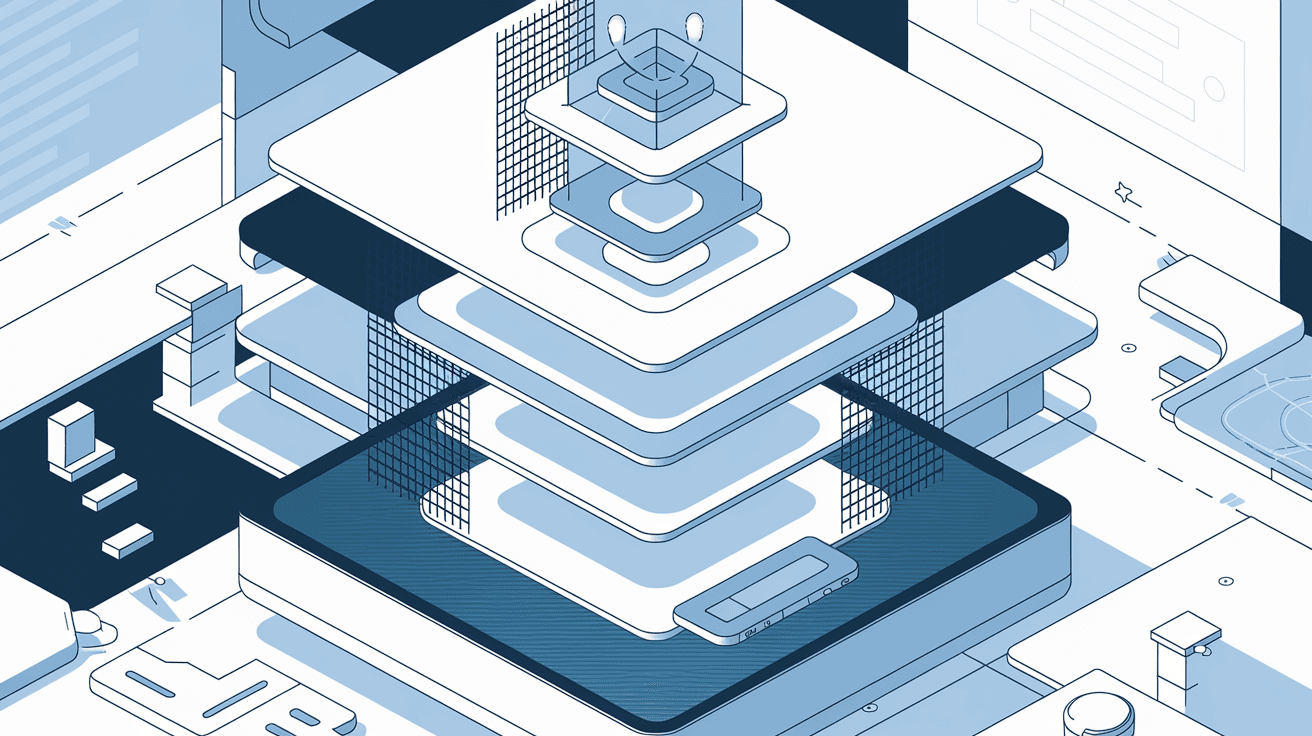
Sandboxing is a security technique that isolates programs or processes from the main system. Think of it like a playpen for software — it lets the program run freely but keeps it contained so it can’t cause damage outside the sandbox.
This isolation helps prevent malware, viruses, or buggy software from affecting your computer or network. Sandboxes create a controlled environment where software can be tested or executed safely.
How Sandboxing Works
- Isolation: The sandbox separates the program from the operating system and other apps.
- Restricted Access: Programs inside the sandbox have limited access to files, network, or hardware.
- Temporary Environment: Changes made inside the sandbox don’t affect the real system and are usually discarded after use.
By doing this, sandboxing limits the potential harm caused by unknown or untrusted software.
Types of Sandboxing
There are different ways to implement sandboxing depending on the purpose and technology used. Here are some common types:
Application Sandboxing
This type isolates a single app from the rest of the system. It’s often used on smartphones and modern operating systems to protect user data.
- Apps can only access their own files and data.
- They can’t interfere with other apps or system settings.
- Examples include iOS and Android app sandboxes.
Browser Sandboxing
Web browsers use sandboxing to protect your computer from malicious websites or harmful scripts.
- Each browser tab runs in its own sandbox.
- This prevents one tab from affecting others or the system.
- It helps block malware from spreading through the browser.
Virtual Machine Sandboxing
Virtual machines (VMs) create a full, separate operating system inside your computer.
- VMs run independently from the host system.
- They are used for testing software or running different OS versions.
- If malware infects the VM, it doesn’t affect the host.
Container Sandboxing
Containers package software and its dependencies in a lightweight, isolated environment.
- Containers share the host OS kernel but keep apps separated.
- Popular in software development and cloud computing.
- Examples include Docker and Kubernetes.
Why Is Sandboxing Important?
Sandboxing plays a crucial role in cybersecurity and software development. Here’s why it matters:
Protects Against Malware and Cyberattacks
Malware often tries to spread or access sensitive data. Sandboxing stops this by isolating suspicious programs.
- Malware inside a sandbox can’t harm the real system.
- Security teams can analyze malware behavior safely.
- It reduces the risk of data breaches and system damage.
Enables Safe Software Testing
Developers use sandboxes to test new software or updates without risking their main system.
- Bugs or crashes stay contained.
- Developers can experiment freely.
- It speeds up the development process.
Enhances Privacy and Security
Sandboxing limits what apps or websites can access on your device.
- Prevents apps from stealing data.
- Blocks unauthorized access to files or hardware.
- Helps enforce security policies.
Supports Compliance and Risk Management
Organizations use sandboxing to meet security standards and reduce operational risks.
- It helps isolate sensitive data.
- Supports controlled testing environments.
- Assists in auditing and monitoring software behavior.
How Sandboxing Is Used in Cybersecurity
Sandboxing is a key defense tool against modern cyber threats. Here’s how it fits into cybersecurity strategies:
Malware Analysis
Security experts run suspicious files in sandboxes to observe their behavior.
- They check if the file tries to connect to malicious servers.
- They see if it attempts to modify system files.
- This helps identify new malware strains quickly.
Email and Web Filtering
Many email and web security solutions use sandboxing to scan attachments and links.
- Suspicious attachments open in a sandbox before delivery.
- Unsafe websites are loaded in isolated environments.
- This prevents threats from reaching users.
Endpoint Protection
Antivirus and endpoint security tools integrate sandboxing to block unknown threats.
- Unknown programs run in sandboxes before full execution.
- Harmful actions are detected and stopped early.
- This adds an extra layer of defense.
Examples of Sandboxing Tools and Technologies
If you want to try sandboxing or learn more, here are some popular tools and platforms:
| Tool/Platform | Type | Use Case |
| Sandboxie | Application Sandbox | Run Windows apps safely |
| Firejail | Linux Application | Isolate Linux apps |
| Docker | Container Sandbox | Develop and deploy apps |
| VMware Workstation | Virtual Machine | Run multiple OS on one computer |
| Google Chrome | Browser Sandbox | Secure web browsing |
| Microsoft Defender ATP | Endpoint Protection | Malware sandboxing and analysis |
These tools help users and organizations apply sandboxing in different environments.
How to Use Sandboxing as a User
You don’t have to be a tech expert to benefit from sandboxing. Here are some simple ways you can use it:
- Use browsers like Google Chrome or Microsoft Edge that have built-in sandboxing.
- Run suspicious email attachments or downloads inside sandbox apps like Sandboxie.
- Use virtual machines to test unknown software safely.
- Keep your operating system and security software updated to use sandbox features.
By taking these steps, you reduce the risk of infections and keep your data safe.
Challenges and Limitations of Sandboxing
While sandboxing is powerful, it’s not perfect. Here are some challenges:
- Performance Impact: Running software in a sandbox can slow it down.
- Complexity: Setting up sandboxes for advanced use requires technical knowledge.
- Bypassing Techniques: Some malware can detect sandboxes and avoid running.
- Limited Scope: Sandboxing protects only what’s inside it; other attack vectors remain.
Understanding these limits helps you use sandboxing wisely alongside other security measures.
Future of Sandboxing
Sandboxing continues to evolve with technology trends like cloud computing, AI, and IoT.
- Cloud providers use sandboxing to isolate workloads and improve security.
- AI helps detect sandbox evasion techniques and improve malware analysis.
- Sandboxing is expanding to protect smart devices and connected systems.
As threats grow more complex, sandboxing will remain a key part of defense strategies.
Conclusion
Sandboxing is a simple but powerful way to keep your computer and data safe. By isolating programs and processes, it stops malware and risky software from causing harm. Whether you’re a developer testing new apps or a user browsing the web, sandboxing adds an important layer of protection.
You can use sandboxing through browsers, virtual machines, or specialized tools to create safe environments. While it has some challenges, sandboxing remains essential in today’s digital world. Understanding how it works helps you stay secure and confident in using technology.
FAQs
What is the main purpose of sandboxing?
Sandboxing isolates programs to prevent them from affecting the main system. It protects against malware and allows safe software testing.
Can sandboxing stop all types of malware?
Sandboxing helps block many threats but isn’t foolproof. Some malware can detect sandboxes and avoid running.
Is sandboxing only for experts?
No, many everyday tools like browsers use sandboxing automatically. Users can also try simple sandbox apps.
How does sandboxing improve software testing?
It lets developers run new software in a safe space, so bugs don’t affect the main system.
Are virtual machines the same as sandboxes?
Virtual machines are a type of sandbox that runs a full separate OS, offering strong isolation.





