What is Root Certificate
Introduction
You might have heard about root certificates when dealing with internet security or setting up websites. But what exactly is a root certificate, and why should you care? Understanding root certificates helps you see how your data stays safe when you browse the web or use apps.
In this article, I’ll explain what a root certificate is in simple terms. We’ll explore how it works, why it’s important, and how it fits into the bigger picture of online security. By the end, you’ll know why root certificates are a key part of keeping your information private and secure.
What Is a Root Certificate?
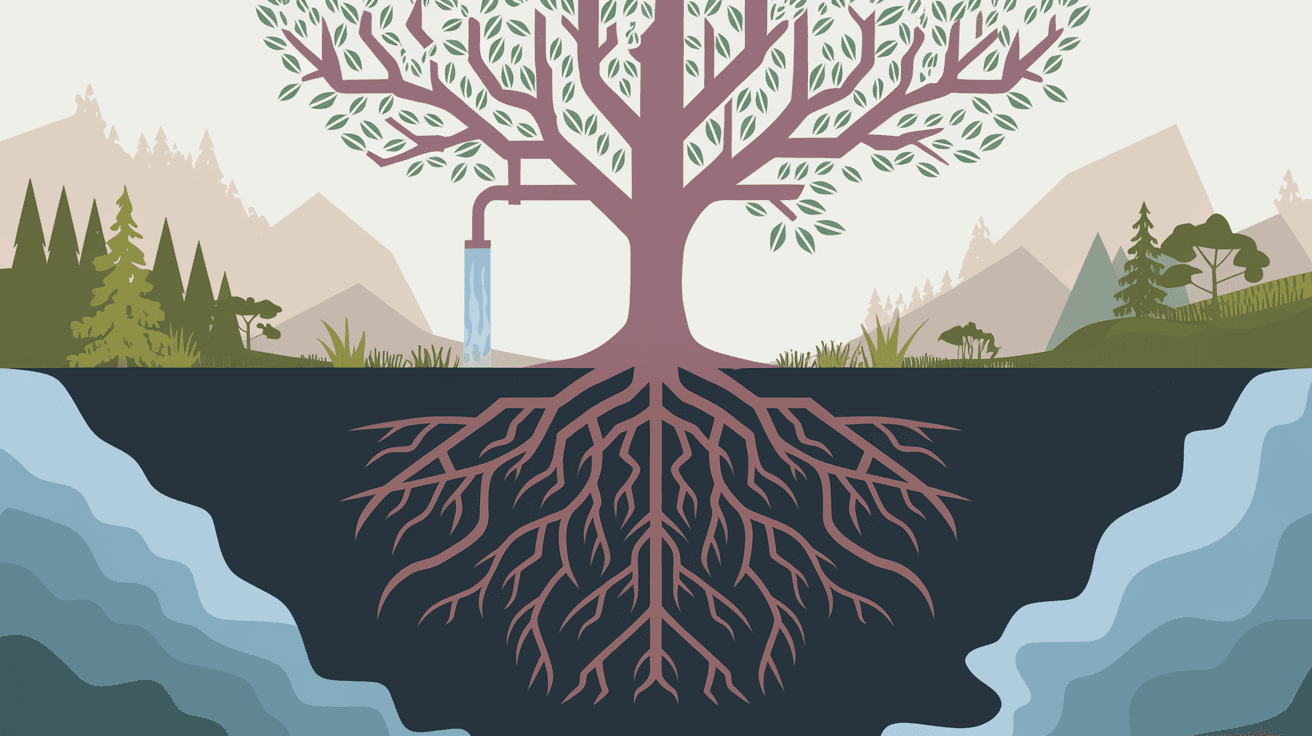
A root certificate is a special type of digital certificate. It acts as the foundation of trust for all other certificates on the internet. Think of it as the "master key" that helps verify if a website or service is safe to use.
Root certificates are issued by trusted organizations called Certificate Authorities (CAs). These CAs are responsible for confirming the identity of websites and companies. When your browser or device sees a root certificate, it trusts it because it comes from a known and reliable source.
How Root Certificates Work
- Root certificates contain a public key and information about the CA.
- They are self-signed, meaning the CA signs its own certificate.
- Devices and browsers store a list of trusted root certificates.
- When you visit a website, your browser checks the site's certificate against these root certificates.
- If the chain of trust leads back to a trusted root certificate, your browser accepts the site as secure.
This process is called the chain of trust, and it ensures that the website you visit is legitimate and not an imposter.
Why Are Root Certificates Important?
Root certificates are crucial because they help secure online communication. Without them, it would be very hard to know if a website is safe or if your data is being intercepted.
Here’s why root certificates matter:
- Secure Browsing: They enable HTTPS connections, which encrypt data between you and websites.
- Authentication: They verify that websites are who they claim to be.
- Data Integrity: They ensure that information sent and received has not been tampered with.
- Trust: They build a trusted environment for online transactions, emails, and software updates.
Without root certificates, hackers could easily create fake websites and steal your personal information.
How Root Certificates Are Managed
Root certificates are stored in a special place called the root store on your device or browser. This store contains all the trusted root certificates your system recognizes.
Who Manages Root Stores?
- Operating systems like Windows, macOS, and Linux maintain their own root stores.
- Browsers like Chrome and Firefox also have their own root stores.
- Certificate Authorities apply to be included in these root stores after strict security checks.
Updating Root Certificates
Root certificates don’t last forever. They have expiration dates and sometimes need to be revoked if compromised. Your device or browser regularly updates its root store to add new trusted certificates and remove old or unsafe ones.
The Chain of Trust Explained
When you visit a secure website, your browser checks the website’s certificate. But that certificate is usually not a root certificate itself. Instead, it’s signed by an intermediate certificate, which is signed by another intermediate, and so on, until the chain reaches a root certificate.
Here’s how the chain of trust works:
- Website Certificate: The certificate presented by the website.
- Intermediate Certificates: Certificates that link the website certificate to the root certificate.
- Root Certificate: The trusted certificate at the top of the chain.
If any link in this chain is broken or untrusted, your browser will warn you that the site is not secure.
Examples of Root Certificate Authorities
Some well-known Certificate Authorities that issue root certificates include:
- DigiCert: One of the largest CAs, trusted by most browsers.
- Let's Encrypt: Provides free certificates and has a trusted root certificate.
- GlobalSign: Offers certificates for businesses and individuals.
- Comodo (now Sectigo): A popular CA with a wide range of certificates.
These organizations follow strict security standards to maintain trust.
How Root Certificates Affect You Daily
You interact with root certificates every day without noticing. Here are some common examples:
- When you visit a website with HTTPS, your browser checks the root certificate.
- When you install software, the installer’s certificate is verified.
- When you send or receive encrypted emails, root certificates help verify identities.
- When your device updates its software, root certificates ensure the update is legitimate.
If a root certificate is missing or untrusted, you might see warnings like "Your connection is not private" or "Untrusted Certificate."
Risks and Challenges with Root Certificates
While root certificates are essential, they also come with risks:
- Compromise: If a root certificate is hacked, attackers can issue fake certificates.
- Misissuance: Sometimes CAs mistakenly issue certificates to the wrong parties.
- Trust Abuse: Malicious actors might exploit trusted certificates for phishing or malware.
To reduce these risks, browsers and operating systems monitor CAs closely and can revoke trust if needed.
How to Check Root Certificates on Your Device
You can view the root certificates trusted by your device or browser. Here’s how:
On Windows
- Open the Certificate Manager by typing
certmgr.mscin the Run dialog. - Navigate to Trusted Root Certification Authorities > Certificates.
- You’ll see a list of root certificates installed on your system.
On macOS
- Open Keychain Access.
- Select the System Roots keychain.
- Browse the list of root certificates.
On Browsers
- In Chrome, go to Settings > Privacy and Security > Security > Manage Certificates.
- In Firefox, go to Options > Privacy & Security > Certificates > View Certificates.
How to Stay Safe with Root Certificates
To keep your online activities secure, follow these tips:
- Keep your operating system and browser updated to get the latest root certificates.
- Avoid ignoring security warnings about certificates.
- Use reputable antivirus and security software.
- Only download software and certificates from trusted sources.
Being cautious helps protect you from fake certificates and malicious websites.
Conclusion
Root certificates are the backbone of internet security. They help your browser trust websites, keep your data safe, and protect your online identity. By understanding what root certificates are and how they work, you can better appreciate the invisible security that protects your daily internet use.
Remember, root certificates are managed by trusted authorities and regularly updated to maintain safety. Staying aware of their role helps you navigate the web more securely and confidently.
FAQs
What is the difference between a root certificate and an SSL certificate?
A root certificate is the top-level trusted certificate issued by a Certificate Authority. An SSL certificate is issued to a website and is verified through a chain that leads back to a root certificate.
Can root certificates expire?
Yes, root certificates have expiration dates. When they expire, they must be renewed or replaced to maintain trust in the certificate chain.
How do browsers decide which root certificates to trust?
Browsers maintain a root store with certificates from trusted Certificate Authorities. They include only those CAs that meet strict security and policy requirements.
What happens if a root certificate is compromised?
If a root certificate is compromised, browsers and operating systems revoke trust in it. This prevents attackers from using fake certificates issued by that root.
Can I add my own root certificate to my device?
Yes, you can manually add root certificates to your device’s root store, but this should be done carefully to avoid security risks. It’s usually done in enterprise environments.





