What is Reverse Proxy Security
Introduction
You might have heard about reverse proxy security but wonder what it really means and why it matters. In simple terms, reverse proxy security is a way to protect your website or web application by acting as a middleman between users and your servers. It helps keep your data safe, improves performance, and blocks harmful traffic.
In this article, I’ll explain what reverse proxy security is, how it works, and why you should consider using it. Whether you run a small blog or a large online store, understanding this concept can help you keep your online presence secure and reliable.
What is a Reverse Proxy?
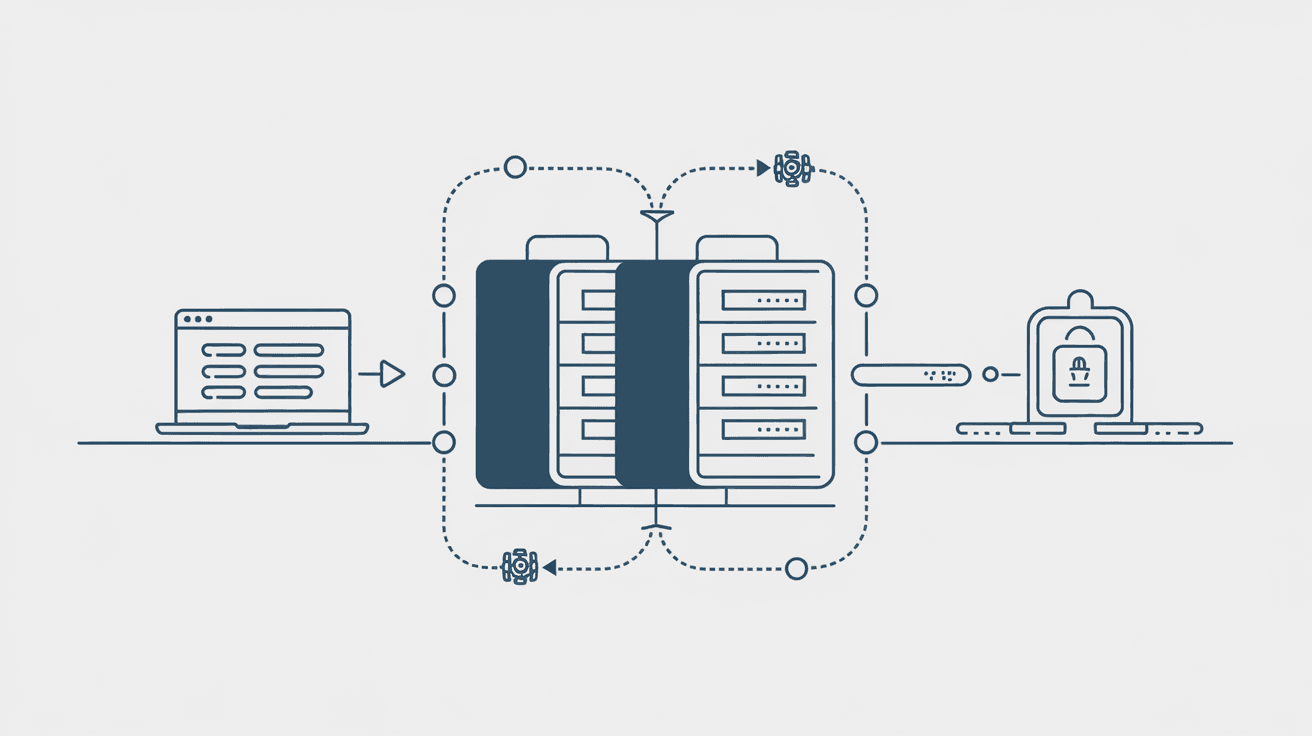
A reverse proxy is a server that sits between your users and your web servers. When someone visits your website, their request first goes to the reverse proxy. The proxy then forwards the request to your actual server, collects the response, and sends it back to the user.
This setup is different from a forward proxy, which acts on behalf of the client to access other servers. The reverse proxy acts on behalf of the server to manage incoming traffic.
Key Functions of a Reverse Proxy
- Load balancing: Distributes incoming traffic evenly across multiple servers.
- Caching: Stores copies of web pages to speed up response times.
- SSL termination: Handles encryption and decryption of secure connections.
- Security filtering: Blocks malicious requests before they reach your server.
By controlling traffic this way, a reverse proxy can improve your website’s speed, reliability, and security.
How Reverse Proxy Enhances Security
Reverse proxy security focuses on protecting your backend servers from attacks and unauthorized access. It acts as a shield, filtering out harmful traffic and hiding your server’s real IP address.
Main Security Benefits
- Hides server identity: The reverse proxy masks your server’s IP, making it harder for attackers to target it directly.
- Blocks malicious traffic: It can detect and block threats like SQL injection, cross-site scripting (XSS), and other web attacks.
- Prevents DDoS attacks: By filtering and limiting traffic, it helps protect against Distributed Denial of Service attacks that try to overwhelm your server.
- Enforces access control: You can set rules to allow or deny access based on IP addresses, geolocation, or user agents.
- Manages SSL certificates: The proxy handles SSL/TLS encryption, ensuring secure communication without burdening your backend servers.
Examples of Security Features
- Web Application Firewall (WAF): Many reverse proxies include WAFs that inspect incoming requests for suspicious patterns.
- Rate limiting: Controls how many requests a user can make in a given time to prevent abuse.
- Bot filtering: Identifies and blocks automated bots that may scrape data or launch attacks.
Common Use Cases for Reverse Proxy Security
Reverse proxy security is widely used across industries and websites of all sizes. Here are some common scenarios where it plays a crucial role:
Protecting Web Applications
Web apps often face attacks targeting vulnerabilities in their code. A reverse proxy with security features can block these attacks before they reach the app, reducing the risk of data breaches.
Securing APIs
APIs are essential for modern apps but can be vulnerable to misuse. Reverse proxies help authenticate requests, limit traffic, and prevent unauthorized access.
Enhancing Cloud Security
Many cloud providers offer reverse proxy services to protect cloud-hosted applications. This adds an extra layer of defense beyond the cloud infrastructure.
Improving Performance and Security for E-commerce
Online stores handle sensitive customer data and payment information. Reverse proxies ensure secure connections and protect against fraud and attacks.
How to Implement Reverse Proxy Security
Setting up reverse proxy security involves choosing the right software or service and configuring it properly. Here’s a simple guide to get started:
Step 1: Choose a Reverse Proxy Solution
Popular options include:
- Nginx: A widely used open-source web server with reverse proxy capabilities.
- Apache HTTP Server: Supports reverse proxy modules.
- Cloudflare: A cloud-based service offering reverse proxy and security features.
- AWS CloudFront: Amazon’s content delivery network with reverse proxy functions.
- HAProxy: A high-performance proxy for load balancing and security.
Step 2: Configure Basic Proxy Settings
- Define the backend servers to forward requests to.
- Set up SSL certificates for secure connections.
- Enable caching and load balancing if needed.
Step 3: Enable Security Features
- Activate Web Application Firewall rules.
- Set rate limiting and bot filtering.
- Configure IP whitelisting or blacklisting.
- Monitor logs for suspicious activity.
Step 4: Test and Monitor
- Use tools like OWASP ZAP or Burp Suite to test security.
- Monitor traffic and alerts regularly.
- Update rules and software to stay protected against new threats.
Challenges and Considerations
While reverse proxy security offers many benefits, there are some challenges to keep in mind:
Complexity
Setting up and managing a reverse proxy requires technical knowledge. Misconfiguration can lead to security gaps or performance issues.
Performance Overhead
Adding a proxy layer can introduce slight delays. Proper tuning and hardware resources are necessary to minimize impact.
Single Point of Failure
If the reverse proxy goes down, your website may become unavailable. Using redundant proxies and failover mechanisms helps avoid this.
Compatibility
Some applications or protocols may not work well behind a reverse proxy without special configuration.
Future Trends in Reverse Proxy Security
As cyber threats evolve, reverse proxy security continues to improve. Here are some trends shaping its future:
- AI-powered threat detection: Using machine learning to identify new attack patterns faster.
- Zero Trust security models: Integrating reverse proxies into broader zero trust frameworks.
- Edge computing integration: Deploying reverse proxies closer to users for faster and safer connections.
- API security enhancements: More advanced controls for API traffic filtering and authentication.
These developments will make reverse proxy security even more essential for protecting online services.
Conclusion
Reverse proxy security is a powerful tool to protect your website or application from cyber threats. By acting as a gatekeeper, it hides your servers, filters harmful traffic, and ensures secure connections. Whether you want to stop hackers, prevent DDoS attacks, or improve performance, a reverse proxy can help.
Implementing reverse proxy security might seem complex at first, but with the right tools and setup, it becomes a vital part of your online defense. As threats grow, using a reverse proxy is a smart step to keep your digital presence safe and reliable.
FAQs
What is the difference between a reverse proxy and a forward proxy?
A reverse proxy acts on behalf of servers to manage incoming traffic, while a forward proxy acts on behalf of clients to access external servers. Reverse proxies protect servers; forward proxies protect clients.
Can a reverse proxy prevent all cyber attacks?
No single solution can stop all attacks. A reverse proxy improves security by filtering traffic and blocking many threats, but it should be part of a broader security strategy.
Is reverse proxy security suitable for small websites?
Yes, even small websites benefit from reverse proxy security to protect against common attacks and improve performance, especially when using cloud-based proxy services.
How does a reverse proxy help with SSL/TLS?
A reverse proxy can handle SSL/TLS encryption and decryption, offloading this work from backend servers and simplifying certificate management.
What happens if the reverse proxy server fails?
If the reverse proxy fails, users may lose access to your website. To avoid downtime, use multiple proxies with failover and load balancing configurations.





