What is Process Injection
Introduction
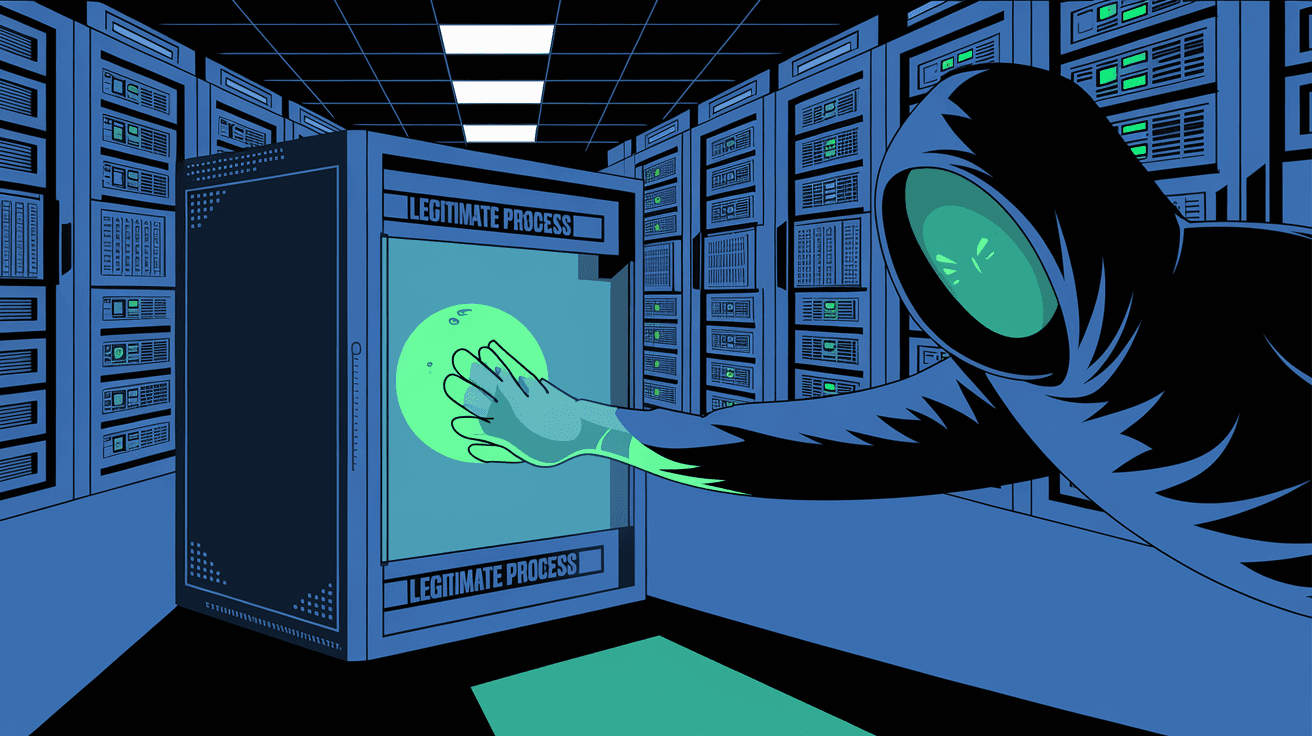
You might have heard the term "process injection" in cybersecurity discussions or software development talks. But what exactly is it? Simply put, process injection is a technique where one program inserts code into another running process. This allows the injected code to run within the target process’s space, often to manipulate or control it.
Understanding process injection is important because it plays a big role in both legitimate software operations and malicious attacks. In this article, I’ll explain what process injection is, how it works, and why it matters to you, whether you're a developer, security professional, or just curious about how software behaves.
What Is Process Injection?
Process injection is a method used to run code inside another process’s memory space. Instead of running separately, the injected code becomes part of the target process. This can change how the process behaves or allow the injected code to hide itself.
How Process Injection Works
- A process (the injector) targets another process (the victim).
- The injector allocates memory inside the victim process.
- It writes its own code into that memory.
- The victim process is made to execute the injected code.
This technique is often used to bypass security controls or to hide malicious activities. However, it also has legitimate uses, such as debugging or extending software functionality.
Common Techniques of Process Injection
There are several ways to perform process injection, each with its own method and purpose. Here are some of the most common techniques:
1. DLL Injection
This involves forcing a target process to load a Dynamic Link Library (DLL). The DLL contains the code to be injected.
- The injector uses system calls to load the DLL into the target process.
- Once loaded, the DLL’s code runs inside the target process.
- This is often used for hooking functions or modifying behavior.
2. Code Injection
Instead of loading a DLL, raw code is injected directly into the target process’s memory.
- The injector allocates memory in the target process.
- It writes the code into this memory.
- The target process is directed to execute this code.
3. Thread Hijacking
This method involves taking control of an existing thread in the target process.
- The injector suspends a thread.
- It changes the thread’s instruction pointer to the injected code.
- The thread resumes and runs the injected code.
4. Reflective DLL Injection
A more advanced form of DLL injection where the DLL loads itself without using the operating system’s loader.
- This helps avoid detection by security software.
- The DLL contains code to load itself into memory.
- It runs entirely within the target process.
Why Is Process Injection Used?
Process injection is a powerful tool with both good and bad uses. Here’s why it’s commonly used:
Legitimate Uses
- Debugging and Profiling: Developers inject code to monitor or analyze running processes.
- Software Extensions: Some programs inject code to add features or fix bugs without restarting.
- Security Tools: Antivirus or monitoring software may use injection to scan or protect processes.
Malicious Uses
- Malware Concealment: Attackers inject code to hide malware inside trusted processes.
- Privilege Escalation: Injected code can run with the target process’s permissions.
- Bypassing Security: Injection can avoid detection by running inside legitimate processes.
How Process Injection Works on Different Operating Systems
Process injection techniques vary depending on the operating system. Here’s a brief look at how it works on Windows and Linux.
Windows
Windows provides APIs that make process injection easier:
- OpenProcess: Opens the target process.
- VirtualAllocEx: Allocates memory in the target process.
- WriteProcessMemory: Writes code into the allocated memory.
- CreateRemoteThread: Starts a new thread in the target process to run the injected code.
Windows is the most common platform for process injection because of its widespread use and rich API set.
Linux
Linux uses different methods, often involving:
- ptrace: A system call that allows one process to control another.
- /proc filesystem: Accessing process memory via
/proc/[pid]/mem. - LD_PRELOAD: Preloading shared libraries to inject code at process start.
Linux injection is generally more complex but still widely used in both legitimate and malicious contexts.
Risks and Security Concerns
Process injection poses significant security risks because it can be used to hide malicious activities. Here are some concerns:
- Malware Evasion: Injected code can run inside trusted processes, making detection harder.
- Data Theft: Attackers can steal sensitive data by injecting code into processes handling that data.
- System Instability: Poorly written injected code can crash the target process or system.
- Privilege Abuse: Injection can allow attackers to escalate privileges.
Security tools now focus on detecting injection attempts by monitoring suspicious API calls and unusual process behavior.
How to Detect and Prevent Process Injection
Detecting process injection is challenging but possible with the right tools and practices.
Detection Methods
- Behavioral Analysis: Monitoring processes for unusual memory allocations or thread creations.
- API Monitoring: Watching for suspicious calls like
WriteProcessMemoryorCreateRemoteThread. - Memory Scanning: Checking process memory for injected code signatures.
- Heuristic Analysis: Using machine learning to spot abnormal process behavior.
Prevention Techniques
- Code Signing: Ensuring only trusted code runs in processes.
- Process Isolation: Running critical processes with minimal privileges.
- Endpoint Protection: Using antivirus and endpoint detection tools that monitor injection attempts.
- Patch Management: Keeping software updated to fix vulnerabilities that allow injection.
Real-World Examples of Process Injection
Process injection is not just theoretical; it’s used in many real-world scenarios.
Example 1: Malware Using DLL Injection
Many malware families use DLL injection to hide inside legitimate processes like explorer.exe. This helps them avoid detection by security software.
Example 2: Debuggers Using Injection
Debuggers inject code to pause or inspect running programs. This helps developers find bugs without stopping the entire system.
Example 3: Game Cheats
Some game cheats use process injection to modify game behavior in real-time, giving players unfair advantages.
Conclusion
Process injection is a powerful technique that lets one program run code inside another. It’s used in many areas, from software debugging to malware attacks. Understanding how it works helps you appreciate both its benefits and risks.
Whether you’re a developer, security expert, or just curious, knowing about process injection is important. It helps you recognize potential threats and understand how software can interact in complex ways. Staying informed and using proper security measures can protect you from the dangers of malicious injection.
FAQs
What is the main purpose of process injection?
Process injection allows one program to run code inside another process’s memory space, often to modify behavior or hide activities.
Is process injection always malicious?
No, process injection can be used for legitimate purposes like debugging, software extensions, and security monitoring.
How do attackers use process injection?
Attackers use it to hide malware, escalate privileges, and bypass security by running malicious code inside trusted processes.
Can process injection be detected?
Yes, through behavioral monitoring, API call tracking, memory scanning, and heuristic analysis.
What operating systems support process injection?
Both Windows and Linux support process injection, though the methods and tools differ between them.





