What is Password Spray Attack
Introduction
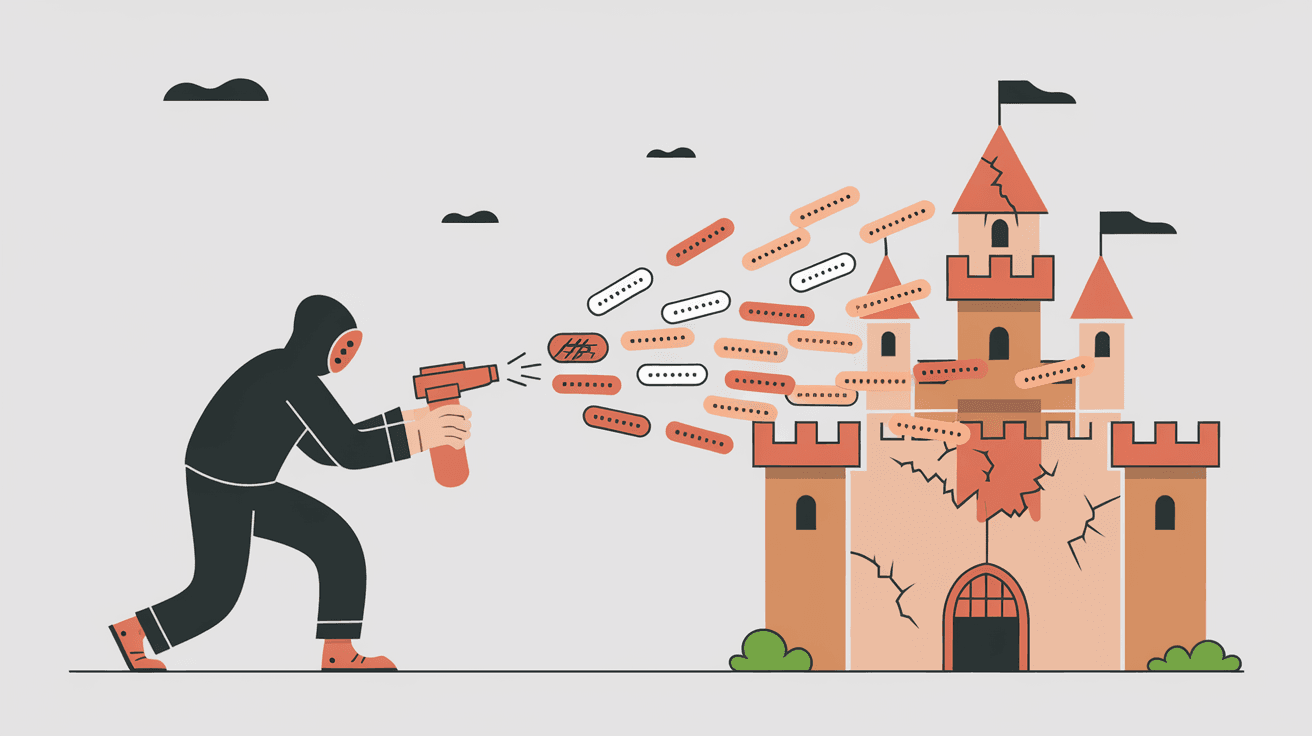
You might have heard about cyberattacks like phishing or ransomware, but have you come across the term "password spray attack"? It’s a sneaky way hackers try to break into accounts without raising alarms. Understanding this attack can help you protect your personal and work accounts better.
In this article, I’ll explain what a password spray attack is, how it works, and why it’s different from other hacking methods. You’ll also learn practical tips to defend yourself and your organization from this growing threat.
What is a Password Spray Attack?
A password spray attack is a type of cyberattack where hackers try a few common passwords across many different user accounts. Instead of guessing many passwords for one account, they guess one or two passwords for many accounts. This approach helps them avoid triggering security systems that lock accounts after multiple failed attempts.
How It Works
- Attackers collect a list of usernames or email addresses.
- They try a small number of common passwords (like "Password123" or "Welcome1") on each account.
- Because they only try a few passwords per account, they avoid detection.
- If a password matches, they gain access to that account.
This method is effective because many people still use weak or common passwords. It’s a low-effort, high-reward strategy for hackers.
Why Password Spray Attacks Are Dangerous
Password spray attacks are dangerous for several reasons:
- Stealthy: They avoid account lockouts by limiting login attempts per account.
- Wide Reach: Attackers target many accounts at once, increasing their chances of success.
- Access to Sensitive Data: Once inside, hackers can steal personal information, financial data, or company secrets.
- Gateway to Larger Attacks: Compromised accounts can be used to launch phishing campaigns or spread malware.
Organizations and individuals often underestimate this threat because it doesn’t look like a traditional brute force attack.
How Password Spray Attacks Differ from Brute Force Attacks
Both password spray and brute force attacks aim to guess passwords, but they work differently:
| Feature | Password Spray Attack | Brute Force Attack |
| Number of Passwords Tried | Few common passwords per account | Many passwords on a single account |
| Number of Accounts Targeted | Many accounts | Usually one account |
| Detection Risk | Low (avoids lockouts) | High (triggers lockouts) |
| Attack Speed | Slower but broader | Faster but focused |
Password spray attacks are more subtle and harder to detect, making them a favorite among cybercriminals.
Common Targets of Password Spray Attacks
Attackers often focus on accounts with weak security or high value. Common targets include:
- Corporate Email Accounts: Access to emails can reveal sensitive business information.
- Cloud Services: Platforms like Microsoft 365 or Google Workspace are popular targets.
- Government Systems: Public sector accounts often have valuable data.
- Social Media Accounts: Compromised accounts can spread misinformation or scams.
- Financial Accounts: Banks and payment services are lucrative targets.
Understanding who is at risk helps you prioritize your security efforts.
Signs You Might Be a Victim of a Password Spray Attack
It’s not always easy to spot a password spray attack, but some signs include:
- Unexpected login alerts from new devices or locations.
- Multiple failed login attempts reported by your system.
- Account lockouts without your action.
- Unusual activity like password changes or unfamiliar emails sent.
- Notifications from your IT team about suspicious login patterns.
If you notice these signs, act quickly to secure your accounts.
How to Protect Yourself from Password Spray Attacks
Protecting yourself requires a mix of good habits and technical measures. Here’s what you can do:
Use Strong, Unique Passwords
- Avoid common passwords like "123456" or "password."
- Use a mix of letters, numbers, and symbols.
- Consider using a password manager to generate and store complex passwords.
Enable Multi-Factor Authentication (MFA)
- MFA adds an extra layer of security by requiring a second form of verification.
- Even if a password is compromised, MFA can block unauthorized access.
Monitor Account Activity
- Regularly check login history and account settings.
- Set up alerts for suspicious activities.
Educate Yourself and Your Team
- Learn about phishing and social engineering tactics.
- Train employees to recognize and report suspicious behavior.
Implement Security Policies (For Organizations)
- Enforce password complexity and rotation policies.
- Use account lockout thresholds wisely.
- Deploy security tools that detect unusual login patterns.
How Organizations Detect and Respond to Password Spray Attacks
Organizations use several strategies to detect and stop password spray attacks:
- Behavioral Analytics: Monitoring login patterns to spot unusual activity.
- Rate Limiting: Restricting the number of login attempts from a single IP address.
- Threat Intelligence: Using data from other attacks to anticipate new threats.
- Security Information and Event Management (SIEM): Collecting and analyzing security alerts.
- Incident Response Plans: Preparing teams to act quickly when an attack is detected.
By combining these methods, companies reduce the risk of breaches and protect their data.
Real-World Examples of Password Spray Attacks
Several high-profile incidents have involved password spray attacks:
- In 2025, a major healthcare provider suffered a breach after attackers used password spray to access employee accounts. This led to exposure of patient records.
- Government agencies worldwide have reported increased password spray attempts targeting official email accounts.
- Cybercriminal groups often use password spray attacks as the first step in larger campaigns involving ransomware or data theft.
These examples show how serious and widespread this threat has become.
The Future of Password Spray Attacks
As cybersecurity improves, attackers adapt their methods. Password spray attacks are evolving with:
- AI-Powered Guessing: Using artificial intelligence to predict likely passwords based on user data.
- Credential Stuffing: Combining password spray with stolen password databases.
- Targeted Attacks: Focusing on high-value individuals with customized password lists.
To stay safe, you need to stay informed and update your security practices regularly.
Conclusion
Now you know that a password spray attack is a clever way hackers try to break into many accounts using a few common passwords. It’s different from brute force attacks because it’s quieter and targets many users at once. This makes it a serious threat for individuals and organizations alike.
By using strong passwords, enabling multi-factor authentication, and staying alert to suspicious activity, you can protect yourself from these attacks. Organizations must also invest in detection tools and employee training to defend against this growing risk. Staying informed and proactive is your best defense in today’s digital world.
FAQs
What is the main goal of a password spray attack?
The main goal is to gain unauthorized access by trying a few common passwords across many accounts, avoiding detection and account lockouts.
How can I tell if my account was targeted by a password spray attack?
Look for unusual login alerts, multiple failed login attempts, or unexpected password changes. These signs may indicate an attack.
Does using a strong password prevent password spray attacks?
Strong passwords reduce the risk, but enabling multi-factor authentication provides better protection against these attacks.
Are password spray attacks common in businesses?
Yes, especially in companies using cloud services. Attackers target many accounts to find weak passwords and gain access.
What tools help detect password spray attacks?
Security tools like SIEM systems, behavioral analytics, and rate limiting help detect and prevent these attacks effectively.





