What is NIST SP 800-171 Compliance
Introduction
If you work with the U.S. government or handle sensitive federal data, you’ve probably heard about NIST SP 800-171 compliance. But what exactly does it mean? Simply put, it’s a set of cybersecurity standards designed to protect controlled unclassified information (CUI) outside of federal systems.
Understanding NIST SP 800-171 compliance is crucial for businesses and contractors who want to secure sensitive data and meet government requirements. In this article, I’ll walk you through what it is, why it matters, and how you can achieve compliance effectively.
What is NIST SP 800-171?
NIST SP 800-171 is a publication by the National Institute of Standards and Technology (NIST). It provides guidelines for protecting Controlled Unclassified Information (CUI) in non-federal systems and organizations.
The goal is to ensure that sensitive government data remains secure when handled by contractors or other third parties. This standard is especially important for companies working with the Department of Defense (DoD) or other federal agencies.
Key Points About NIST SP 800-171
- Focuses on protecting CUI outside federal networks.
- Contains 110 security requirements grouped into 14 families.
- Applies to federal contractors and subcontractors.
- Helps prevent data breaches and cyber threats.
By following these guidelines, organizations can reduce the risk of exposing sensitive information to hackers or unauthorized users.
Why is NIST SP 800-171 Compliance Important?
You might wonder why NIST SP 800-171 compliance is such a big deal. The answer lies in the increasing number of cyberattacks targeting government data and contractors.
Protecting Sensitive Data
Federal agencies share sensitive information with contractors to complete projects. If this data falls into the wrong hands, it can compromise national security or lead to financial losses.
Meeting Contract Requirements
Many government contracts now require proof of NIST SP 800-171 compliance. Without it, companies may lose business opportunities or face penalties.
Enhancing Cybersecurity Posture
Compliance helps organizations build stronger cybersecurity defenses. It encourages best practices like access controls, incident response, and system monitoring.
Avoiding Legal and Financial Risks
Non-compliance can lead to fines, contract termination, or damage to reputation. Staying compliant reduces these risks and builds trust with government partners.
The 14 Control Families of NIST SP 800-171
NIST SP 800-171 organizes its 110 security requirements into 14 control families. Each family addresses a specific area of cybersecurity.
Here’s a quick overview:
| Control Family | Description |
| Access Control | Limits system access to authorized users. |
| Awareness and Training | Ensures personnel understand security risks. |
| Audit and Accountability | Tracks user activities and system events. |
| Configuration Management | Maintains secure system settings. |
| Identification and Authentication | Verifies user identities. |
| Incident Response | Plans for detecting and responding to incidents. |
| Maintenance | Manages system upkeep securely. |
| Media Protection | Protects data stored on physical media. |
| Personnel Security | Controls personnel access based on roles. |
| Physical Protection | Secures physical access to systems. |
| Risk Assessment | Identifies and manages cybersecurity risks. |
| Security Assessment | Evaluates security controls’ effectiveness. |
| System and Communications Protection | Safeguards data in transit and systems. |
| System and Information Integrity | Detects and corrects system flaws. |
Each family contains specific requirements that organizations must implement to protect CUI effectively.
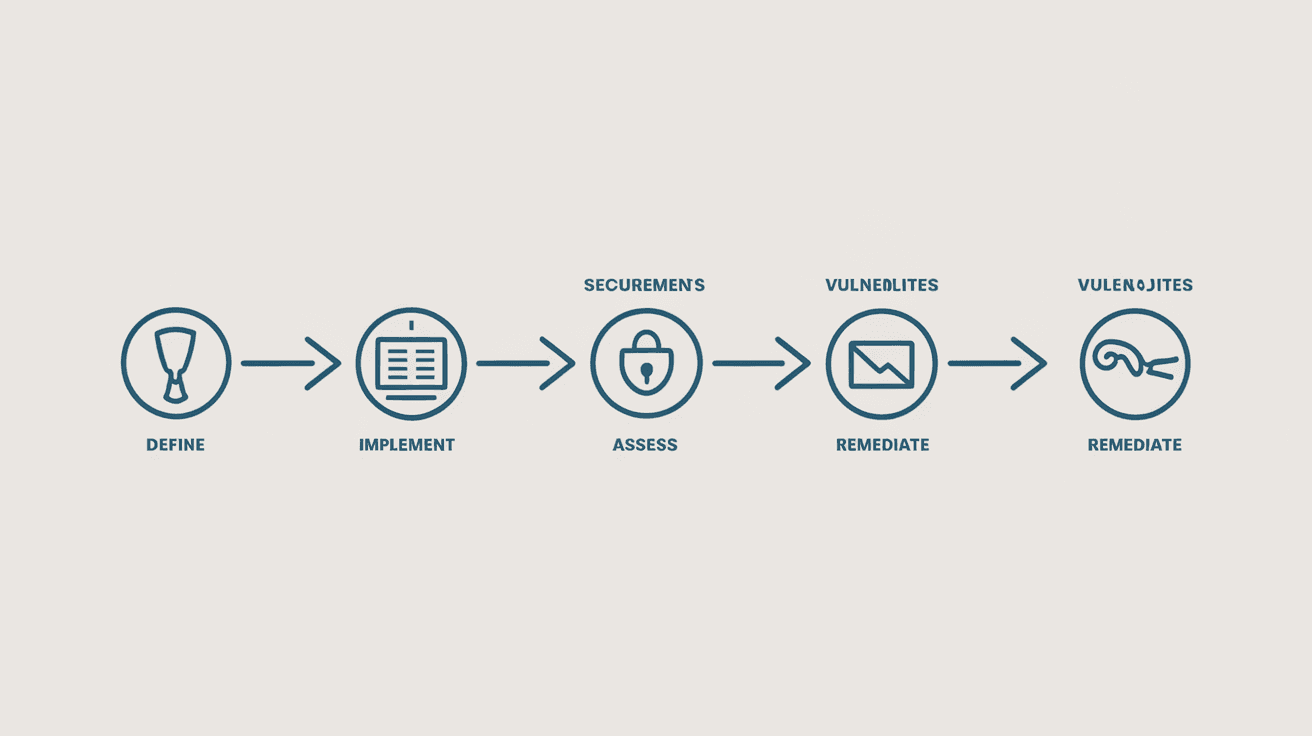
Steps to Achieve NIST SP 800-171 Compliance
Achieving compliance may seem overwhelming, but breaking it down into clear steps can help you manage the process.
1. Understand Your CUI
Identify what Controlled Unclassified Information your organization handles. Knowing where CUI resides is the first step to protecting it.
2. Conduct a Gap Analysis
Compare your current cybersecurity practices against NIST SP 800-171 requirements. This helps you spot areas needing improvement.
3. Develop a System Security Plan (SSP)
Document how your organization meets each security requirement. The SSP explains your security controls and policies.
4. Create a Plan of Action and Milestones (POA&M)
For any gaps found, develop a POA&M to outline how and when you will fix them.
5. Implement Security Controls
Put in place the necessary technical and administrative controls, such as access restrictions, encryption, and training.
6. Train Your Staff
Ensure employees understand their roles in protecting CUI and follow security policies.
7. Monitor and Maintain Compliance
Regularly review your security posture, update your SSP and POA&M, and respond to incidents promptly.
Common Challenges in NIST SP 800-171 Compliance
Many organizations face hurdles when trying to comply with NIST SP 800-171. Knowing these challenges can help you prepare better.
Limited Resources
Small and medium businesses often struggle with budget and staffing constraints to implement all controls.
Complex Requirements
The 110 controls can be difficult to interpret and apply without expert guidance.
Continuous Monitoring
Compliance is not a one-time effort. It requires ongoing monitoring and updates, which can be time-consuming.
Integration with Other Standards
Organizations may need to align NIST SP 800-171 with other cybersecurity frameworks like CMMC or ISO 27001.
Tools and Resources to Help with Compliance
Fortunately, there are many tools and resources available to simplify the compliance process.
Automated Assessment Tools
Software solutions can scan your systems and identify compliance gaps quickly.
Templates and Guides
NIST and other organizations provide templates for SSPs and POA&Ms to streamline documentation.
Training Programs
Online courses and workshops help your team understand and implement security controls.
Consulting Services
Cybersecurity experts can offer tailored advice and support to meet compliance requirements.
The Role of CMMC and NIST SP 800-171
The Cybersecurity Maturity Model Certification (CMMC) builds upon NIST SP 800-171. It adds a certification process to verify compliance for DoD contractors.
How They Work Together
- NIST SP 800-171 sets the baseline security requirements.
- CMMC introduces maturity levels and third-party assessments.
- Contractors must meet both to qualify for certain contracts.
Understanding this relationship is important if you want to work with the DoD or other federal agencies.
Conclusion
NIST SP 800-171 compliance is essential for protecting sensitive government data outside federal systems. By following its 110 security requirements, you can safeguard Controlled Unclassified Information and meet government contract demands.
While achieving compliance can be challenging, breaking it into clear steps and using available tools makes the process manageable. Staying compliant not only helps you avoid penalties but also strengthens your cybersecurity defenses in today’s threat landscape.
FAQs
What types of organizations need to comply with NIST SP 800-171?
Any organization that handles Controlled Unclassified Information (CUI) for the federal government, especially contractors and subcontractors, must comply with NIST SP 800-171.
How long does it take to become NIST SP 800-171 compliant?
The timeline varies depending on your current security posture, but it typically takes several months to a year to fully implement all controls and document compliance.
Is NIST SP 800-171 compliance mandatory?
For federal contractors handling CUI, compliance is mandatory to win and maintain government contracts. It’s also a best practice for cybersecurity.
Can small businesses meet NIST SP 800-171 requirements?
Yes, but small businesses may need to prioritize controls and seek external help due to limited resources.
How often should organizations update their compliance documentation?
Organizations should review and update their System Security Plan (SSP) and Plan of Action and Milestones (POA&M) at least annually or whenever significant changes occur.





