What is Network Sandboxing
Introduction
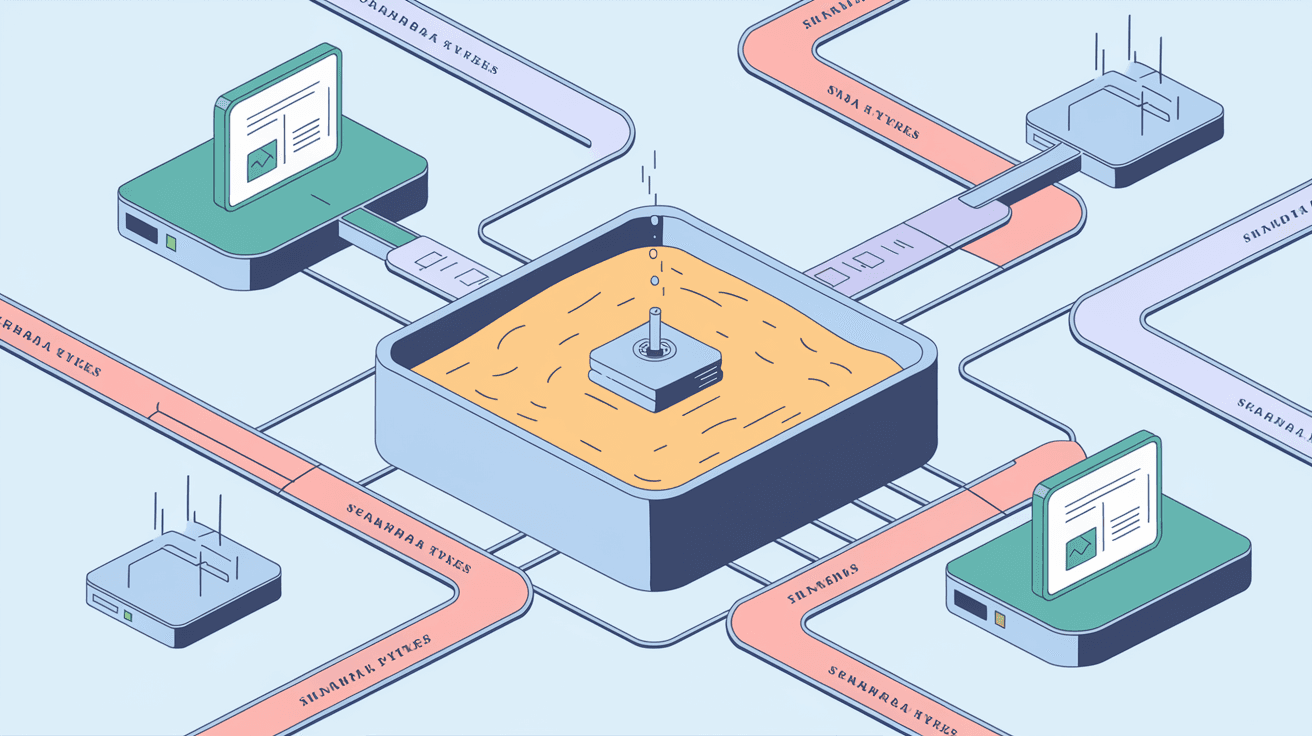
When you hear the term "network sandboxing," you might wonder what it means and why it matters. In simple terms, network sandboxing is a cybersecurity technique that helps protect your systems by isolating suspicious files or activities in a safe environment. This way, you can analyze threats without risking your entire network.
In this article, I’ll explain what network sandboxing is, how it works, and why it’s becoming a must-have tool for businesses and individuals alike. You’ll also learn about its benefits and how it fits into modern cybersecurity strategies.
What is Network Sandboxing?
Network sandboxing is a security method that creates a controlled, isolated environment—called a sandbox—where suspicious files, programs, or network traffic can be tested safely. Think of it as a virtual lab where you can observe how a file behaves without letting it affect your real network.
This technique is especially useful for detecting new or unknown malware. Instead of relying only on known virus signatures, sandboxing watches how a file acts. If it tries to do something harmful, like modifying system files or connecting to dangerous servers, the sandbox alerts you.
Key Features of Network Sandboxing
- Isolation: Suspicious elements run separately from the main network.
- Behavior Analysis: Monitors actions like file changes, network connections, and system calls.
- Threat Detection: Identifies zero-day attacks and polymorphic malware.
- Automated Reporting: Generates detailed reports on suspicious activity.
How Does Network Sandboxing Work?
Network sandboxing works by creating a virtual environment that mimics your real network but is completely separate. When a suspicious file or network packet arrives, it’s sent to this sandbox for testing.
Here’s a step-by-step look at the process:
- Capture Suspicious Data: The system identifies files, emails, or network traffic that look unusual.
- Redirect to Sandbox: These items are sent to the sandbox environment.
- Execute and Monitor: The sandbox runs the file or simulates the network behavior.
- Analyze Behavior: It watches for malicious actions like file encryption, data exfiltration, or unusual network requests.
- Generate Report: The sandbox produces a detailed analysis.
- Take Action: Based on the report, security teams can block or quarantine threats.
Types of Sandboxes
- Host-Based Sandboxes: Run on individual devices to test files locally.
- Network-Based Sandboxes: Analyze network traffic and files at the perimeter.
- Cloud-Based Sandboxes: Use cloud resources to scale analysis and share threat intelligence.
Why is Network Sandboxing Important?
Cyber threats are evolving fast. Traditional antivirus tools often miss new or sophisticated attacks. Network sandboxing fills this gap by focusing on behavior rather than just known signatures.
Here’s why it’s crucial:
- Detects Unknown Threats: It can spot zero-day malware that hasn’t been seen before.
- Prevents Data Breaches: By isolating threats early, it stops attackers from stealing sensitive information.
- Improves Incident Response: Detailed reports help security teams respond faster and more effectively.
- Supports Compliance: Many regulations require advanced threat detection methods like sandboxing.
Benefits of Network Sandboxing
Using network sandboxing offers several advantages for your cybersecurity strategy:
- Enhanced Security: It adds an extra layer of defense against sophisticated attacks.
- Reduced False Positives: Behavior analysis helps avoid blocking safe files mistakenly.
- Faster Threat Detection: Automated sandboxing speeds up identifying malicious activity.
- Cost-Effective: Preventing breaches saves money on recovery and fines.
- Scalability: Cloud-based sandboxes can handle large volumes of data easily.
Common Use Cases for Network Sandboxing
Network sandboxing is versatile and fits many cybersecurity needs. Here are some common scenarios where it shines:
- Email Security: Scanning attachments and links before delivery.
- Web Traffic Analysis: Testing downloads and scripts from websites.
- Endpoint Protection: Isolating suspicious files on user devices.
- Threat Intelligence Sharing: Collaborating with other organizations to improve detection.
- Incident Investigation: Deep-diving into suspicious activity after an alert.
Challenges and Limitations of Network Sandboxing
While network sandboxing is powerful, it’s not perfect. Here are some challenges to keep in mind:
- Evasion Techniques: Some malware can detect sandboxes and hide malicious behavior.
- Resource Intensive: Running many sandboxes requires computing power and storage.
- False Negatives: Not all threats show harmful behavior immediately.
- Complex Setup: Integrating sandboxing into existing systems can be tricky.
Despite these challenges, sandboxing remains a vital tool when combined with other security measures.
How to Implement Network Sandboxing Effectively
If you want to add network sandboxing to your security setup, consider these tips:
- Choose the Right Type: Decide between host-based, network-based, or cloud-based sandboxes based on your needs.
- Integrate with Existing Tools: Connect sandboxing with firewalls, antivirus, and SIEM systems.
- Automate Analysis: Use automated workflows to speed up threat detection and response.
- Regularly Update: Keep sandbox environments updated to handle new malware techniques.
- Train Your Team: Make sure your security staff understands how to use sandbox reports.
Future Trends in Network Sandboxing
As cyber threats evolve, so does sandboxing technology. Here are some trends shaping its future:
- AI and Machine Learning: Using AI to improve behavior analysis and reduce false positives.
- Cloud-Native Sandboxing: More organizations will adopt cloud-based solutions for scalability.
- Integration with Zero Trust: Sandboxing will play a key role in zero trust security models.
- Real-Time Analysis: Faster sandboxing will enable immediate threat blocking.
- Collaboration Platforms: Sharing sandbox data across industries to improve collective defense.
Conclusion
Network sandboxing is a powerful cybersecurity tool that helps you detect and analyze threats safely. By isolating suspicious files and network traffic, it protects your systems from unknown malware and advanced attacks. Whether you run a small business or a large enterprise, sandboxing adds an essential layer of defense.
As cyber threats continue to grow, adopting network sandboxing can improve your security posture and help you respond faster to incidents. With the right setup and ongoing updates, sandboxing will remain a key part of your cybersecurity strategy for years to come.
FAQs
What types of threats can network sandboxing detect?
Network sandboxing detects malware, ransomware, zero-day attacks, and phishing attempts by analyzing suspicious files and network behavior in an isolated environment.
Is network sandboxing suitable for small businesses?
Yes, many cloud-based sandboxing solutions are affordable and scalable, making them suitable for small businesses looking to enhance their cybersecurity.
How does network sandboxing differ from antivirus software?
Antivirus relies on known virus signatures, while sandboxing analyzes the behavior of unknown or suspicious files in a safe environment to detect new threats.
Can malware evade network sandboxing?
Some advanced malware can detect sandbox environments and hide malicious actions, but ongoing improvements in sandbox technology reduce this risk.
Does network sandboxing slow down network performance?
While sandboxing requires resources, modern solutions are designed to minimize impact and often run in the cloud to avoid slowing down your network.





