What is Network Flood Attack
Introduction
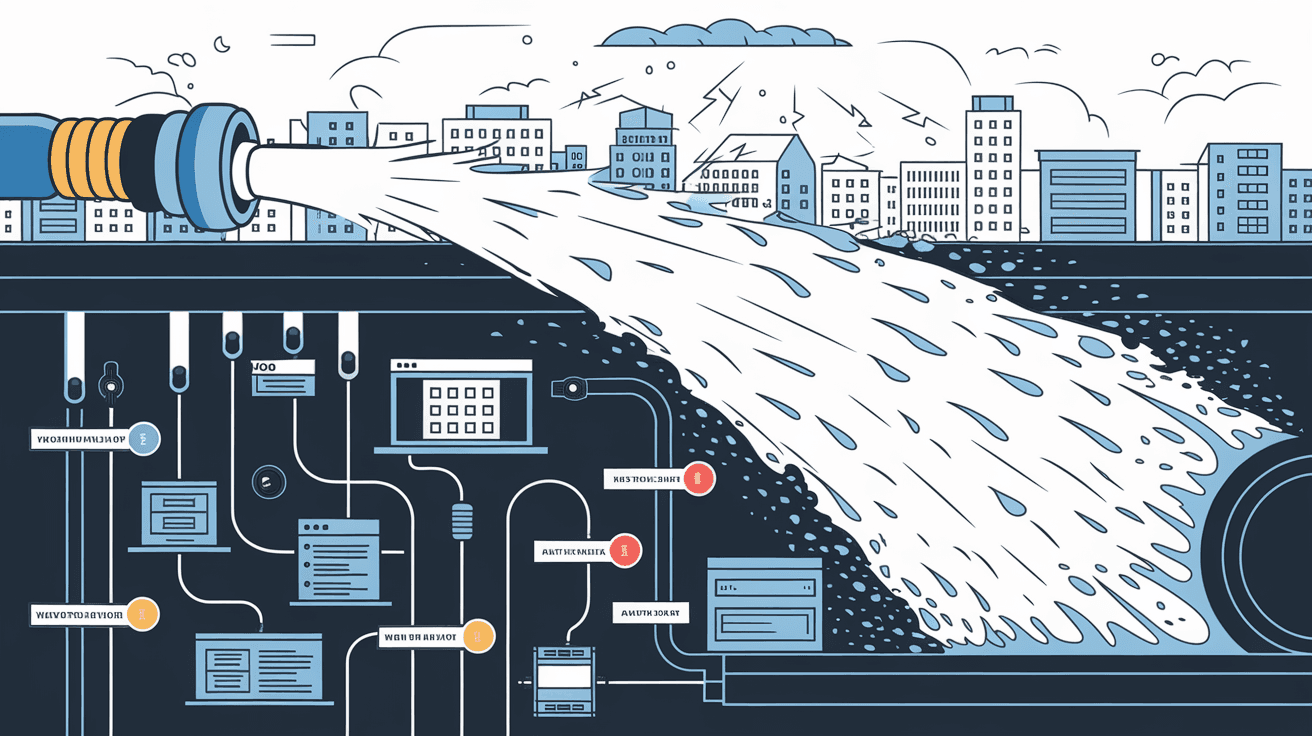
You might have heard about network flood attacks but wondered what they really are and how they affect your online experience. These attacks are a common way hackers disrupt internet services by overwhelming networks with excessive traffic. Understanding what a network flood attack is can help you protect your devices and data.
In this article, I’ll explain the basics of network flood attacks, how they work, and what you can do to defend against them. Whether you’re a casual internet user or managing a business network, knowing about these attacks is essential in today’s digital world.
What is a Network Flood Attack?
A network flood attack is a type of cyberattack where an attacker sends a massive amount of data packets to a network or server. The goal is to overwhelm the target’s resources, making it slow or completely unavailable to legitimate users. This is a form of Denial of Service (DoS) attack.
How It Works
- Attackers use automated tools to send huge volumes of traffic.
- The target network or server tries to process all incoming requests.
- Resources like bandwidth, CPU, and memory get exhausted.
- Legitimate users experience delays or can’t access the service at all.
Network flood attacks can target websites, online services, or entire networks. They are often used to disrupt business operations or as a distraction while other attacks happen.
Types of Network Flood Attacks
There are several types of network flood attacks, each using different methods to overwhelm a target. Here are the most common ones:
1. UDP Flood
- Sends a large number of User Datagram Protocol (UDP) packets.
- Targets random ports on the victim’s system.
- The system responds with error messages, consuming resources.
2. ICMP Flood (Ping Flood)
- Uses Internet Control Message Protocol (ICMP) echo requests (pings).
- The target tries to reply to each ping, using up bandwidth and processing power.
- Can cause network congestion and slow down services.
3. SYN Flood
- Exploits the TCP handshake process.
- Sends many SYN requests but never completes the handshake.
- The server waits for responses, tying up resources.
4. HTTP Flood
- Sends many HTTP requests to a web server.
- Mimics legitimate user behavior but at a high volume.
- Overloads the server’s ability to respond.
Each type targets different parts of the network stack but shares the goal of exhausting resources.
Why Do Attackers Use Network Flood Attacks?
Attackers have various reasons for launching network flood attacks:
- Disruption: To make websites or services unavailable.
- Extortion: Demanding ransom to stop the attack (ransom DoS).
- Cover-up: Distracting security teams while other attacks occur.
- Testing: Checking the strength of defenses.
- Political or Social Motives: Targeting organizations for ideological reasons.
Understanding the attacker’s motive can help in preparing the right defense.
How to Detect a Network Flood Attack
Detecting a network flood attack early is crucial to minimize damage. Here are signs that may indicate an ongoing attack:
- Sudden spike in network traffic.
- Slow or unresponsive websites and services.
- Increased error messages or timeouts.
- Unusual patterns in network logs.
- Alerts from intrusion detection systems.
Using monitoring tools and setting traffic thresholds can help spot attacks quickly.
Protecting Your Network from Flood Attacks
You can take several steps to protect your network from flood attacks. Here are practical measures:
1. Use Firewalls and Intrusion Prevention Systems (IPS)
- Configure firewalls to block suspicious traffic.
- IPS can detect and stop flood attacks in real-time.
2. Rate Limiting
- Limit the number of requests a user or IP can make in a given time.
- Helps prevent overwhelming your server with too many requests.
3. Traffic Filtering and Blacklisting
- Filter out traffic from known malicious IP addresses.
- Use blacklists to block repeat offenders.
4. Deploy Content Delivery Networks (CDNs)
- CDNs distribute traffic across multiple servers.
- Helps absorb large volumes of traffic during an attack.
5. Use Anti-DDoS Services
- Specialized services detect and mitigate flood attacks.
- They can scrub malicious traffic before it reaches your network.
6. Keep Systems Updated
- Regularly update software and firmware.
- Patches often fix vulnerabilities attackers exploit.
7. Network Segmentation
- Divide your network into smaller parts.
- Limits the spread and impact of an attack.
Real-World Examples of Network Flood Attacks
Network flood attacks have caused significant disruptions worldwide. Here are a few examples:
- GitHub Attack: In 2026, GitHub faced a massive HTTP flood attack that peaked at over 3 terabits per second. Their anti-DDoS measures helped mitigate the attack quickly.
- Financial Sector: Banks often face SYN flood attacks aimed at disrupting online banking services.
- Gaming Servers: Popular online games are frequent targets of UDP floods to cause lag and downtime.
These examples show how attackers target different industries and why robust defenses are necessary.
The Impact of Network Flood Attacks
The consequences of network flood attacks can be severe:
- Downtime: Services become unavailable, affecting users and revenue.
- Reputation Damage: Customers lose trust in unreliable services.
- Financial Loss: Costs from downtime, mitigation, and recovery.
- Data Breaches: Sometimes used as a distraction for stealing data.
- Legal Issues: Non-compliance with regulations if services fail.
Understanding these impacts highlights the importance of prevention and response planning.
What to Do If You Are Under a Network Flood Attack
If you suspect your network is under a flood attack, act quickly:
- Identify the attack: Use monitoring tools to confirm.
- Activate mitigation: Use firewalls, rate limiting, or anti-DDoS services.
- Contact your ISP: They can help filter traffic upstream.
- Inform stakeholders: Keep users and management updated.
- Analyze logs: Understand the attack to improve defenses.
- Review security policies: Adjust to prevent future attacks.
Quick response can reduce downtime and damage.
Conclusion
Now that you know what a network flood attack is, you can better understand the risks and how to protect yourself. These attacks aim to overwhelm networks with traffic, causing slowdowns or outages. They come in various forms like UDP floods, SYN floods, and HTTP floods.
By using firewalls, rate limiting, anti-DDoS services, and staying vigilant, you can defend your network against these threats. Remember, early detection and quick response are key to minimizing the impact. Staying informed and prepared helps keep your online services safe and reliable.
FAQs
What is the main goal of a network flood attack?
The main goal is to overwhelm a network or server with excessive traffic, making it slow or unavailable to legitimate users.
How does a SYN flood attack work?
It sends many TCP connection requests but never completes them, causing the server to wait and use up resources.
Can network flood attacks be prevented completely?
While you can’t prevent all attacks, using firewalls, rate limiting, and anti-DDoS services greatly reduces the risk and impact.
What tools help detect network flood attacks?
Network monitoring software, intrusion detection systems, and traffic analysis tools help spot unusual traffic spikes.
Are network flood attacks illegal?
Yes, launching network flood attacks is illegal in most countries as it disrupts services and causes harm.





