What is Network Address Translation Security
Introduction
When you connect to the internet, your device uses an IP address to communicate. But did you know that Network Address Translation (NAT) plays a big role in keeping your network safe? NAT security is a key part of how networks protect themselves from outside threats.
In this article, I’ll explain what NAT security is, how it works, and why it’s important for your home or business network. You’ll also learn how NAT helps hide your devices and what limitations it has when it comes to security.
What is Network Address Translation (NAT)?
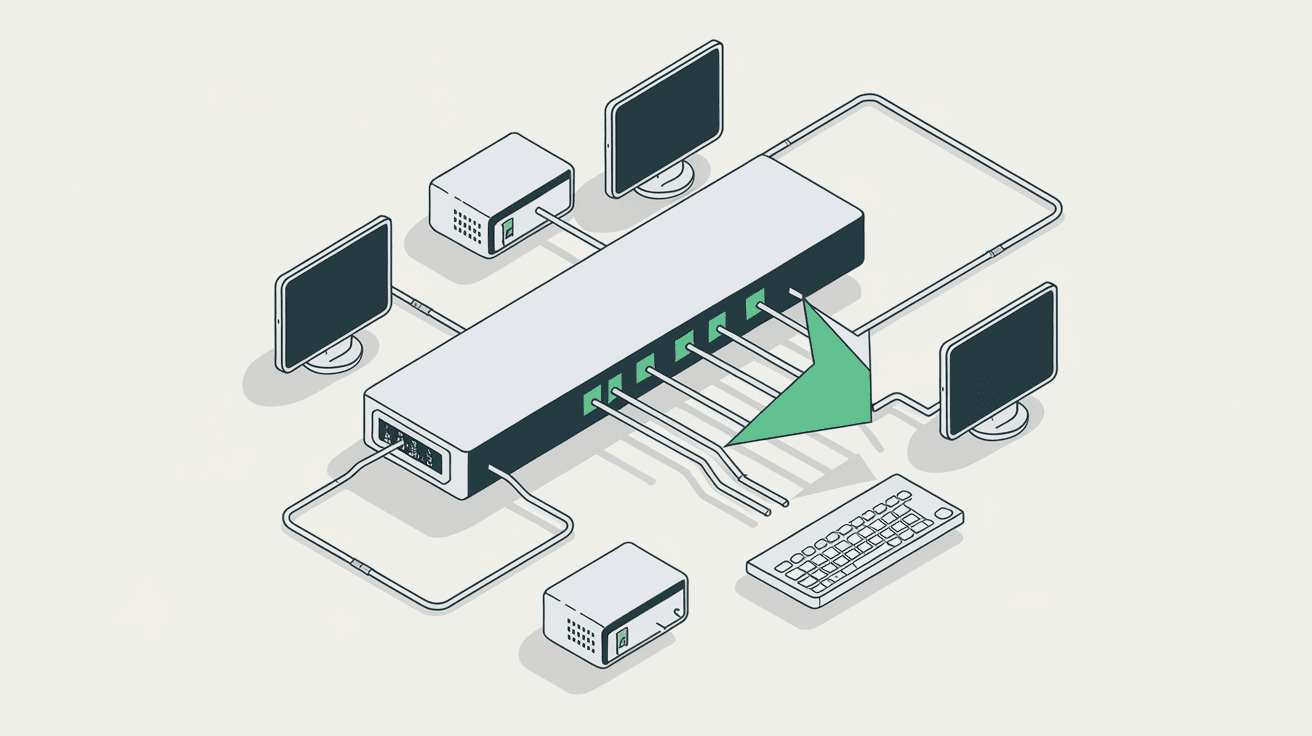
Network Address Translation, or NAT, is a method used by routers to modify IP addresses in data packets as they pass through a network. It allows multiple devices on a private network to share a single public IP address when accessing the internet.
Here’s how NAT works in simple terms:
- Your device has a private IP address that only works inside your home or office network.
- When your device sends data to the internet, the router changes the private IP to the router’s public IP.
- When the response comes back, the router translates the public IP back to your device’s private IP.
This process helps conserve public IP addresses and allows many devices to connect through one address.
How NAT Enhances Network Security
NAT adds a layer of security by hiding internal IP addresses from the outside world. Here’s why that matters:
- IP Address Masking: External devices only see the router’s public IP, not the private IPs of your devices.
- Inbound Traffic Control: NAT blocks unsolicited inbound traffic because the router only forwards responses to requests initiated inside the network.
- Basic Firewall Functionality: Many routers combine NAT with firewall rules to filter traffic.
This means hackers can’t directly target your devices because they don’t know their private IP addresses. NAT acts like a shield, making it harder for attackers to find and exploit devices on your network.
Types of NAT and Their Security Implications
There are different types of NAT, each with varying effects on security:
- Static NAT: Maps one private IP to one public IP. It’s less secure because the mapping is fixed and predictable.
- Dynamic NAT: Maps private IPs to a pool of public IPs dynamically. It offers better security by changing mappings.
- Port Address Translation (PAT): Also called NAT overload, it maps multiple private IPs to a single public IP using different ports. This is the most common and secure form for home networks.
PAT is especially useful because it allows many devices to share one IP while keeping their connections separate. This makes it difficult for outsiders to guess which device is communicating.
NAT Security Limitations You Should Know
While NAT improves security, it’s not a complete solution. Here are some limitations:
- Not a True Firewall: NAT doesn’t inspect the content of packets deeply. It only translates addresses.
- Vulnerable to Certain Attacks: Techniques like NAT traversal can bypass NAT restrictions, allowing some attacks.
- No Protection Against Internal Threats: NAT only hides devices from outside networks, not from threats inside your network.
- Complicates Some Applications: Applications like VoIP or online gaming may require special configurations (port forwarding) that can expose devices.
Because of these limits, NAT should be combined with other security measures like firewalls, antivirus software, and intrusion detection systems.
How NAT Works with Firewalls for Better Security
Most modern routers combine NAT with firewall features to improve security. Here’s how they work together:
- NAT Hides Devices: Keeps internal IPs private.
- Firewall Filters Traffic: Blocks unauthorized inbound and outbound connections based on rules.
- Stateful Inspection: Tracks active connections to allow only legitimate traffic.
This combination creates a strong barrier against many common cyber threats. For example, unsolicited connection attempts from hackers are blocked because the firewall doesn’t recognize them as part of an active session.
NAT Security in Enterprise Networks
In larger networks, NAT security is more complex but still essential. Enterprises use NAT to:
- Conserve IP Addresses: Private IP ranges are reused internally.
- Segment Networks: Different departments or zones use separate private IPs.
- Control Access: NAT combined with firewalls and VPNs restricts access between segments.
Enterprises often use advanced NAT types like NAT64 or NAT44 to support IPv6 transition or complex routing. They also deploy intrusion prevention systems (IPS) alongside NAT to detect and block threats.
Best Practices for Enhancing NAT Security
To get the most security from NAT, consider these best practices:
- Use PAT Instead of Static NAT: Dynamic mappings reduce predictability.
- Enable Router Firewalls: Don’t rely on NAT alone; use firewall features.
- Configure Port Forwarding Carefully: Only open necessary ports and monitor them.
- Keep Firmware Updated: Router updates often fix security vulnerabilities.
- Combine NAT with VPNs: Encrypt traffic for secure remote access.
- Monitor Network Traffic: Use tools to detect unusual activity.
By following these steps, you can strengthen your network’s defenses and reduce risks.
NAT and IPv6: What You Need to Know
IPv6, the new internet protocol, changes how NAT is used. Unlike IPv4, IPv6 has a huge address space, so NAT is less necessary for address conservation.
However, NAT still plays a role in IPv6 security:
- NAT66: A form of NAT for IPv6, though less common.
- Firewalling Still Needed: IPv6 devices have public addresses, so firewalls are critical.
- Privacy Extensions: IPv6 uses temporary addresses to protect user privacy.
In the future, networks may rely more on firewalls and less on NAT for security as IPv6 adoption grows.
Conclusion
Network Address Translation security is a fundamental part of protecting your devices online. By hiding private IP addresses and controlling inbound traffic, NAT makes it harder for attackers to reach your network. However, NAT alone isn’t enough—it works best when combined with firewalls, updated software, and careful network management.
Whether you’re managing a home network or a large enterprise, understanding NAT security helps you build stronger defenses. Keep your router’s firmware updated, use dynamic NAT types like PAT, and monitor your network regularly. These steps will help you stay safe in an increasingly connected world.
FAQs
What is the main security benefit of NAT?
NAT hides your internal IP addresses from the internet, making it harder for attackers to directly access your devices. It also blocks unsolicited inbound traffic by only allowing responses to requests initiated inside your network.
Can NAT replace a firewall?
No, NAT is not a replacement for a firewall. While NAT hides IP addresses, it doesn’t inspect or filter traffic deeply. Firewalls provide detailed traffic filtering and protection against many types of attacks.
How does NAT affect online gaming or VoIP?
NAT can block some online gaming or VoIP services because they require incoming connections. You may need to set up port forwarding or use NAT traversal techniques to allow these applications to work properly.
Is NAT still necessary with IPv6?
IPv6 has a large address space, reducing the need for NAT to conserve addresses. However, NAT or similar techniques may still be used for security or network management, but firewalls remain essential.
What is Port Address Translation (PAT)?
PAT is a type of NAT that allows multiple devices to share one public IP address by using different port numbers. It’s common in home networks and provides better security by making device mappings dynamic and less predictable.





