What is MITRE ATT&CK Framework
Introduction
If you’re curious about how organizations defend themselves against cyber threats, you’ve probably heard of the MITRE ATT&CK Framework. It’s a powerful tool that helps security teams understand how attackers operate and how to stop them. In this article, I’ll explain what the MITRE ATT&CK Framework is and why it’s so important for cybersecurity.
We’ll explore how this framework breaks down attacker behavior into clear tactics and techniques. You’ll also learn how it’s used in real-world security operations to detect, respond to, and prevent cyberattacks. By the end, you’ll see why the MITRE ATT&CK Framework is a must-know for anyone interested in cybersecurity.
What is the MITRE ATT&CK Framework?
The MITRE ATT&CK Framework is a knowledge base of cyber adversary behavior. It stands for Adversarial Tactics, Techniques, and Common Knowledge. Developed by MITRE, a nonprofit organization, it organizes and categorizes the methods attackers use during cyber intrusions.
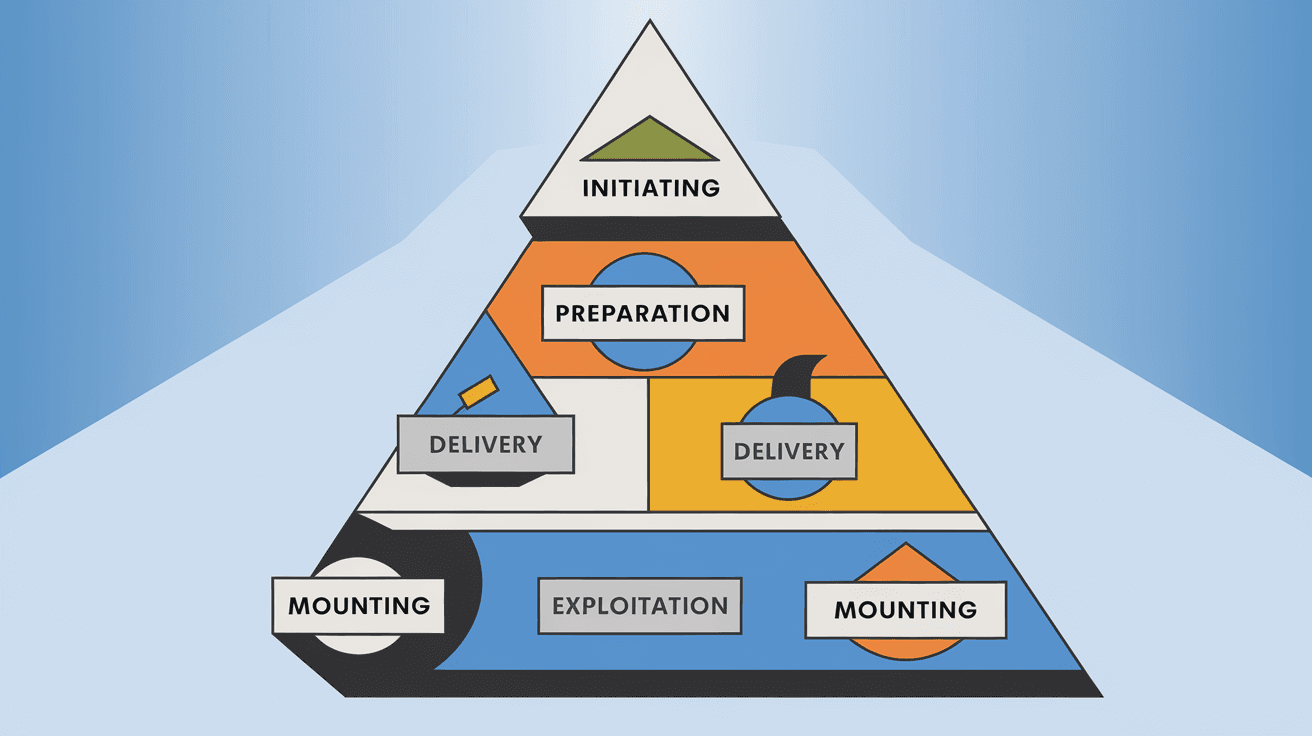
Unlike traditional security tools that focus on specific threats or malware, ATT&CK focuses on the behavior of attackers. It maps out the steps attackers take from initial access to achieving their goals. This helps defenders understand the full attack lifecycle.
Key Features of MITRE ATT&CK
- Tactics: The high-level goals attackers want to achieve, like gaining access or stealing data.
- Techniques: The specific methods attackers use to accomplish those goals.
- Sub-techniques: More detailed variations of techniques.
- Procedures: Real-world examples of how attackers use these techniques.
This framework is constantly updated based on new threat intelligence, making it a living resource for cybersecurity teams.
Why is the MITRE ATT&CK Framework Important?
The MITRE ATT&CK Framework is important because it provides a common language and structure for understanding cyber threats. Here’s why it matters:
- Improves Threat Detection: By knowing attacker behaviors, security teams can spot suspicious activity earlier.
- Enhances Incident Response: It helps responders understand what an attacker is doing and how to stop them.
- Supports Threat Hunting: Analysts can proactively search for signs of attacker techniques in their networks.
- Guides Security Controls: Organizations can prioritize defenses based on the most relevant tactics and techniques.
- Facilitates Communication: It creates a shared vocabulary between teams, vendors, and researchers.
Many cybersecurity tools and platforms now integrate ATT&CK to improve their detection and response capabilities.
How Does the MITRE ATT&CK Framework Work?
The framework is organized into matrices that cover different environments, such as enterprise networks, mobile devices, and cloud systems. The most widely used is the Enterprise ATT&CK Matrix.
The Enterprise ATT&CK Matrix
This matrix is divided into columns representing tactics—the goals attackers aim to achieve during an attack. Each column contains rows of techniques that describe how attackers accomplish those goals.
For example, some common tactics include:
- Initial Access: How attackers first enter a network (e.g., phishing, exploiting vulnerabilities).
- Execution: How attackers run malicious code (e.g., PowerShell scripts).
- Persistence: How attackers maintain access over time (e.g., creating backdoors).
- Privilege Escalation: How attackers gain higher permissions.
- Defense Evasion: How attackers avoid detection.
- Credential Access: How attackers steal login information.
- Exfiltration: How attackers steal data.
Each technique is linked to real-world examples and detection recommendations.
Using the Framework in Practice
Security teams use ATT&CK to:
- Map detected activities to known techniques.
- Identify gaps in their defenses.
- Develop detection rules based on attacker behaviors.
- Train staff on common attack methods.
For example, if a team detects suspicious PowerShell activity, they can check the ATT&CK framework to understand which technique it matches and what to do next.
Real-World Applications of MITRE ATT&CK
Many organizations and cybersecurity vendors use the MITRE ATT&CK Framework to strengthen their defenses. Here are some common applications:
Threat Intelligence Analysis
Threat intelligence teams analyze attacker campaigns and map them to ATT&CK techniques. This helps them understand attacker goals and predict future moves.
Security Operations Centers (SOCs)
SOCs use ATT&CK to classify alerts and prioritize responses. It helps analysts quickly identify the severity and nature of threats.
Red Teaming and Penetration Testing
Red teams simulate attacks using ATT&CK techniques to test an organization’s defenses. This reveals weaknesses and improves security posture.
Security Product Development
Vendors build detection and prevention features based on ATT&CK techniques. This ensures their products address real attacker behaviors.
Compliance and Risk Management
Organizations use ATT&CK to assess their security controls against known attacker methods, helping meet regulatory requirements.
Benefits of Using MITRE ATT&CK Framework
Using the MITRE ATT&CK Framework offers several benefits:
- Comprehensive Coverage: It covers a wide range of attacker behaviors across different platforms.
- Up-to-Date Intelligence: Regular updates keep it relevant against evolving threats.
- Improved Detection: Helps identify sophisticated attacks that traditional tools might miss.
- Better Incident Response: Provides clear guidance on attacker techniques and mitigation.
- Collaboration: Enables sharing of threat information using a common language.
These benefits make ATT&CK a valuable resource for organizations of all sizes.
Challenges and Limitations
While powerful, the MITRE ATT&CK Framework has some challenges:
- Complexity: The framework is detailed and can be overwhelming for beginners.
- Resource Intensive: Implementing ATT&CK-based detection requires skilled analysts and tools.
- Not a Complete Solution: It focuses on attacker behavior but doesn’t replace other security measures.
- False Positives: Some techniques may trigger alerts that are not actual attacks.
Despite these challenges, many organizations find the benefits outweigh the difficulties.
How to Get Started with MITRE ATT&CK
If you want to start using the MITRE ATT&CK Framework, here are some steps:
- Familiarize Yourself: Explore the ATT&CK website and matrices to understand tactics and techniques.
- Map Your Environment: Identify which parts of your network and systems are most at risk.
- Integrate with Tools: Use security tools that support ATT&CK mapping and detection.
- Train Your Team: Educate analysts and responders on how to use ATT&CK in daily operations.
- Conduct Threat Hunting: Use ATT&CK techniques to proactively search for threats.
- Review and Update: Regularly update your knowledge and defenses based on new ATT&CK releases.
Starting small and gradually expanding your use of ATT&CK can make adoption easier.
Conclusion
The MITRE ATT&CK Framework is a game-changer in cybersecurity. It helps you understand how attackers operate by breaking down their tactics and techniques. This knowledge lets you detect threats faster, respond smarter, and build stronger defenses.
Whether you’re a security analyst, manager, or just curious about cyber defense, learning about ATT&CK is a smart move. It provides a clear, practical way to stay ahead of cyber threats in today’s complex digital world.
FAQs
What does MITRE ATT&CK stand for?
MITRE ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge. It’s a framework that categorizes attacker behaviors to help defenders understand and respond to cyber threats.
How is the ATT&CK Framework different from traditional threat databases?
Unlike traditional databases that focus on malware signatures, ATT&CK focuses on attacker behavior and techniques, providing a more comprehensive view of how attacks unfold.
Can small businesses use the MITRE ATT&CK Framework?
Yes, small businesses can benefit by using ATT&CK to understand common attack methods and improve their security posture, even if they don’t have large security teams.
How often is the MITRE ATT&CK Framework updated?
MITRE regularly updates the framework with new tactics, techniques, and procedures based on the latest threat intelligence and real-world attacks.
Are there tools that integrate with MITRE ATT&CK?
Many cybersecurity tools, including SIEMs, endpoint detection, and threat intelligence platforms, integrate ATT&CK to enhance detection and response capabilities.





