What is Message Authentication Code
Introduction
When you send a message online, how do you know it hasn’t been changed or tampered with? That’s where a Message Authentication Code, or MAC, comes in. It helps you verify that the message you received is exactly what the sender intended. In this article, I’ll explain what a MAC is, how it works, and why it’s important for keeping your data safe.
You might have heard about encryption, but MACs play a different role. They don’t hide the message; instead, they ensure the message’s integrity and authenticity. Let’s dive into how this works and why you should care about MACs in your digital life.
What is a Message Authentication Code?
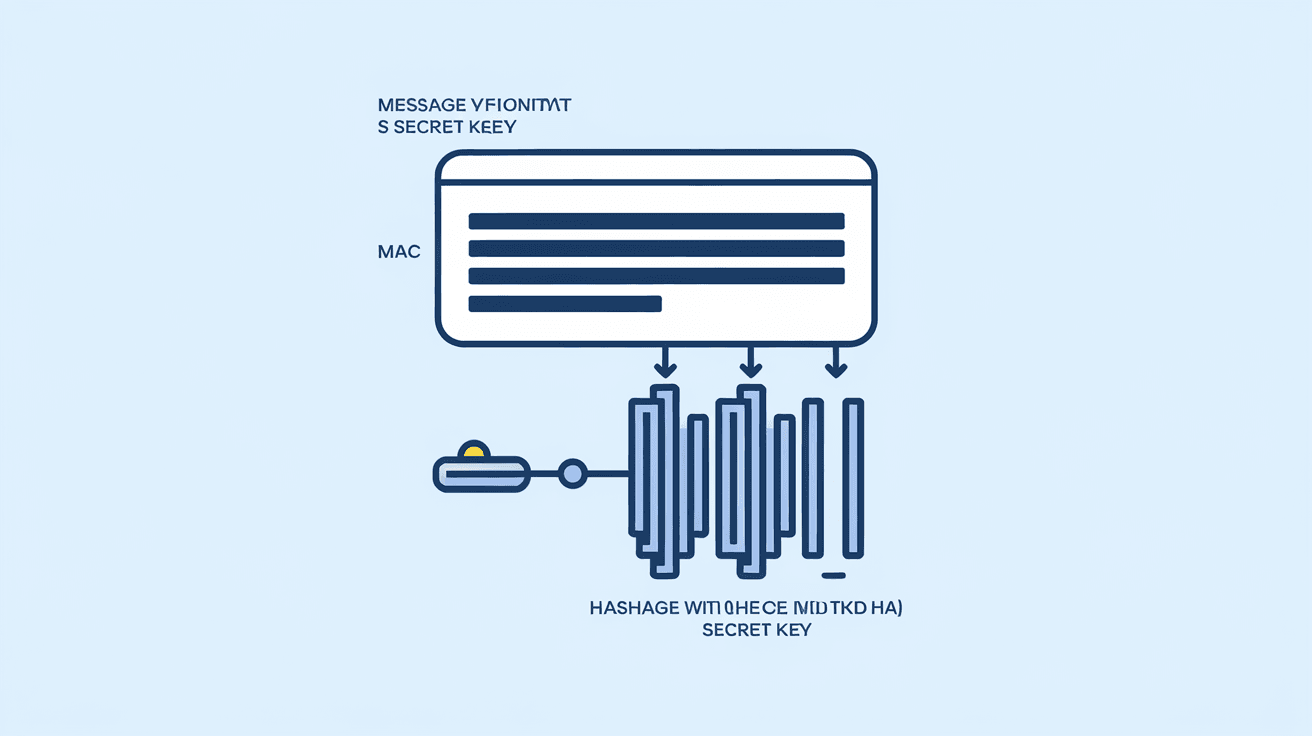
A Message Authentication Code (MAC) is a short piece of information used to confirm that a message is authentic and hasn’t been altered. Think of it as a digital signature created using a secret key shared between the sender and receiver.
Here’s how it works in simple terms:
- The sender uses a secret key and the message to generate a MAC.
- The MAC is sent along with the message.
- The receiver uses the same secret key and the received message to generate their own MAC.
- If both MACs match, the message is authentic and unchanged.
MACs are widely used in secure communication protocols, like HTTPS and VPNs, to protect data from tampering.
How Does a Message Authentication Code Work?
MACs rely on cryptographic algorithms and secret keys. The process involves two main steps: generation and verification.
Generation
- The sender combines the message with a secret key.
- A cryptographic function processes this combination.
- The output is the MAC, a fixed-size string unique to the message and key.
Verification
- The receiver takes the received message and the shared secret key.
- They run the same cryptographic function to generate a new MAC.
- If the new MAC matches the one sent, the message is verified.
This process ensures two things:
- Integrity: The message hasn’t been changed.
- Authenticity: The message comes from someone who knows the secret key.
Common Algorithms Used in MACs
- HMAC (Hash-based MAC): Uses hash functions like SHA-256.
- CMAC (Cipher-based MAC): Uses block ciphers like AES.
- UMAC and VMAC: Use universal hashing for faster performance.
Each algorithm has its strengths depending on the application and security needs.
Why is a Message Authentication Code Important?
You might wonder why we need MACs when encryption already protects data. The answer lies in the difference between confidentiality and integrity.
- Encryption hides the content of a message.
- MACs ensure the message hasn’t been altered and is from a trusted source.
Without MACs, attackers could intercept messages, change them, and send fake messages without detection.
Real-World Uses of MACs
- Online banking: Ensures transaction details aren’t tampered with.
- Software updates: Verifies that updates come from the official source.
- Secure messaging apps: Confirms messages are genuine and unaltered.
- Payment systems: Protects against fraud by verifying transaction authenticity.
MACs are a critical part of many security protocols, helping protect your data every day.
How is a MAC Different from a Digital Signature?
Both MACs and digital signatures verify message authenticity, but they work differently.
| Feature | Message Authentication Code (MAC) | Digital Signature |
| Key Type | Symmetric (same key for sender and receiver) | Asymmetric (public/private key pair) |
| Verification | Only parties with the secret key | Anyone with the public key |
| Use Case | Private communication between trusted parties | Public verification, non-repudiation |
| Security Focus | Integrity and authenticity | Integrity, authenticity, and non-repudiation |
MACs are faster and simpler but require both parties to share a secret key. Digital signatures provide stronger guarantees but are more complex.
How to Implement a Message Authentication Code
If you want to implement a MAC in your application, here are the basic steps:
- Choose a MAC algorithm: HMAC with SHA-256 is a popular and secure choice.
- Generate a secret key: Use a strong, random key shared securely between sender and receiver.
- Create the MAC: Use a cryptographic library to combine the message and key.
- Send the message and MAC: Transmit both to the receiver.
- Verify the MAC: The receiver uses the same key and algorithm to check the MAC.
Tips for Secure MAC Implementation
- Always use a strong, random key.
- Never reuse keys across different systems.
- Use well-tested cryptographic libraries.
- Protect the secret key from exposure.
Following these steps helps ensure your MAC implementation is secure and reliable.
Common Attacks Against MACs and How to Prevent Them
Even though MACs are designed to protect messages, attackers try to break them. Here are some common attacks and how to defend against them:
- Replay attacks: An attacker resends a valid message and MAC. Use timestamps or sequence numbers to detect duplicates.
- Key leakage: If the secret key is exposed, attackers can forge MACs. Protect keys with strong access controls.
- Collision attacks: Some MAC algorithms may be vulnerable if the underlying hash function is weak. Use strong algorithms like HMAC-SHA-256.
- Length extension attacks: Certain hash functions allow attackers to append data without changing the MAC. Use HMAC to prevent this.
By understanding these threats, you can design systems that keep your MACs secure.
Message Authentication Code in Modern Security Protocols
MACs are embedded in many security protocols you use every day:
- TLS/SSL: Uses MACs to verify data integrity during secure web browsing.
- IPsec: Protects internet protocol communications with MACs.
- SSH: Secures remote logins by verifying message authenticity.
- JWT (JSON Web Tokens): Often use MACs to ensure token integrity.
These protocols rely on MACs to maintain trust and security in digital communications.
Conclusion
Now you know that a Message Authentication Code is a vital tool for verifying that messages are authentic and unchanged. Unlike encryption, which hides data, MACs focus on integrity and authenticity. They use secret keys and cryptographic algorithms to create a unique code that both sender and receiver can check.
Whether you’re sending a simple message or securing complex systems, MACs help protect against tampering and fraud. Understanding how MACs work and their role in security protocols can help you appreciate the hidden layers of protection in your digital life.
FAQs
What is the difference between a MAC and a hash function?
A MAC uses a secret key combined with a hash function to ensure message authenticity, while a hash function alone only provides a fixed output for data without any secret key, so it can’t verify the sender.
Can MACs be used without encryption?
Yes, MACs can be used on plain messages to verify integrity and authenticity without encrypting the content. However, combining MACs with encryption provides both confidentiality and integrity.
How does HMAC improve security over simple MACs?
HMAC uses a hash function with a secret key in a specific way that prevents attacks like length extension, making it more secure than simple MACs based on raw hash functions.
Are MAC keys shared publicly?
No, MAC keys are secret and must be shared securely only between trusted parties. If the key is exposed, attackers can forge MACs and compromise security.
Can MACs prevent all types of message tampering?
MACs protect against tampering and forgery but do not prevent message interception or eavesdropping. For full security, MACs are often combined with encryption and other security measures.





