What is Least Privilege Networking
Introduction
When it comes to network security, controlling access is key. You want to make sure that users and systems only have the permissions they truly need. This is where least privilege networking comes in. It’s a security approach that limits network access to the minimum necessary, reducing risks and improving control.
In this article, I’ll explain what least privilege networking means, why it matters, and how you can apply it to protect your network. You’ll also see practical examples and tips to get started with this powerful security strategy.
What is Least Privilege Networking?
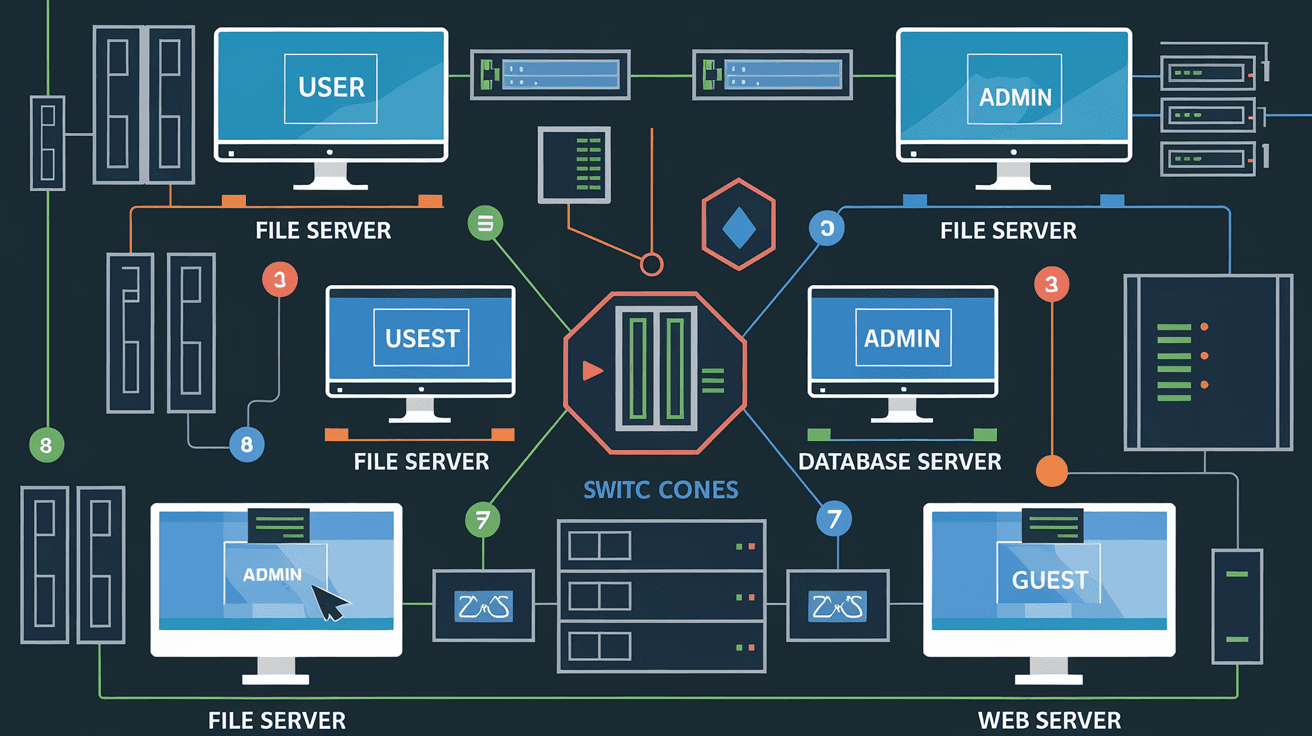
Least privilege networking is a security principle that restricts network access rights for users, devices, and applications to only what is essential for their tasks. Instead of giving broad or full access, it enforces strict limits on who can connect to what, and how.
This approach helps prevent unauthorized access and limits the damage if a breach happens. For example, if a user only needs to access a specific database, least privilege networking ensures they cannot reach other parts of the network.
Key Features of Least Privilege Networking
- Minimal Access: Users and devices get only the permissions they need.
- Segmentation: Networks are divided into smaller zones to isolate resources.
- Strict Controls: Access is granted based on roles, time, or context.
- Continuous Monitoring: Access patterns are tracked to detect anomalies.
By applying these features, organizations reduce their attack surface and improve overall security posture.
Why is Least Privilege Networking Important?
Network environments today are complex and dynamic. With cloud services, remote work, and IoT devices, the risk of unauthorized access grows. Least privilege networking helps you manage these risks effectively.
Here are some reasons why it’s essential:
- Limits Damage from Breaches: If an attacker gains access, they can only reach limited resources.
- Reduces Insider Threats: Even trusted users can’t access sensitive areas unnecessarily.
- Improves Compliance: Many regulations require strict access controls.
- Simplifies Auditing: Clear access rules make it easier to track who accessed what.
By enforcing least privilege, you create a safer network that’s harder for attackers to exploit.
How Does Least Privilege Networking Work?
Least privilege networking works by combining several security techniques and technologies. Here’s how it typically operates:
Network Segmentation
The network is divided into smaller segments or zones. Each segment contains resources with similar security needs. Access between segments is tightly controlled.
- Example: Separate your finance systems from general employee devices.
- Benefit: Limits lateral movement of attackers inside the network.
Role-Based Access Control (RBAC)
Users and devices are assigned roles with specific permissions. Access is granted based on these roles, not on broad privileges.
- Example: A marketing employee can access marketing servers but not HR databases.
- Benefit: Ensures users only see what they need.
Micro-Segmentation
This is a finer level of segmentation, often used in cloud or virtualized environments. It controls traffic between individual workloads or applications.
- Example: Only allow the web server to communicate with the database server.
- Benefit: Reduces risk of spreading malware or attacks.
Zero Trust Principles
Least privilege networking aligns with zero trust, which assumes no user or device is trusted by default. Every access request is verified.
- Example: Require multi-factor authentication and device checks before granting access.
- Benefit: Strengthens security by verifying every connection.
Benefits of Implementing Least Privilege Networking
Adopting least privilege networking offers many advantages beyond just security. Here are some key benefits:
- Enhanced Security: Limits exposure to attacks and insider threats.
- Better Control: Clear policies make it easier to manage who accesses what.
- Improved Performance: Segmentation can reduce unnecessary traffic.
- Regulatory Compliance: Helps meet standards like HIPAA, PCI-DSS, and GDPR.
- Faster Incident Response: Easier to isolate and contain breaches.
These benefits make least privilege networking a smart choice for organizations of all sizes.
Challenges in Applying Least Privilege Networking
While the benefits are clear, implementing least privilege networking can be challenging. Here are some common obstacles:
- Complexity: Designing and managing segmented networks requires planning.
- Legacy Systems: Older devices may not support fine-grained access controls.
- User Resistance: Users may find restrictions inconvenient.
- Continuous Maintenance: Access needs change, requiring ongoing updates.
- Visibility: Without proper tools, it’s hard to monitor all access points.
Understanding these challenges helps you prepare and address them effectively.
Best Practices for Implementing Least Privilege Networking
To successfully apply least privilege networking, consider these best practices:
1. Map Your Network and Resources
Know what devices, users, and applications exist. Understand their access needs.
- Create an inventory of assets.
- Identify sensitive data and critical systems.
2. Define Roles and Access Policies
Assign roles based on job functions and limit access accordingly.
- Use the principle of least privilege for each role.
- Avoid giving blanket permissions.
3. Use Network Segmentation and Micro-Segmentation
Divide your network into zones and control traffic between them.
- Implement firewalls or software-defined networking (SDN).
- Use VLANs or cloud security groups.
4. Enforce Strong Authentication and Authorization
Require multi-factor authentication and verify devices.
- Use identity and access management (IAM) tools.
- Regularly review access rights.
5. Monitor and Audit Access Continuously
Track who accesses what and when.
- Use security information and event management (SIEM) systems.
- Look for unusual patterns or violations.
6. Automate Where Possible
Automation helps keep policies consistent and up to date.
- Use tools for policy enforcement and access reviews.
- Automate alerts for suspicious activity.
Examples of Least Privilege Networking in Action
Here are some real-world examples to illustrate how least privilege networking works:
- Cloud Environments: AWS and Azure allow micro-segmentation with security groups and network ACLs. You can restrict traffic between virtual machines based on roles.
- Corporate Networks: A company segments its network so that finance staff can only access financial servers, while IT has separate access. VPN access is limited by role.
- Healthcare: Hospitals restrict access to patient records systems only to authorized medical staff, using role-based controls and network segmentation.
- Remote Work: Organizations use zero trust network access (ZTNA) solutions to verify remote users before granting access to internal applications.
These examples show how least privilege networking adapts to different environments.
Tools and Technologies Supporting Least Privilege Networking
Several tools can help you implement and maintain least privilege networking:
| Tool Type | Examples | Purpose |
| Network Firewalls | Palo Alto, Cisco ASA | Control traffic between segments |
| Identity and Access Management (IAM) | Okta, Microsoft Azure AD | Manage user roles and authentication |
| Software-Defined Networking (SDN) | VMware NSX, Cisco ACI | Enable micro-segmentation and automation |
| Zero Trust Network Access (ZTNA) | Zscaler, Cloudflare Access | Verify and control remote access |
| Security Information and Event Management (SIEM) | Splunk, IBM QRadar | Monitor and analyze access logs |
Using these tools together creates a strong least privilege networking environment.
Conclusion
Least privilege networking is a powerful way to secure your network by limiting access to only what is necessary. It reduces risks from attackers and insiders, helps meet compliance requirements, and improves overall control. While it requires planning and ongoing effort, the benefits far outweigh the challenges.
By understanding the principles, applying best practices, and using the right tools, you can protect your network effectively. Start by mapping your assets and defining clear roles, then segment your network and enforce strict access controls. With least privilege networking, you take a big step toward a safer, more resilient network.
FAQs
What is the main goal of least privilege networking?
The main goal is to limit network access to only what users or devices need to perform their tasks. This reduces security risks by preventing unnecessary or unauthorized access.
How does network segmentation support least privilege networking?
Network segmentation divides the network into smaller zones, isolating resources. This limits access and prevents attackers from moving freely within the network.
Can least privilege networking be applied to cloud environments?
Yes, cloud platforms support least privilege networking through micro-segmentation, security groups, and role-based access controls to restrict traffic and user permissions.
What challenges might I face when implementing least privilege networking?
Common challenges include managing complexity, dealing with legacy systems, user resistance, and the need for continuous monitoring and updates.
How does least privilege networking relate to zero trust security?
Least privilege networking is a key part of zero trust, which assumes no user or device is trusted by default and requires verification for every access request.





