What is Lateral Movement Attack
Introduction
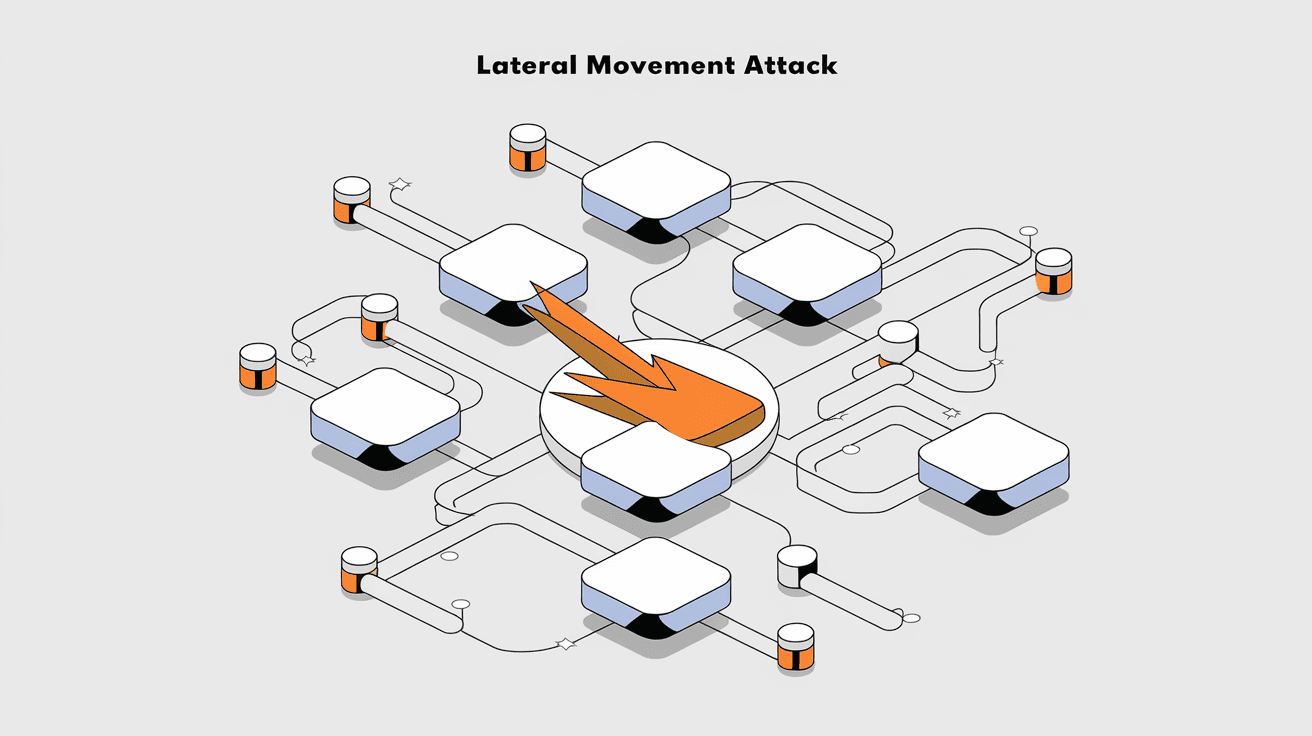
You might have heard about cyberattacks that don’t just stop at one system but spread quietly across networks. That’s what a lateral movement attack is all about. It’s a sneaky way hackers move inside a network after breaking in, aiming to access valuable data or control critical systems.
In this article, I’ll explain what a lateral movement attack is, how attackers carry it out, and what you can do to spot and stop it. Understanding this will help you protect your network better and keep your data safe.
What Is a Lateral Movement Attack?
A lateral movement attack happens when a hacker gains access to one part of a network and then moves sideways to other connected systems. Instead of attacking everything at once, they quietly explore and expand their control.
- The attacker starts with a single compromised device or account.
- They use that foothold to explore the network.
- They move from one system to another, often without being noticed.
- Their goal is to find sensitive data or critical systems to exploit.
This method is common in advanced cyberattacks because it helps hackers avoid detection. They don’t trigger alarms by attacking many systems at once. Instead, they move slowly and carefully.
How Does Lateral Movement Work?
Lateral movement involves several steps that hackers follow to spread inside a network. Here’s a simplified breakdown:
- Initial Access: The attacker gains entry through phishing, malware, or exploiting vulnerabilities.
- Reconnaissance: They gather information about the network, such as user accounts, system configurations, and connected devices.
- Credential Theft: Hackers steal login details or tokens to access other systems.
- Privilege Escalation: They increase their access rights to control more parts of the network.
- Lateral Movement: Using stolen credentials and tools, they move to other devices.
- Objective Execution: Finally, they reach their target, like stealing data or disrupting operations.
Each step is carefully planned to avoid detection and maximize control.
Common Techniques Used in Lateral Movement Attacks
Hackers use various tools and methods to move laterally. Some of the most common include:
- Pass-the-Hash: Using stolen password hashes to log into other systems without cracking passwords.
- Pass-the-Ticket: Using stolen Kerberos tickets to access network resources.
- Remote Desktop Protocol (RDP): Exploiting remote access tools to control other machines.
- Windows Management Instrumentation (WMI): Running commands on remote systems.
- PowerShell Scripts: Automating tasks and moving through the network silently.
- Exploitation of Trust Relationships: Taking advantage of trusted connections between systems.
These techniques allow attackers to blend in with normal network activity, making detection harder.
Why Are Lateral Movement Attacks Dangerous?
Lateral movement attacks are especially dangerous because they:
- Bypass Perimeter Defenses: Once inside, attackers avoid firewalls and antivirus protections.
- Access Sensitive Data: They can reach databases, financial records, or intellectual property.
- Cause Widespread Damage: The attacker can control many systems, leading to data breaches or ransomware spread.
- Remain Undetected: Slow movement and use of legitimate credentials make spotting them difficult.
Organizations often discover these attacks only after significant damage has been done.
How to Detect Lateral Movement Attacks
Detecting lateral movement requires careful monitoring and analysis of network activity. Here are some signs and methods:
- Unusual Login Patterns: Multiple logins from the same user to different systems in a short time.
- Access Outside Normal Hours: Users accessing systems at odd times.
- Use of Administrative Tools: Unexpected use of PowerShell, WMI, or RDP.
- Network Traffic Anomalies: Sudden spikes or unusual data flows between devices.
- Alerts from Endpoint Detection and Response (EDR) Tools: These tools can spot suspicious behavior.
Regularly reviewing logs and using automated detection systems helps catch lateral movement early.
Preventing Lateral Movement Attacks
Stopping lateral movement involves a mix of technology and good security practices. Here’s what you can do:
- Implement Network Segmentation: Divide your network into smaller zones to limit attacker movement.
- Use Strong Authentication: Multi-factor authentication (MFA) reduces the risk of stolen credentials being used.
- Limit Privileges: Give users only the access they need to do their jobs.
- Patch Systems Regularly: Fix vulnerabilities that attackers might exploit.
- Monitor and Audit: Continuously watch network activity and review access logs.
- Educate Employees: Train staff to recognize phishing and other attack methods.
Combining these steps creates multiple barriers against lateral movement.
Real-World Examples of Lateral Movement Attacks
Several high-profile cyberattacks have involved lateral movement. Here are two examples:
- SolarWinds Hack: Attackers gained access through a software update and moved laterally to compromise many government and private networks.
- Target Data Breach: Hackers accessed Target’s network via a third-party vendor and moved laterally to steal customer credit card data.
These cases show how lateral movement can lead to massive breaches and highlight the importance of strong internal security.
Tools Used to Detect and Prevent Lateral Movement
Security teams use various tools to fight lateral movement:
| Tool Type | Purpose | Examples |
| Endpoint Detection & Response (EDR) | Detect suspicious endpoint activity | CrowdStrike, Carbon Black |
| Network Traffic Analysis | Monitor unusual network flows | Darktrace, Vectra |
| Identity and Access Management (IAM) | Control and audit user permissions | Okta, Microsoft Azure AD |
| Security Information and Event Management (SIEM) | Aggregate and analyze security logs | Splunk, IBM QRadar |
Using these tools together improves your chances of spotting and stopping lateral movement.
Best Practices for Responding to a Lateral Movement Attack
If you suspect lateral movement, quick action is crucial. Follow these steps:
- Isolate Affected Systems: Disconnect compromised devices from the network.
- Identify the Entry Point: Find how the attacker got in to prevent further access.
- Change Credentials: Reset passwords and revoke stolen tokens.
- Conduct a Full Network Scan: Look for other compromised systems.
- Notify Stakeholders: Inform your security team and possibly affected parties.
- Review and Improve Security: Learn from the incident to strengthen defenses.
A clear response plan helps minimize damage and recover faster.
Conclusion
Lateral movement attacks are a serious threat because they let hackers quietly explore and control your network after breaking in. Understanding how these attacks work helps you spot suspicious activity and protect your systems better.
By using strong security measures like network segmentation, multi-factor authentication, and continuous monitoring, you can reduce the risk of lateral movement. Staying informed and prepared is key to keeping your data and systems safe from these stealthy attacks.
FAQs
What is the main goal of a lateral movement attack?
The main goal is to move within a network after initial access to find valuable data or critical systems to exploit or steal.
How do hackers steal credentials for lateral movement?
They use methods like phishing, malware, or exploiting vulnerabilities to capture passwords, hashes, or tokens.
Can multi-factor authentication stop lateral movement?
MFA makes it much harder for attackers to use stolen credentials, significantly reducing lateral movement risks.
What role does network segmentation play in prevention?
It limits attacker movement by dividing the network into smaller, controlled zones, making it harder to spread.
How can I detect lateral movement early?
Look for unusual login patterns, unexpected use of admin tools, and monitor network traffic with security tools like EDR and SIEM.





