What is IoT Botnet
Introduction
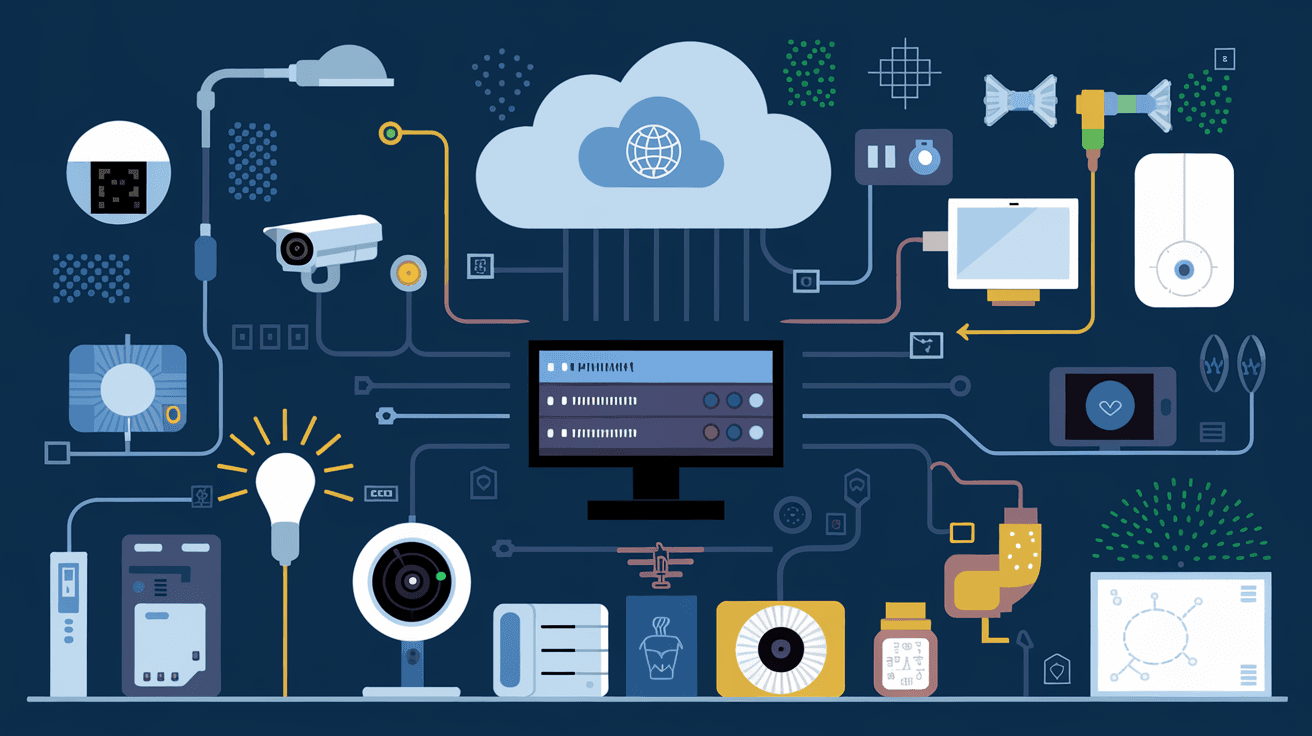
You might have heard about IoT botnets but wonder what they really are and why they matter. If you use smart devices like cameras, thermostats, or even smart fridges, you’re part of the Internet of Things (IoT). These devices make life easier but also open doors for cyber threats like IoT botnets.
In this article, I’ll explain what an IoT botnet is, how it works, and why it’s a growing concern. You’ll also learn practical steps to protect your devices and keep your digital life safe.
What is an IoT Botnet?
An IoT botnet is a network of internet-connected devices infected with malware. These devices, often called “bots” or “zombies,” are controlled remotely by hackers without the owner’s knowledge. The devices in an IoT botnet are usually everyday smart gadgets like security cameras, routers, or smart home appliances.
Here’s how it works:
- Hackers find weak or unprotected IoT devices.
- They infect these devices with malware.
- The infected devices connect to a central command server.
- The hacker controls the entire network to launch attacks or steal data.
Unlike traditional botnets that use computers, IoT botnets exploit the growing number of smart devices that often lack strong security.
How Do IoT Botnets Work?
IoT botnets operate by exploiting vulnerabilities in smart devices. Many IoT devices have weak passwords, outdated software, or unsecured network connections. Hackers scan the internet to find these weak points and infect devices with malware.
Once infected, the devices become part of the botnet and follow commands from the hacker. Common uses of IoT botnets include:
- Distributed Denial of Service (DDoS) attacks: Overloading websites or servers to make them unavailable.
- Spam campaigns: Sending massive amounts of spam emails.
- Data theft: Stealing sensitive information from connected devices.
- Cryptocurrency mining: Using device resources to mine digital currencies without permission.
Because IoT devices are often always online and have stable internet connections, they are perfect for these malicious activities.
Examples of Famous IoT Botnets
Several high-profile IoT botnets have made headlines in recent years. Here are some notable examples:
- Mirai Botnet: One of the most infamous IoT botnets, Mirai infected hundreds of thousands of devices in 2016. It launched massive DDoS attacks that disrupted major websites like Twitter and Netflix.
- Hajime: Unlike Mirai, Hajime was a more stealthy botnet that infected IoT devices but didn’t launch attacks. Instead, it created a peer-to-peer network, possibly to defend against other malware.
- Mozi: This botnet targets routers and IoT devices to build a large network for DDoS attacks. It uses peer-to-peer communication to avoid detection.
These examples show how IoT botnets can cause widespread disruption and highlight the importance of securing your devices.
Why Are IoT Devices Vulnerable?
IoT devices are vulnerable for several reasons:
- Weak or default passwords: Many devices come with factory-set passwords that users don’t change.
- Lack of software updates: IoT devices often don’t receive regular security patches.
- Limited security features: Some devices have minimal security measures due to cost or design.
- Always-on connectivity: Devices are connected 24/7, giving hackers constant access.
- Poor user awareness: Many users don’t know how to secure their smart devices properly.
Because of these factors, IoT devices are easy targets for hackers building botnets.
How to Protect Your Devices from IoT Botnets
You can take several steps to protect your IoT devices from becoming part of a botnet:
- Change default passwords: Use strong, unique passwords for every device.
- Keep software updated: Regularly install firmware and security updates.
- Disable unused features: Turn off services like remote access if you don’t need them.
- Use network segmentation: Separate IoT devices from your main network using guest Wi-Fi.
- Install security software: Use firewalls and antivirus tools that support IoT protection.
- Monitor device activity: Check for unusual behavior or traffic from your devices.
- Buy from reputable brands: Choose devices with good security track records.
Taking these steps reduces the risk of your devices being hijacked by hackers.
The Impact of IoT Botnets on Businesses and Individuals
IoT botnets don’t just affect individual users; they can cause serious problems for businesses and the internet as a whole.
- For businesses: Botnets can disrupt operations by launching DDoS attacks on company websites or services. They can also steal sensitive data or use company devices for illegal activities.
- For individuals: Infected devices can slow down your internet, expose personal information, or even cause financial loss.
- For the internet: Large botnets can take down major websites and services, affecting millions of users worldwide.
Understanding these impacts helps you see why IoT security is critical for everyone.
The Future of IoT Botnets and Security
As IoT devices become more common, IoT botnets are expected to grow in size and sophistication. However, the cybersecurity industry is also evolving to fight back.
- Improved device security: Manufacturers are starting to build stronger security features into IoT devices.
- AI and machine learning: These technologies help detect and block botnet activity faster.
- Regulations and standards: Governments are introducing rules to ensure IoT devices meet minimum security requirements.
- User education: More awareness campaigns teach people how to protect their smart devices.
By staying informed and proactive, you can help reduce the threat of IoT botnets in the future.
Conclusion
Now you know that an IoT botnet is a network of infected smart devices controlled by hackers. These botnets can cause serious harm by launching attacks, stealing data, or disrupting services. The main reason IoT devices are vulnerable is weak security and constant internet connection.
But you’re not powerless. By changing default passwords, updating software, and monitoring your devices, you can protect your smart gadgets from becoming part of a botnet. As IoT technology grows, staying aware and taking simple security steps will keep you safe in our connected world.
FAQs
What devices can be part of an IoT botnet?
Any internet-connected device can be part of an IoT botnet, including smart cameras, routers, smart TVs, thermostats, and even smart home appliances like refrigerators.
How do hackers infect IoT devices?
Hackers infect IoT devices by exploiting weak passwords, outdated software, or security flaws. They scan for vulnerable devices and install malware remotely.
Can IoT botnets be detected easily?
Detecting IoT botnets can be difficult because infected devices often behave normally. However, unusual network traffic or slow internet speeds can be signs of infection.
Are all IoT devices at risk of botnet attacks?
Not all IoT devices are equally at risk. Devices with strong security, regular updates, and proper user settings are less likely to be compromised.
What should I do if I suspect my device is part of a botnet?
If you suspect infection, disconnect the device from the internet, update its software, change passwords, and run security scans. Contact the manufacturer or a cybersecurity expert for help if needed.





