What is Inline Network Encryption
Introduction
You might have heard about network encryption but wonder what inline network encryption means and why it’s important. In today’s digital world, protecting data as it moves across networks is crucial. Inline network encryption is a powerful way to secure your information in real time, preventing hackers from intercepting sensitive data.
In this article, I’ll explain what inline network encryption is, how it works, and why it’s becoming a key part of modern cybersecurity. Whether you’re managing a business network or just curious about data security, understanding this technology will help you keep your information safe.
What is Inline Network Encryption?
Inline network encryption is a method of encrypting data directly as it passes through a network device. Unlike traditional encryption that happens before data leaves a device or after it arrives, inline encryption secures data in real time while it’s moving through the network.
This means the encryption process is embedded “inline” within the network path. Devices like switches, routers, or dedicated encryption appliances handle the encryption and decryption automatically without disrupting the flow of data.
Key Features of Inline Network Encryption
- Real-time encryption: Data is encrypted and decrypted instantly as it travels.
- Transparent to users: The process happens without user intervention.
- Integrated with network devices: Encryption is part of the network hardware or software.
- Protects data in transit: Prevents interception or tampering during transmission.
Inline encryption is especially useful for protecting sensitive information like financial transactions, personal data, or confidential business communications.
How Does Inline Network Encryption Work?
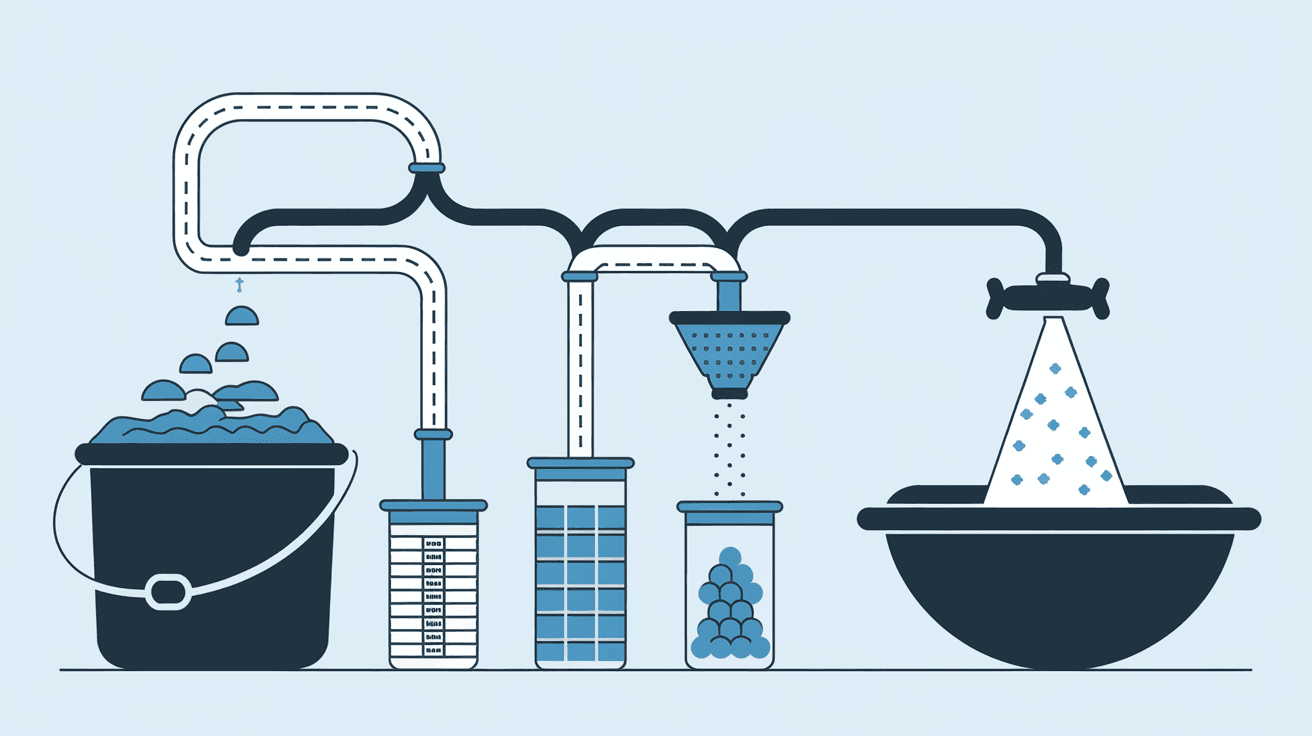
Inline network encryption works by placing an encryption engine directly in the data path. When data packets flow through a network device, the engine encrypts the data before sending it onward. On the receiving end, the device decrypts the data so it can be used normally.
Here’s a simple breakdown of the process:
- Data enters the network device: The device receives unencrypted data.
- Encryption engine activates: The data is encrypted using strong algorithms.
- Encrypted data is transmitted: The data moves securely across the network.
- Receiving device decrypts data: The encrypted data is converted back to its original form.
Common Encryption Algorithms Used
- AES (Advanced Encryption Standard): The most widely used standard for secure encryption.
- TLS (Transport Layer Security): Often used for encrypting data in transit.
- IPsec (Internet Protocol Security): Secures IP communications by authenticating and encrypting each IP packet.
These algorithms ensure that even if someone intercepts the data, they cannot read or alter it without the encryption keys.
Why is Inline Network Encryption Important?
Inline network encryption is critical because it protects data as it moves between devices, which is when it is most vulnerable. Cyberattacks often target data in transit, trying to steal or manipulate information before it reaches its destination.
Benefits of Inline Network Encryption
- Enhanced security: Encrypting data inline reduces the risk of data breaches.
- Compliance with regulations: Many industries require encryption to meet legal standards.
- Minimal latency: Because encryption happens inline, it doesn’t slow down network traffic significantly.
- Simplified management: Centralized encryption in network devices makes it easier to control and monitor.
For businesses, this means safeguarding customer information, intellectual property, and internal communications without sacrificing performance.
Where is Inline Network Encryption Used?
Inline network encryption is used in various environments where data security is a priority. Some common use cases include:
- Data centers: Protecting data moving between servers and storage systems.
- Financial institutions: Securing transactions and sensitive customer data.
- Healthcare: Protecting patient records during transmission.
- Cloud services: Encrypting data between cloud providers and users.
- Telecommunications: Securing voice and data communications over networks.
Many organizations deploy inline encryption in their core network infrastructure to maintain strong security without disrupting operations.
Inline Network Encryption vs. Other Encryption Methods
It’s helpful to understand how inline encryption compares to other types of encryption:
| Encryption Type | When Encryption Happens | Impact on Network Traffic | Use Case Example |
| Inline Network Encryption | During data transit, inline in network devices | Low latency, real-time encryption | Data center traffic protection |
| End-to-End Encryption | At the source and decrypted at the destination | Can add latency, requires key management | Messaging apps, email security |
| Link Encryption | Encrypts data on a single network link | Transparent to higher layers | Securing point-to-point links |
Inline encryption offers a balance of security and performance by encrypting data as it moves through the network, rather than only at the endpoints.
Challenges and Considerations with Inline Network Encryption
While inline network encryption offers many benefits, there are some challenges to keep in mind:
- Hardware costs: Encryption-capable devices can be expensive.
- Key management: Securely handling encryption keys is critical.
- Compatibility: Ensuring encryption works across different network devices and protocols.
- Performance impact: Although minimal, encryption can add some processing overhead.
To address these, organizations often use dedicated encryption appliances or upgrade existing network hardware to support inline encryption efficiently.
How to Implement Inline Network Encryption
If you want to add inline network encryption to your infrastructure, here are some steps to consider:
- Assess your network: Identify critical data flows that need protection.
- Choose encryption technology: Select algorithms and devices that fit your needs.
- Upgrade network devices: Use switches, routers, or appliances with inline encryption support.
- Plan key management: Implement secure methods for generating, storing, and rotating keys.
- Test performance: Monitor network latency and throughput after deployment.
- Train staff: Ensure your IT team understands encryption management and troubleshooting.
By following these steps, you can secure your network traffic without disrupting business operations.
Future Trends in Inline Network Encryption
As cyber threats evolve, inline network encryption continues to advance. Here are some trends shaping its future:
- Integration with AI: Using artificial intelligence to detect anomalies in encrypted traffic.
- Quantum-resistant encryption: Developing algorithms that can withstand quantum computing attacks.
- Cloud-native encryption: Inline encryption built into cloud networking services.
- Automation: Simplifying key management and encryption deployment through automation tools.
These innovations will make inline network encryption more effective and easier to manage, helping organizations stay ahead of cybercriminals.
Conclusion
Inline network encryption is a vital technology for protecting data as it travels across networks. By encrypting data in real time within network devices, it prevents unauthorized access and keeps sensitive information safe. Whether you run a business or manage a network, understanding inline encryption helps you make smarter security decisions.
As cyber threats grow more sophisticated, inline network encryption offers a practical way to secure your data without slowing down your network. Investing in this technology now can save you from costly breaches and compliance issues later. Keep your data safe by embracing inline network encryption as part of your cybersecurity strategy.
FAQs
What devices support inline network encryption?
Many modern routers, switches, and dedicated encryption appliances support inline network encryption. Vendors often provide hardware or software upgrades to enable this feature.
Does inline network encryption affect network speed?
Inline encryption adds minimal latency because it encrypts data in real time within network devices. Properly designed systems maintain high performance.
How is inline network encryption different from VPNs?
VPNs encrypt data between endpoints over public networks, while inline encryption secures data within the network infrastructure itself, often in private or enterprise networks.
Can inline network encryption protect against all cyber threats?
While it protects data in transit, inline encryption should be part of a broader security strategy including endpoint protection, firewalls, and monitoring.
Is inline network encryption required by law?
Certain industries like finance and healthcare mandate encryption of data in transit. Inline encryption helps meet these regulatory requirements efficiently.





