What is Indicators of Compromise Feed
Introduction
If you’re concerned about cybersecurity, you’ve probably heard the term "Indicators of Compromise Feed" or IOC feed. But what exactly is it, and why should you care? In simple terms, an IOC feed is a tool that helps you spot signs of cyberattacks early. It’s like having a security guard who constantly updates you about potential threats.
In this article, I’ll explain what an Indicators of Compromise Feed is, how it works, and why it’s important for protecting your digital world. Whether you’re a business owner or just curious about cyber safety, understanding IOC feeds can help you stay one step ahead of hackers.
What Are Indicators of Compromise (IOCs)?
Indicators of Compromise, or IOCs, are clues that show a system or network might have been attacked. Think of them as footprints left behind by cybercriminals. These clues can be anything unusual or suspicious that signals a breach.
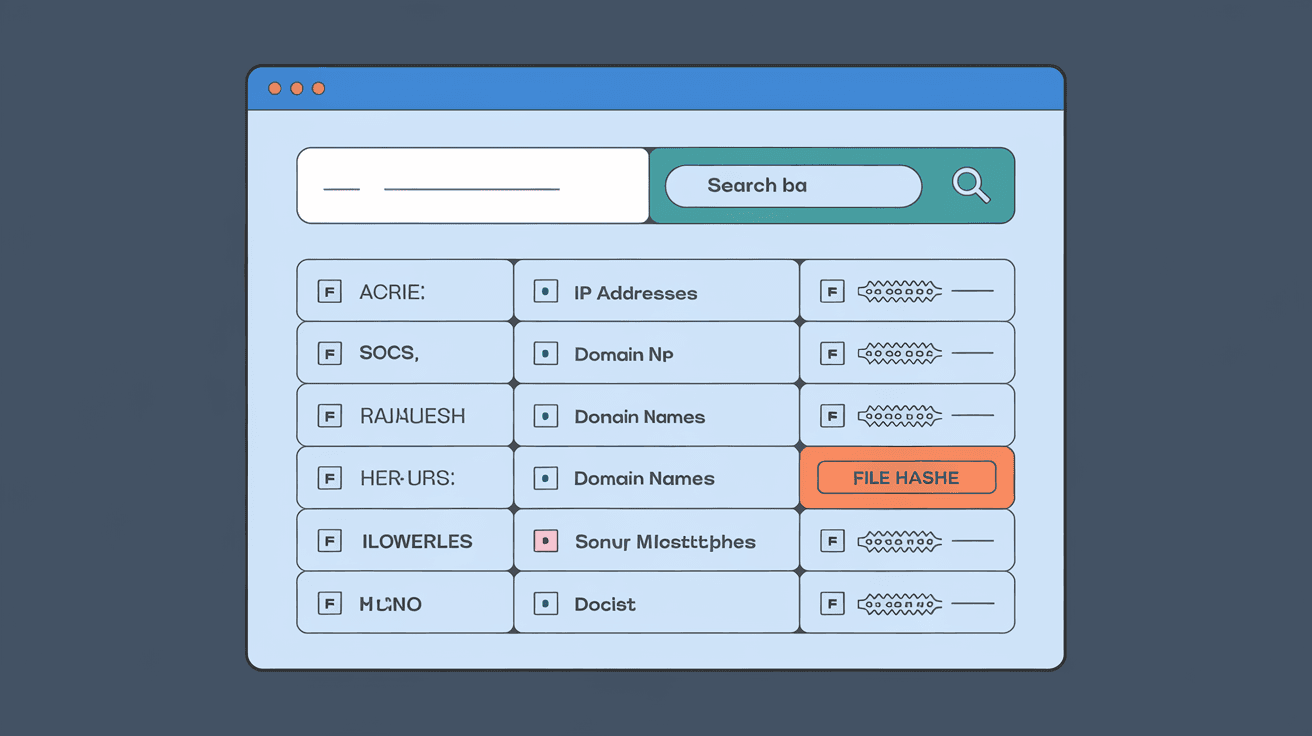
Common Types of IOCs
- Malicious IP addresses: IPs known to be used by hackers.
- Suspicious domain names: Websites linked to phishing or malware.
- File hashes: Unique codes that identify malicious files.
- Unusual network traffic: Data patterns that don’t fit normal behavior.
- Registry changes: Alterations in system settings that indicate tampering.
These indicators help security teams detect threats before they cause serious damage.
What is an Indicators of Compromise Feed?
An Indicators of Compromise Feed is a continuously updated list or stream of IOCs. It provides real-time information about new and existing cyber threats. Think of it as a news feed but focused solely on cybersecurity alerts.
How IOC Feeds Work
- Data Collection: IOC feeds gather data from various sources like security vendors, government agencies, and threat intelligence platforms.
- Aggregation: They combine this data into a single, organized feed.
- Distribution: The feed is shared with organizations and security tools to help detect threats quickly.
- Automation: Many security systems automatically use IOC feeds to scan networks and devices.
By using IOC feeds, you get timely warnings about potential attacks, allowing you to respond faster.
Why Are IOC Feeds Important?
In today’s digital world, cyber threats evolve rapidly. Hackers constantly change their tactics, making it hard to keep up. IOC feeds help by providing up-to-date information on the latest threats.
Benefits of Using IOC Feeds
- Early Detection: Spot threats before they spread.
- Improved Response: Act quickly to contain attacks.
- Better Threat Intelligence: Understand attacker methods.
- Automation: Reduce manual work with automatic scanning.
- Collaboration: Share threat data across organizations.
Using IOC feeds strengthens your security posture and reduces the risk of costly breaches.
How Organizations Use IOC Feeds
Organizations integrate IOC feeds into their cybersecurity tools to enhance threat detection. Here’s how they typically use them:
Integration with Security Tools
- SIEM Systems: Security Information and Event Management tools use IOC feeds to correlate alerts.
- Endpoint Detection and Response (EDR): These tools scan devices for IOC matches.
- Firewalls and Intrusion Detection Systems (IDS): Block or alert on suspicious activity based on IOC data.
- Threat Intelligence Platforms: Analyze and prioritize threats using IOC feeds.
Practical Steps for Using IOC Feeds
- Subscribe to reliable IOC feed providers.
- Configure security tools to consume and act on feed data.
- Regularly update and validate IOC data.
- Train security teams to interpret IOC alerts.
- Combine IOC feeds with other security measures for layered defense.
Types of IOC Feeds Available
There are many IOC feed providers, each offering different types of data. Some are free, while others require subscriptions.
Common IOC Feed Sources
- Open Source Feeds: Free and community-driven, like AlienVault OTX or MISP.
- Commercial Feeds: Paid services offering detailed and verified data, such as FireEye or CrowdStrike.
- Government Feeds: Official alerts from agencies like US-CERT or Europol.
- Industry-Specific Feeds: Tailored to sectors like finance or healthcare.
Choosing the right feed depends on your needs, budget, and security goals.
Challenges and Limitations of IOC Feeds
While IOC feeds are powerful, they’re not perfect. Here are some challenges you might face:
Common Issues
- False Positives: Legitimate activity flagged as malicious.
- Data Overload: Too many indicators can overwhelm security teams.
- Timeliness: Some feeds may not update quickly enough.
- Quality Variance: Not all feeds have accurate or relevant data.
- Integration Complexity: Technical challenges in connecting feeds to tools.
To overcome these, organizations must carefully select feeds, tune detection rules, and combine IOC data with other intelligence.
How to Choose the Right IOC Feed for You
Selecting the best IOC feed depends on your organization’s size, industry, and security maturity.
Factors to Consider
- Relevance: Does the feed cover threats relevant to your environment?
- Accuracy: How reliable is the data?
- Update Frequency: How often is the feed refreshed?
- Format Compatibility: Can your tools easily consume the feed?
- Cost: Does it fit your budget?
- Support and Documentation: Is help available when needed?
Testing multiple feeds and combining them can provide a more comprehensive defense.
Future Trends in IOC Feeds
The world of cybersecurity is always changing, and IOC feeds are evolving too.
Emerging Developments
- AI and Machine Learning: Automate IOC generation and reduce false positives.
- Threat Sharing Communities: More collaboration between organizations.
- Integration with Zero Trust Models: IOC feeds supporting stricter access controls.
- Cloud-Based Feeds: Easier access and scalability.
- Behavioral Indicators: Moving beyond static IOCs to detect suspicious behavior patterns.
These trends will make IOC feeds smarter and more effective in fighting cybercrime.
Conclusion
Understanding what an Indicators of Compromise Feed is can make a big difference in how you protect your digital assets. It’s a powerful tool that gives you early warnings about cyber threats, helping you act before damage occurs. By integrating IOC feeds into your security strategy, you stay informed and ready.
Whether you’re managing a small business or a large enterprise, using IOC feeds is a smart move. They provide timely, actionable intelligence that strengthens your defenses. Keep in mind the challenges and choose feeds that fit your needs. Staying ahead of cyber threats is easier when you have the right information at your fingertips.
FAQs
What is the main purpose of an Indicators of Compromise Feed?
An IOC feed provides real-time data about cyber threats, helping organizations detect and respond to attacks quickly by identifying suspicious activity or malicious files.
How often are IOC feeds updated?
Most IOC feeds update frequently, sometimes multiple times a day, to provide the latest threat information and keep security systems current.
Can IOC feeds prevent cyberattacks completely?
IOC feeds help detect and respond to threats early but cannot prevent all attacks alone. They work best as part of a layered cybersecurity approach.
Are there free IOC feeds available?
Yes, several open-source IOC feeds are available for free, such as AlienVault OTX and MISP, offering valuable threat intelligence for many users.
How do IOC feeds integrate with security tools?
IOC feeds are usually integrated with SIEM, EDR, firewalls, and IDS systems to automatically scan and alert on suspicious indicators within a network or device.





