What is DNS Amplification Attack
Introduction
You might have heard about cyberattacks that can take down websites or networks, but have you ever wondered how they work? One common and powerful type of attack is called a DNS amplification attack. It’s a method hackers use to overwhelm a target by exploiting the Domain Name System (DNS).
In this article, I’ll explain what a DNS amplification attack is, how it operates, and what you can do to protect yourself. Understanding this attack helps you stay safer online and better defend your network from cyber threats.
What is a DNS Amplification Attack?
A DNS amplification attack is a type of Distributed Denial of Service (DDoS) attack. It uses the Domain Name System to flood a target with a massive amount of traffic. The goal is to overwhelm the target’s servers or network, making websites or services unavailable.
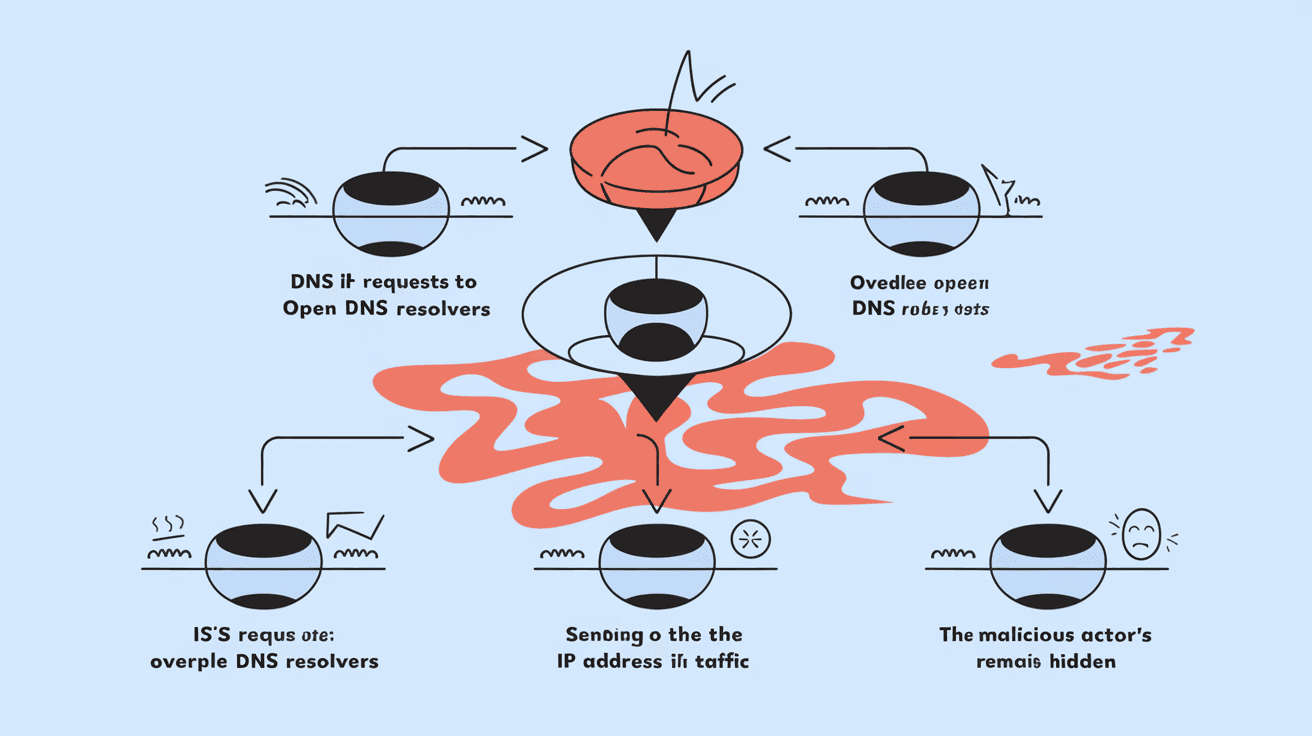
Here’s how it works in simple terms:
- The attacker sends small DNS queries to open DNS servers.
- These queries are crafted to request large responses.
- The DNS servers reply with much bigger responses.
- The replies are sent to the victim’s IP address, not the attacker’s.
- This amplifies the traffic hitting the victim, causing disruption.
Because the attacker’s small requests cause large responses, the attack “amplifies” the amount of data sent to the target. This makes it easier for attackers to cause damage with fewer resources.
How Does DNS Amplification Work?
DNS amplification attacks rely on the way DNS servers respond to queries. DNS servers translate domain names (like example.com) into IP addresses. Some DNS servers are “open resolvers,” meaning they answer queries from any IP address.
Here’s a step-by-step breakdown:
- Attacker finds open DNS resolvers: These servers will respond to queries from anyone.
- Crafts a DNS query: The attacker sends a small query that triggers a large DNS response.
- Spoofs the victim’s IP address: The attacker fakes the source IP in the query to be the victim’s IP.
- DNS server sends large response to victim: The server replies to the victim, not the attacker.
- Victim receives massive traffic: Many DNS servers send large responses, flooding the victim.
The amplification factor can be 50 to 70 times the size of the original request. For example, a 60-byte request might generate a 3,000-byte response. This makes the attack very efficient for attackers.
Why Are DNS Amplification Attacks Dangerous?
DNS amplification attacks are dangerous because they can cause severe disruption with relatively little effort from the attacker. Here are some reasons why:
- High traffic volume: The attack can generate huge amounts of data, overwhelming networks.
- Difficult to trace: The attacker spoofs IP addresses, hiding their identity.
- Exploits legitimate servers: Open DNS resolvers are used without permission.
- Can target any online service: Websites, online games, and even critical infrastructure can be affected.
In recent years, DNS amplification attacks have been used in some of the largest DDoS attacks recorded. For example, attacks exceeding hundreds of gigabits per second have taken down major websites and services.
Common Targets of DNS Amplification Attacks
Attackers often target organizations or services that rely heavily on internet connectivity. Some common targets include:
- E-commerce websites: Disrupting sales and customer access.
- Financial institutions: Causing downtime for online banking.
- Government websites: Interrupting public services.
- Gaming servers: Affecting online gameplay and user experience.
- Internet service providers (ISPs): Impacting large numbers of users.
Because DNS amplification attacks can cause widespread outages, they are a favorite tool for cybercriminals aiming to cause chaos or demand ransom.
How to Detect a DNS Amplification Attack
Detecting a DNS amplification attack early can help you respond quickly and reduce damage. Here are signs to watch for:
- Sudden spike in incoming traffic: A large increase in DNS response packets.
- Unusual DNS traffic patterns: Many DNS responses without corresponding requests.
- Network slowdown or outages: Services become slow or unreachable.
- Alerts from security tools: Firewalls or intrusion detection systems may flag suspicious traffic.
Network monitoring tools and specialized DDoS protection services can help identify these patterns and alert you to an ongoing attack.
How to Protect Against DNS Amplification Attacks
Protecting your network from DNS amplification attacks involves several strategies. Here’s what you can do:
For Network Administrators
- Disable open DNS resolvers: Configure DNS servers to only respond to trusted clients.
- Implement rate limiting: Limit the number of DNS responses sent to a single IP.
- Use DNS response rate limiting (RRL): This technique reduces the impact of amplification.
- Deploy firewalls and intrusion prevention systems: Block suspicious traffic patterns.
- Monitor traffic continuously: Use tools to detect unusual spikes or patterns.
For End Users and Organizations
- Use reputable DNS providers: Choose DNS services that protect against abuse.
- Keep software updated: Patch DNS servers and network devices regularly.
- Educate staff: Train employees on cybersecurity best practices.
- Have a DDoS response plan: Prepare steps to take if an attack occurs.
By combining these measures, you can reduce the risk and impact of DNS amplification attacks.
The Role of Internet Service Providers (ISPs)
ISPs play a crucial role in preventing DNS amplification attacks. They can:
- Filter spoofed IP addresses: Block packets with fake source IPs.
- Monitor traffic for anomalies: Detect and mitigate attacks early.
- Educate customers: Help users secure their networks.
- Collaborate with other ISPs: Share information about threats and coordinate defenses.
Many ISPs now offer DDoS protection services to help customers stay safe from amplification attacks.
Recent Trends in DNS Amplification Attacks
In 2026, DNS amplification attacks continue to evolve. Some recent trends include:
- Use of IoT devices: Attackers exploit insecure Internet of Things devices to launch attacks.
- Increased attack size: Attacks now often exceed 1 terabit per second.
- Multi-vector attacks: Combining DNS amplification with other attack types.
- Improved mitigation tools: New AI-based detection systems help stop attacks faster.
Staying informed about these trends helps you adapt your defenses accordingly.
Conclusion
Now that you understand what a DNS amplification attack is, you can see why it’s such a powerful and dangerous cyber threat. Attackers exploit open DNS servers to flood victims with massive traffic, causing outages and disruption. But with the right knowledge and tools, you can protect your network.
By disabling open resolvers, monitoring traffic, and working with your ISP, you reduce your risk. Staying updated on attack trends and preparing a response plan also helps you stay one step ahead. Remember, cybersecurity is a shared responsibility, and understanding threats like DNS amplification attacks is the first step to staying safe online.
FAQs
What is the main goal of a DNS amplification attack?
The main goal is to overwhelm a target’s network or servers with a flood of traffic, causing denial of service and making websites or services unavailable.
How do attackers spoof IP addresses in DNS amplification attacks?
Attackers fake the source IP address in DNS queries to make responses go to the victim’s IP, hiding their identity and amplifying the attack’s impact.
Can DNS amplification attacks be prevented completely?
While you can’t prevent all attacks, you can greatly reduce risk by securing DNS servers, using rate limiting, and working with ISPs to block spoofed traffic.
Why are open DNS resolvers dangerous?
Open DNS resolvers respond to queries from anyone, allowing attackers to use them to amplify traffic and direct it at victims during attacks.
What tools help detect DNS amplification attacks?
Network monitoring systems, intrusion detection systems, and specialized DDoS protection services can detect unusual DNS traffic patterns indicating an attack.





