What is Digital Network Forensics
Introduction
You might have heard about digital network forensics but wonder what it really means and why it’s important. In today’s world, where cyber threats are everywhere, understanding how experts track and analyze network data is crucial. Digital network forensics helps uncover hidden clues in digital traffic to solve crimes or security breaches.
We’ll explore what digital network forensics is, how it works, and why it plays a vital role in protecting networks and investigating cyber incidents. By the end, you’ll have a clear idea of how this field helps keep our digital world safer.
What Is Digital Network Forensics?
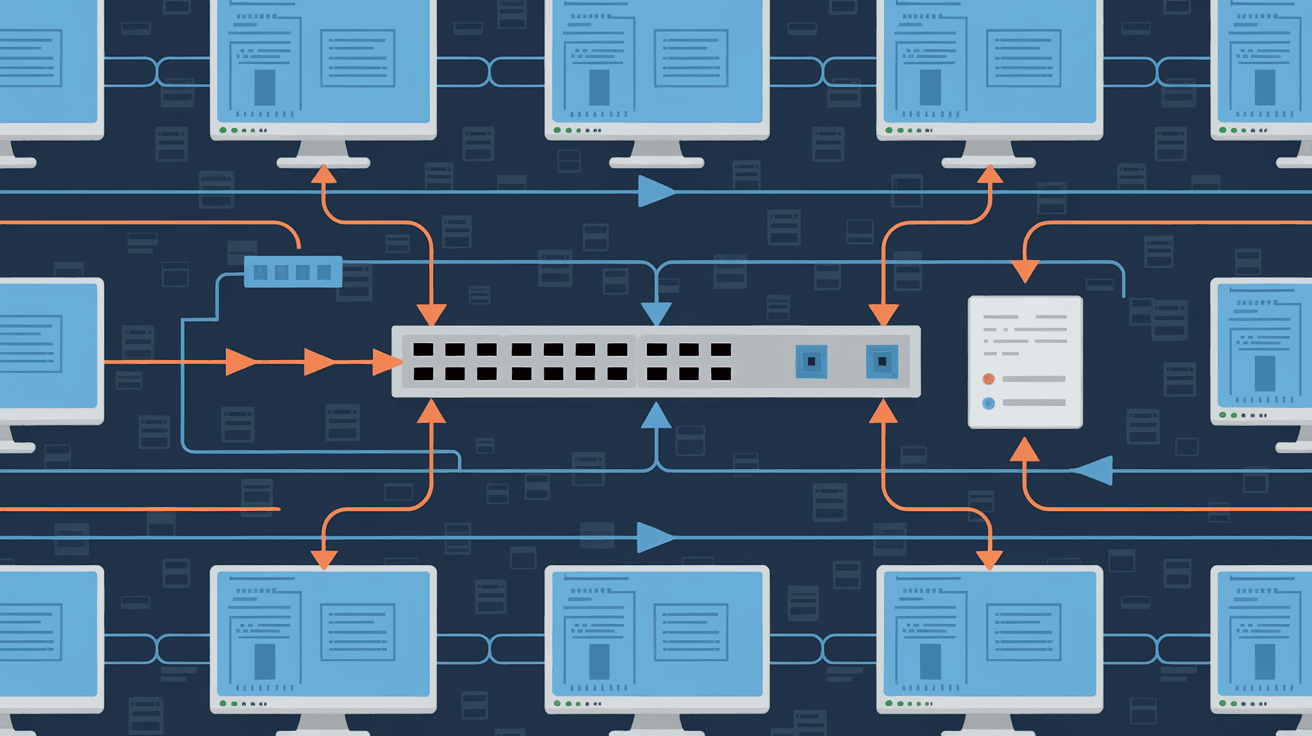
Digital network forensics is a branch of digital forensics focused on monitoring, capturing, and analyzing network traffic data. It involves collecting evidence from computer networks to investigate cybercrimes, security breaches, or unauthorized activities.
Unlike traditional forensics that deal with physical evidence, digital network forensics deals with data packets, logs, and communication patterns. It helps experts trace the source of attacks, understand how intrusions happened, and gather proof for legal cases.
Key Aspects of Digital Network Forensics
- Data Capture: Collecting network traffic in real-time or from stored logs.
- Traffic Analysis: Examining data packets to identify suspicious activities.
- Evidence Preservation: Ensuring data integrity for legal use.
- Incident Reconstruction: Piecing together events leading to a cyber incident.
This process is essential for organizations to respond quickly to threats and for law enforcement to solve cybercrimes.
How Does Digital Network Forensics Work?
Digital network forensics works by capturing and analyzing data that flows through networks. This data includes everything from emails and web traffic to file transfers and instant messages.
Steps Involved in Digital Network Forensics
- Data Collection: Using tools like packet sniffers and network taps to capture data.
- Data Filtering: Removing irrelevant information to focus on suspicious traffic.
- Data Analysis: Inspecting packet headers, payloads, and communication patterns.
- Event Correlation: Linking multiple data points to understand the bigger picture.
- Reporting: Documenting findings for security teams or legal authorities.
Tools Used in Digital Network Forensics
- Wireshark: A popular packet analyzer for capturing and inspecting network traffic.
- Network Forensic Analysis Tools (NFAT): Specialized software for deep traffic analysis.
- Intrusion Detection Systems (IDS): Detect suspicious network behavior.
- Log Management Systems: Collect and analyze logs from various network devices.
These tools help forensic experts uncover details like IP addresses, timestamps, protocols used, and the nature of the data exchanged.
Why Is Digital Network Forensics Important?
Digital network forensics is vital because cyber threats are becoming more complex and frequent. It helps organizations and law enforcement:
- Detect Cyber Attacks: Identify hacking attempts, malware infections, and data breaches.
- Investigate Incidents: Understand how attacks happened and who was responsible.
- Prevent Future Threats: Learn from incidents to improve security measures.
- Support Legal Cases: Provide evidence that can be used in court.
Without digital network forensics, many cybercrimes would go unsolved, and organizations would struggle to protect their data.
Applications of Digital Network Forensics
Digital network forensics is used in various fields to enhance security and solve crimes.
Cybersecurity
Security teams use network forensics to monitor traffic for signs of intrusion or malware. It helps them respond quickly to threats and minimize damage.
Law Enforcement
Police and government agencies rely on network forensics to investigate cybercrimes like hacking, identity theft, and online fraud. It provides crucial evidence for prosecution.
Corporate Investigations
Companies use network forensics to investigate insider threats, data leaks, or policy violations. It helps maintain trust and compliance.
Incident Response
During a security breach, network forensics helps identify the attack vector, scope, and impact, enabling faster recovery.
Challenges in Digital Network Forensics
While digital network forensics is powerful, it faces several challenges:
- Data Volume: Networks generate massive amounts of data, making analysis time-consuming.
- Encryption: Encrypted traffic can hide malicious activities.
- Data Integrity: Ensuring collected data is not altered is critical for legal cases.
- Skill Requirements: Experts need specialized knowledge and tools.
- Privacy Concerns: Monitoring network traffic must balance security with user privacy.
Addressing these challenges requires advanced technology and skilled professionals.
Future Trends in Digital Network Forensics
As cyber threats evolve, digital network forensics is also advancing.
Artificial Intelligence and Machine Learning
AI helps automate data analysis, detect anomalies faster, and predict potential threats.
Cloud Forensics
With more data moving to the cloud, forensic methods are adapting to analyze cloud network traffic.
IoT Forensics
The rise of Internet of Things devices creates new network data sources, requiring specialized forensic techniques.
Enhanced Encryption Handling
New methods are being developed to analyze encrypted traffic without compromising privacy.
These trends will make digital network forensics more efficient and effective in the coming years.
Conclusion
Digital network forensics is a crucial tool in today’s fight against cybercrime. By capturing and analyzing network data, it helps uncover hidden threats, investigate incidents, and support legal actions. Whether you’re a security professional or just curious, understanding this field shows how digital evidence can protect our online world.
As cyber threats grow, digital network forensics will continue to evolve, using new technologies to stay ahead. Keeping networks safe depends on experts who can trace digital footprints and reveal the truth behind cyber incidents.
FAQs
What is the main goal of digital network forensics?
The main goal is to capture and analyze network data to detect, investigate, and prevent cybercrimes or security breaches.
How is digital network forensics different from traditional forensics?
Digital network forensics focuses on network data and traffic, while traditional forensics deals with physical evidence like fingerprints or DNA.
Can digital network forensics be used in real-time?
Yes, many tools allow real-time monitoring and analysis to quickly detect and respond to threats.
What types of data are analyzed in digital network forensics?
Data includes network packets, logs, communication patterns, IP addresses, timestamps, and protocols.
Is digital network forensics legal?
Yes, but it must follow laws and regulations regarding privacy and data protection to ensure evidence is admissible in court.





