What is DDoS (Distributed Denial of Service)
Introduction
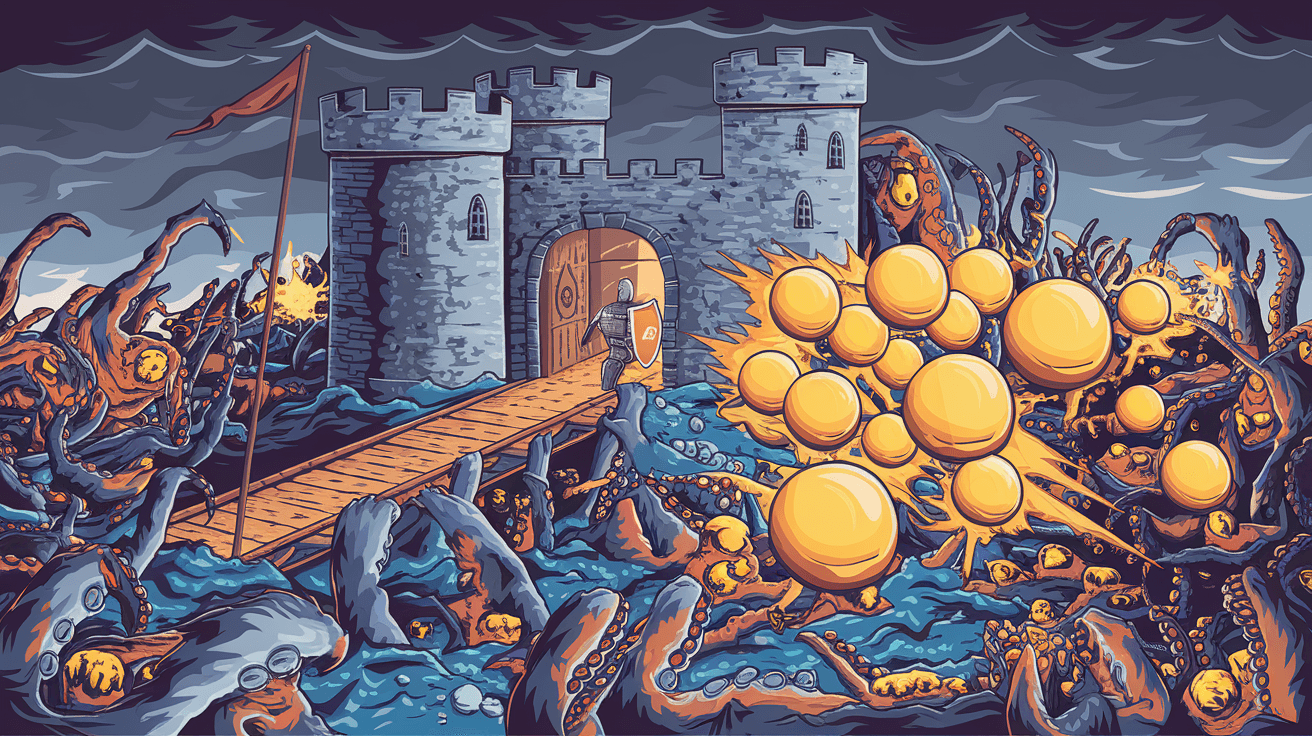
You’ve probably heard about DDoS attacks in the news or tech discussions. But what exactly is a DDoS, and why should you care? Understanding Distributed Denial of Service attacks is important because they can disrupt websites, apps, and online services you use every day.
In this article, I’ll explain what a DDoS attack is, how it works, and what you can do to protect yourself or your business. Whether you’re a casual internet user or managing a website, knowing about DDoS helps you stay safe online.
What is a DDoS Attack?
A DDoS, or Distributed Denial of Service, attack is a cyberattack where multiple computers flood a target system with traffic. The goal is to overwhelm the target’s resources so it can’t respond to legitimate users. This causes the website or service to slow down or crash.
Unlike a regular Denial of Service (DoS) attack, which comes from one source, a DDoS attack uses many sources. These sources are often compromised devices controlled by hackers, called a botnet. This makes DDoS attacks harder to stop.
How Does a DDoS Attack Work?
- Botnet Creation: Hackers infect many devices with malware, turning them into bots.
- Command and Control: The attacker sends commands to the botnet to start the attack.
- Traffic Flood: Bots send massive amounts of traffic to the target.
- Resource Exhaustion: The target’s servers or network get overwhelmed.
- Service Disruption: Legitimate users can’t access the service.
This flood of traffic can take many forms, such as sending too many connection requests or overwhelming the bandwidth.
Types of DDoS Attacks
DDoS attacks come in different types depending on what part of the system they target. Here are the main categories:
1. Volume-Based Attacks
These attacks focus on flooding the target with huge amounts of data to consume bandwidth. Examples include:
- UDP Flood: Sends many User Datagram Protocol packets.
- ICMP Flood: Sends many ping requests.
- DNS Amplification: Uses vulnerable DNS servers to amplify traffic.
2. Protocol Attacks
These attacks exploit weaknesses in network protocols to exhaust server resources. Examples include:
- SYN Flood: Sends many connection requests but never completes them.
- Ping of Death: Sends malformed packets to crash systems.
- Smurf Attack: Uses broadcast addresses to amplify traffic.
3. Application Layer Attacks
These attacks target the application itself, like a website or API, by sending requests that look legitimate but overload the system. Examples include:
- HTTP Flood: Sends many HTTP requests.
- Slowloris: Opens many connections and holds them open.
- Zero-day DDoS: Exploits unknown vulnerabilities.
Why Do Attackers Use DDoS?
Attackers launch DDoS attacks for several reasons:
- Extortion: Threaten businesses to pay ransom to stop attacks.
- Competition: Disrupt competitors’ services.
- Hacktivism: Protest or promote political causes.
- Distraction: Mask other cyberattacks like data breaches.
- Revenge: Target organizations out of spite.
Understanding the motive helps in preparing the right defense.
How to Detect a DDoS Attack
Detecting a DDoS attack early is crucial to minimize damage. Signs include:
- Sudden spike in traffic from many IP addresses.
- Slow or unavailable website.
- Unusual traffic patterns, like many requests to a single page.
- Alerts from security tools or hosting providers.
Using monitoring tools and traffic analysis helps spot attacks quickly.
Protecting Against DDoS Attacks
You can take several steps to protect your online services from DDoS attacks:
1. Use a Content Delivery Network (CDN)
CDNs distribute your content across many servers worldwide. They absorb traffic spikes and filter malicious requests.
2. Deploy Web Application Firewalls (WAF)
WAFs filter and block malicious traffic before it reaches your servers. They can detect suspicious patterns and stop attacks.
3. Rate Limiting
Limit the number of requests a user or IP can make in a given time. This helps prevent flooding.
4. Network Security Measures
- Use anti-DDoS hardware and software.
- Configure routers and firewalls to drop suspicious traffic.
- Use blacklists to block known malicious IPs.
5. Cloud-Based DDoS Protection Services
Services like Cloudflare, Akamai, and AWS Shield specialize in DDoS mitigation. They offer scalable protection and quick response.
6. Have an Incident Response Plan
Prepare a plan that includes:
- Contacting your ISP or hosting provider.
- Switching to backup servers.
- Communicating with customers.
Real-World Examples of DDoS Attacks
DDoS attacks have caused major disruptions worldwide. Here are some notable cases:
- GitHub Attack: In 2026, GitHub faced a record-breaking 3.5 Tbps attack using a new DNS amplification method. Their mitigation systems absorbed the traffic, keeping the site online.
- Financial Sector: Banks often face DDoS attacks aiming to disrupt online banking services, especially during peak hours.
- Gaming Industry: Online games like Fortnite and League of Legends regularly experience DDoS attacks during tournaments to disrupt gameplay.
These examples show how serious and widespread DDoS threats are.
The Future of DDoS Attacks and Defense
As technology evolves, so do DDoS attacks. Here’s what to expect:
- More IoT Botnets: With billions of connected devices, attackers have more targets to build botnets.
- AI-Powered Attacks: Attackers may use AI to create smarter, adaptive attacks.
- Improved Defense: AI and machine learning will also help detect and block attacks faster.
- Stronger Regulations: Governments may enforce stricter cybersecurity laws to combat DDoS.
Staying informed and updating defenses is key to keeping up with these changes.
Conclusion
Now you know that a DDoS attack is a coordinated effort to overwhelm a website or online service with traffic. These attacks can cause serious disruptions but understanding how they work helps you prepare. Whether you run a website or just use the internet, knowing about DDoS is important for online safety.
Protecting against DDoS involves a mix of technology, planning, and vigilance. Using tools like CDNs, firewalls, and cloud services can keep your services running smoothly. Remember, the internet is always changing, so staying updated on threats and defenses is your best strategy.
FAQs
What is the difference between DoS and DDoS attacks?
A DoS attack comes from a single source, while a DDoS attack uses many devices (a botnet) to flood the target, making it harder to stop.
Can a DDoS attack cause permanent damage?
DDoS attacks mainly cause downtime and slow service. They don’t usually damage hardware but can lead to financial loss and reputation damage.
How long do DDoS attacks usually last?
Attack duration varies from minutes to days. Some attacks are short bursts, while others persist until the attacker stops or defenses kick in.
Are IoT devices vulnerable to DDoS attacks?
Yes, many IoT devices have weak security and can be hijacked to form botnets used in DDoS attacks.
Can individuals protect themselves from DDoS attacks?
Individuals can protect themselves by using strong passwords, updating devices, and avoiding suspicious downloads to prevent their devices from becoming part of a botnet.





