What is Carbanak Attack
Introduction
You might have heard about the Carbanak attack and wondered what it really means. It’s one of the most notorious cyberattacks targeting banks and financial institutions worldwide. Understanding what Carbanak is can help you grasp how cybercriminals steal millions and how you can protect your money and data.
In this article, I’ll explain what the Carbanak attack is, how it works, and why it’s so dangerous. We’ll also look at how organizations defend themselves against it. By the end, you’ll have a clear picture of this cyber threat and what it means for you.
What is the Carbanak Attack?
The Carbanak attack is a sophisticated cybercrime campaign that targets banks and financial institutions. It was first discovered around 2014 and quickly became infamous for stealing over a billion dollars globally. The attackers use malware named "Carbanak" to infiltrate bank systems and manipulate them to transfer money illegally.
This attack is not just about hacking into a system; it involves deep infiltration and control over bank operations. The criminals behind Carbanak are highly skilled and patient. They spend weeks or even months inside a bank’s network, learning how it works before making their move.
Key Features of Carbanak Attack
- Targets banks, ATMs, and financial institutions.
- Uses malware to gain control of internal systems.
- Can manipulate bank software to transfer money.
- Often involves social engineering to trick employees.
- Results in large-scale theft, sometimes over $1 billion.
How Does the Carbanak Attack Work?
The Carbanak attack follows a multi-step process that allows criminals to bypass security and steal money without immediate detection. Here’s how it typically unfolds:
1. Initial Infection
Attackers send phishing emails to bank employees. These emails contain malicious attachments or links. When an employee opens the attachment or clicks the link, the Carbanak malware installs itself on the employee’s computer.
2. Network Reconnaissance
Once inside, the malware spreads across the bank’s network. It collects information about the bank’s systems, software, and employees. The attackers study how the bank operates, including how money transfers are processed.
3. Gaining Control
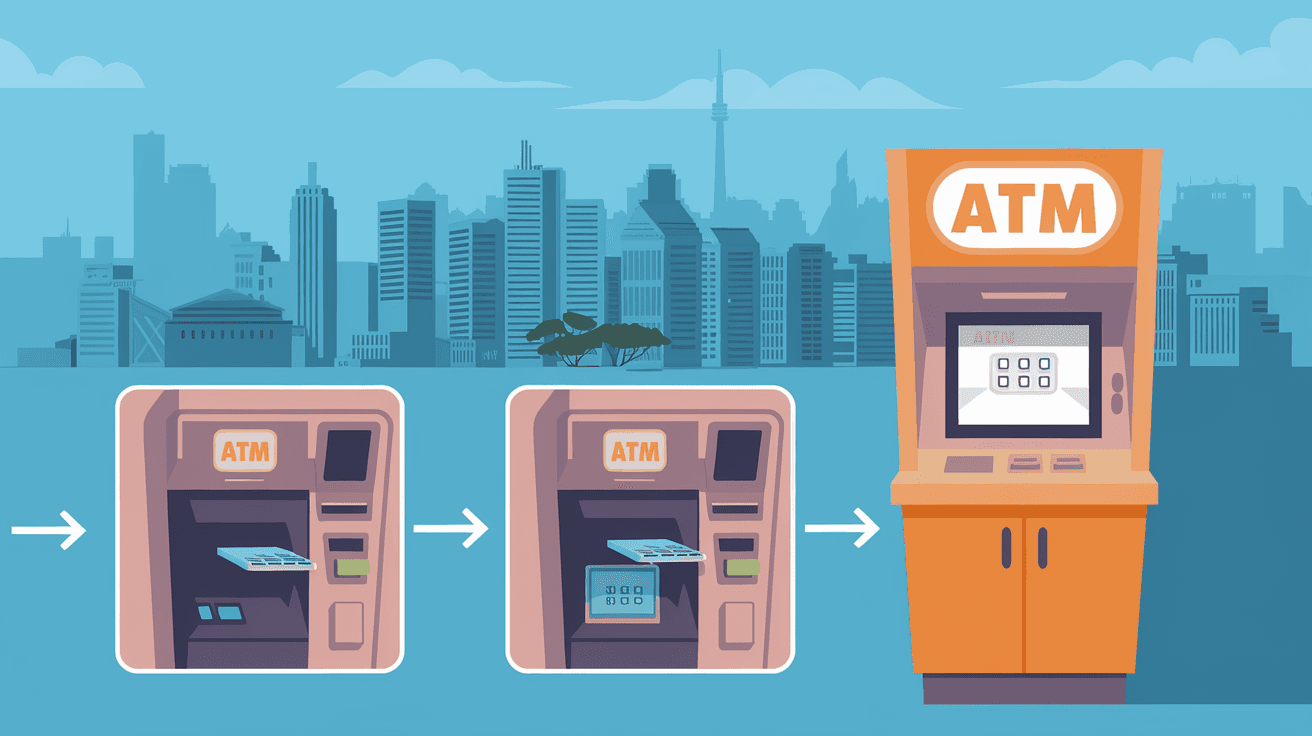
After gathering enough information, the attackers use the malware to take control of key systems. They can manipulate bank software, access databases, and even control ATMs remotely.
4. Money Theft
The attackers then instruct the bank’s systems to transfer money to accounts they control. They can also command ATMs to dispense cash at specific times, which accomplices collect. This method allows them to steal large sums without raising immediate suspicion.
5. Covering Tracks
Finally, the attackers erase logs and hide their presence to avoid detection. This makes it difficult for banks to trace the attack or recover stolen funds quickly.
Why is the Carbanak Attack So Dangerous?
Carbanak is dangerous because it targets the core of financial institutions. Unlike simple hacks that steal data, Carbanak steals actual money by controlling bank operations. This makes it a direct threat to the financial system.
Reasons for Its Danger
- High Financial Impact: Carbanak has stolen over $1 billion from banks worldwide.
- Sophistication: The attack uses advanced malware and social engineering.
- Stealth: It remains undetected for long periods, sometimes months.
- Wide Reach: It has affected banks in over 40 countries.
- Complexity: It manipulates multiple systems, including ATMs and SWIFT transfers.
Because of these factors, Carbanak is considered one of the most successful and damaging cybercrime campaigns in history.
How Can Banks Protect Themselves from Carbanak?
Protecting against Carbanak requires a combination of technology, training, and vigilance. Banks must strengthen their defenses to detect and stop such attacks early.
Key Protection Measures
- Employee Training: Teach staff to recognize phishing emails and suspicious links.
- Advanced Malware Detection: Use security software that can detect and block Carbanak malware.
- Network Segmentation: Separate critical systems to limit malware spread.
- Regular Audits: Conduct frequent security checks and monitor unusual activity.
- Multi-Factor Authentication: Require multiple verification steps for sensitive operations.
- Incident Response Plans: Prepare clear procedures to respond quickly if an attack occurs.
By combining these measures, banks can reduce the risk of falling victim to Carbanak or similar attacks.
Examples of Carbanak Attacks in Action
Several high-profile cases have shown how Carbanak operates in real life. Here are a few examples:
- European Banks: Attackers used Carbanak to steal millions by controlling ATMs to dispense cash at specific times.
- Asian Financial Institutions: The malware was used to manipulate internal bank software to transfer funds to fake accounts.
- Global Reach: The attack affected banks in countries like the US, Russia, China, and Spain, showing its worldwide impact.
These examples highlight how versatile and dangerous Carbanak can be.
What Makes Carbanak Different from Other Cyberattacks?
Carbanak stands out because it targets the entire banking process, not just data. Many cyberattacks focus on stealing customer information or disrupting services. Carbanak goes further by directly stealing money through system manipulation.
Differences Include:
- Direct Financial Theft: Instead of stealing data, it steals money.
- Long-Term Infiltration: Attackers stay inside networks for months.
- Use of Social Engineering: It tricks employees to gain access.
- Control Over ATMs: It can command machines to dispense cash remotely.
- Complex Malware: The Carbanak malware is highly advanced and adaptable.
This combination makes Carbanak a unique and serious threat.
How Has the Cybersecurity Community Responded?
Since Carbanak’s discovery, cybersecurity experts have worked hard to understand and combat it. They have developed tools to detect the malware and shared information globally to warn banks.
Community Actions
- Threat Intelligence Sharing: Banks and security firms share data on Carbanak indicators.
- Improved Detection Tools: New antivirus and monitoring software can spot Carbanak behavior.
- Law Enforcement Cooperation: International agencies collaborate to track and arrest attackers.
- Awareness Campaigns: Educating employees about phishing and malware risks.
These efforts have helped reduce Carbanak’s impact, but the threat remains.
Conclusion
The Carbanak attack is a powerful example of how cybercriminals can exploit banks to steal money directly. Its combination of malware, social engineering, and system control makes it a serious threat to financial institutions worldwide. Understanding how it works helps you see why banks must stay vigilant.
If you work in banking or handle financial data, knowing about Carbanak can help you recognize risks and support security efforts. For everyone else, it’s a reminder of the importance of cybersecurity in protecting our money and information. Staying informed and cautious is the best defense against attacks like Carbanak.
FAQs
What type of malware is used in the Carbanak attack?
Carbanak uses a sophisticated Trojan malware designed to infiltrate bank systems, gather information, and control operations like money transfers and ATM commands.
How do attackers initially infect a bank’s network with Carbanak?
They typically use phishing emails with malicious attachments or links that, when opened by employees, install the Carbanak malware on their computers.
Can Carbanak attacks be detected early?
Yes, with advanced malware detection tools and network monitoring, banks can identify unusual activities and stop the attack before major damage occurs.
Has Carbanak been linked to any specific hacker groups?
While the exact groups remain unclear, cybersecurity experts believe Carbanak is operated by highly skilled cybercriminal organizations focused on financial theft.
What should employees do to prevent Carbanak infections?
Employees should avoid opening suspicious emails or attachments, report unusual system behavior, and follow security training to recognize phishing attempts.





